Key Takeaways
- Reentrancy attacks exploit recursive external calls to drain contract funds before balances are updated, and MLM payout systems are especially vulnerable because of their multi-level distribution logic.
- Integer overflow and underflow bugs can let attackers inflate referral bonuses or manipulate reward balances, though Solidity 0.8+ now includes built-in protections against these issues.
- The DAO hack of 2016 remains the most cited reentrancy exploit in blockchain history, resulting in a loss of roughly $60 million in ETH and eventually splitting the Ethereum chain.
- Developers should follow the Checks-Effects-Interactions pattern and use tools like OpenZeppelin’s ReentrancyGuard to prevent recursive call exploits in MLM contracts.
- Regular third-party security audits, penetration testing, time locks, and withdrawal caps are non-negotiable for any serious crypto MLM software platform.
- Secure smart contract architecture is not just a technical concern. It directly affects user trust, platform reputation, and long-term business sustainability.
Introduction: Why Smart Contract Security Should Be Your Top Priority in Crypto MLM
Blockchain-based MLM platforms have grown rapidly over the past five years. Businesses that once relied on manual tracking and centralized databases are now shifting toward decentralized models where smart contracts handle everything from user registration to commission payouts. According to Wikipedia’s overview of smart contracts, these self-executing programs run on blockchains like Ethereum and automatically enforce the terms of an agreement without any middleman.
That sounds great on paper. But here is the thing most platform owners overlook: smart contracts are only as safe as the code behind them. And in the MLM space, where contracts handle complex referral trees, tiered commissions, and automated fund distribution, the attack surface is significantly larger than a typical DeFi application.
Two of the most dangerous vulnerabilities that plague MLM smart contracts are reentrancy attacks and integer overflow/underflow exploits. Both have caused millions of dollars in losses across the blockchain industry. And both are entirely preventable if you know what you are doing.
Having worked on crypto MLM development solutions for over eight years, our team has audited and built dozens of MLM smart contracts across Ethereum, BNB Chain, Polygon, and Tron. This article breaks down exactly how these attacks work, why MLM platforms are particularly exposed, and what developers and business owners need to do to protect their platforms.
If you are evaluating or building a blockchain MLM system, this is something you cannot afford to ignore. For a broader understanding of how blockchain fits into MLM, you might also want to read our guide to blockchain MLM networks.
Understanding MLM Smart Contracts: How They Work Under the Hood
Before we get into the attacks themselves, it helps to understand what MLM smart contracts actually do and why their structure creates unique security challenges.
In a traditional MLM business, a central server manages the user hierarchy, calculates commissions at each level, and processes withdrawals. When you move this logic onto a blockchain, a smart contract takes over all of those responsibilities. Users interact directly with the contract. The contract stores the referral tree, tracks earnings, and sends payouts automatically.
Most crypto MLM contracts handle these core functions: user registration and placement within the network structure, referral bonus calculations across multiple levels, automated commission distribution whenever a new participant joins or makes a purchase, and fund withdrawal mechanisms that let users claim their earnings.
The challenge is that all of this logic runs on-chain. Every function call, every state change, and every ETH or token transfer is visible and executable by anyone. A single bug in the commission distribution logic or the withdrawal function can be exploited repeatedly, sometimes within seconds.
Common MLM contract structures include binary plans (two legs per user), matrix plans (fixed-width, fixed-depth grids), and unilevel plans (unlimited width, limited depth). Each one has its own payout rules, and each one introduces specific vulnerabilities. For a deeper dive into how these blockchain-based MLM networks function, we have covered the topic in detail separately.
What Is a Reentrancy Attack? Breaking Down the Mechanism
A reentrancy attack happens when an external contract calls back into the vulnerable contract before the first execution is finished. Think of it like this: you walk into a bank, ask for a withdrawal, and before the teller updates your balance, you walk up to another window and make the same withdrawal again. And again. And again. Each time, the bank thinks you still have the original balance because it has not been updated yet.
In Solidity, this typically occurs when a contract sends ETH to an external address using a low-level call, and the receiving address is a malicious contract with a fallback function. That fallback function immediately calls the withdrawal function again. Since the original contract has not yet updated the sender’s balance (the state change happens after the external call), the attacker can keep draining funds in a loop.
Here is a simplified version of how the vulnerable code looks:
// VULNERABLE CODE - Do not use
function withdraw() public {
uint balance = balances[msg.sender];
require(balance > 0);
// External call happens BEFORE state update
(bool success, ) = msg.sender.call{value: balance}("");
require(success);
// State update happens AFTER external call
balances[msg.sender] = 0;
}The attacker deploys a contract whose fallback function calls withdraw() again. Since balances[msg.sender] has not been set to zero yet, each recursive call passes the require(balance > 0) check.
The DAO Hack: The Incident That Changed Ethereum Forever
The most well-known reentrancy attack happened in June 2016 against The DAO, a decentralized autonomous organization built on Ethereum. An attacker exploited a reentrancy vulnerability in the fund withdrawal function and drained approximately 3.6 million ETH, worth around $60 million at the time. The fallout was so severe that the Ethereum community decided to hard fork the entire blockchain to reverse the damage, which is how Ethereum Classic was born.
That event happened almost a decade ago, but the same class of vulnerability still shows up in contracts today, especially in less audited projects like some MLM platforms.
Why MLM Payout Systems Are Particularly Vulnerable
MLM contracts process payouts across multiple levels of a referral chain. When a new user joins, the contract might distribute commissions to five, ten, or even fifteen upline members in a single transaction. Each of those distributions involves an external call. If any of those recipients is a malicious contract, the entire payout function can be reentered.
The problem gets worse with structures like forced matrix plans, where the contract automatically places users and triggers cascading payouts. More external calls mean more entry points for an attacker.

Fig 1: How a reentrancy attack exploits the withdrawal function in an MLM smart contract through recursive external calls.
What Is an Integer Overflow and Underflow Attack?
Integer overflow and underflow are arithmetic bugs that occur when a number exceeds the maximum or minimum value a variable can hold. In older versions of Solidity (before 0.8.0), unsigned integers (uint256) would silently wrap around when they exceeded their limits.
An overflow happens when you add to a number that is already at its maximum value. Instead of throwing an error, it wraps back to zero. An underflow is the opposite. If you subtract from zero, instead of getting a negative number (which unsigned integers cannot represent), you get an astronomically large number.
For context, a uint256 variable can hold values from 0 to 2^256 minus 1. That upper limit is a number with 78 digits. If a balance hits that ceiling and you add even 1, it wraps back to zero. If a balance is 0 and you subtract 1, it jumps to that 78-digit maximum. Investopedia’s explanation of smart contracts touches on how these self-executing agreements depend entirely on the accuracy of their underlying code.
How Attackers Use This in MLM Contracts
In an MLM contract, overflow and underflow bugs can appear in commission calculations, balance tracking, and reward distribution. For example, if an attacker can trigger an underflow on their withdrawal amount, they could end up with a balance that appears to be nearly unlimited. Or if the referral bonus calculation overflows, it could wrap around and give a user zero rewards instead of what they earned.
Imagine a contract that calculates a level bonus like this: bonus = userInvestment * bonusPercentage / 100. If userInvestment * bonusPercentage overflows, the resulting bonus could be a tiny fraction of what it should be, or it could be zero. In some cases, an attacker could manipulate inputs to make the overflow work in their favor.
Modern Solidity Protections
Starting with Solidity version 0.8.0 (released in December 2020), the compiler automatically checks for overflow and underflow and reverts the transaction if either occurs. This was a major improvement. However, contracts written in older versions or those that use the unchecked block for gas optimization are still at risk. Any MLM platform running on legacy code without proper SafeMath usage is a ticking time bomb.
Reentrancy vs. Overflow Attacks: A Side-by-Side Comparison
Understanding the differences between these two attack types is critical for prioritizing your security efforts. Here is a quick comparison.
| Parameter | Reentrancy Attack | Overflow/Underflow Attack |
|---|---|---|
| Attack Vector | Recursive external calls before state updates | Arithmetic manipulation of integer variables |
| Primary Target | Withdrawal and payout functions | Balance tracking, commission calculations |
| Impact | Direct fund drainage from the contract | Inflated or zeroed balances and rewards |
| Detection Difficulty | Moderate (visible in transaction patterns) | Hard (may appear as legitimate transactions) |
| Relevant Solidity Versions | All versions (still relevant today) | Mainly pre-0.8.0 or unchecked blocks |
| Prevention Complexity | Requires careful code patterns and guards | Largely solved by Solidity 0.8+ compiler |
| Risk in MLM Contracts | Very High (multi-level payouts = multiple external calls) | High in legacy contracts, moderate in newer ones |
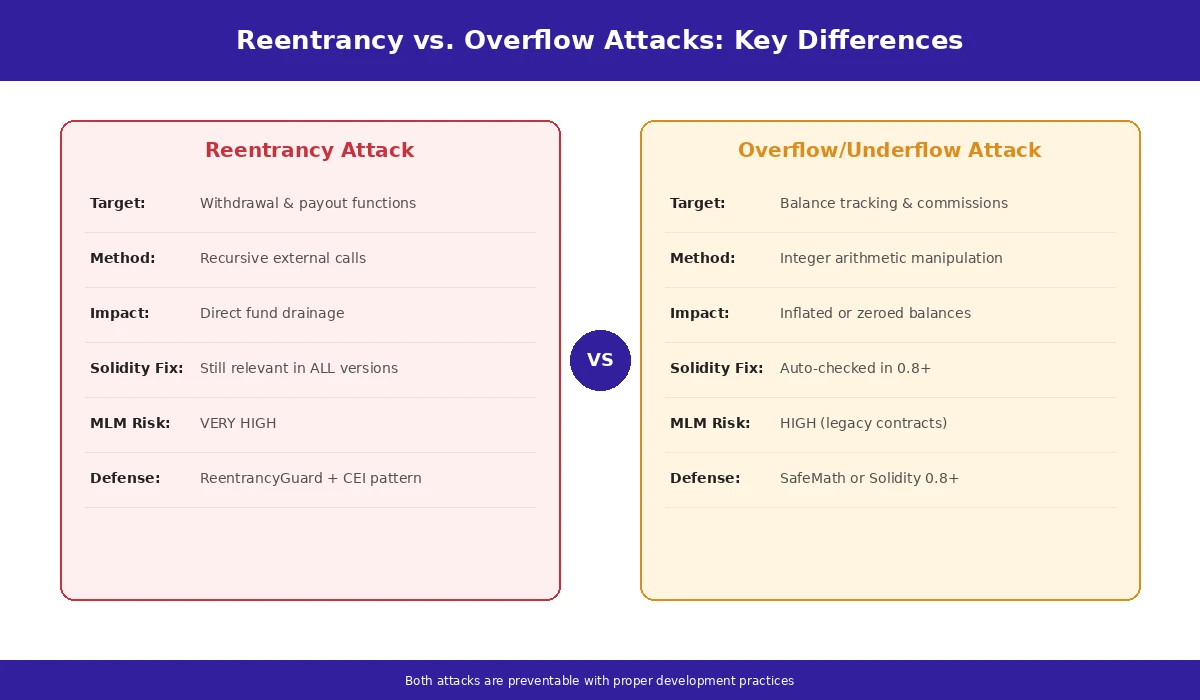
Fig 2: Reentrancy vs. overflow attacks compared across key parameters relevant to MLM smart contract security.
How These Attacks Specifically Target MLM Business Models
MLM smart contracts are not generic token contracts. They carry specialized business logic that creates unique attack opportunities. Let us walk through the specific ways reentrancy and overflow exploits target MLM systems.
Exploiting Referral Bonus Loops
When a user joins an MLM platform, the contract typically loops through the referral chain and sends a percentage of the join amount to each upline member. If this loop sends ETH via external calls and does not follow safe coding patterns, a malicious upline address (a contract, not a regular wallet) can reenter the bonus distribution function and claim its share multiple times before the loop completes.
In platforms where trustless MLM payouts are a selling point, this kind of exploit completely undermines the promise of fair, automated distribution.
Manipulating Level Income Distributions
Level income in MLM means you earn a percentage from users up to a certain depth below you. The contract calculates these percentages for each level and distributes accordingly. Overflow vulnerabilities in these calculations can result in wildly inaccurate payouts. An attacker who understands the math can craft transactions that cause specific levels to receive inflated rewards while others get nothing.
Draining Contract Funds Through Payout Flaws
The most direct damage comes from reentrancy on the main withdrawal function. If the contract holds pooled funds (which most MLM contracts do), a single reentrancy exploit can drain the entire pool. We have seen contracts in the wild where one attacker emptied 95% of the contract balance in a single transaction because the withdrawal function did not have a reentrancy guard.
Vulnerabilities in Matrix and Binary Plans
Matrix plans place users in fixed positions, and binary plans split the network into two legs. Both structures involve automated placement and spillover logic that triggers additional payouts. The more complex the placement algorithm, the more external calls the contract makes, and the larger the attack surface becomes. To understand how distributed ledger technology powers MLM systems and why these structures matter, we have written a dedicated breakdown.
Real-World Smart Contract Breaches: Lessons from the Industry
The blockchain space has seen billions of dollars lost to smart contract exploits. While not all of these were MLM platforms specifically, the vulnerabilities are the same, and the lessons apply directly.
| Incident | Year | Attack Type | Estimated Loss | Key Lesson |
|---|---|---|---|---|
| The DAO | 2016 | Reentrancy | ~$60 million | Always update state before external calls |
| Beauty Chain (BEC) | 2018 | Integer Overflow | Billions in tokens | Use SafeMath or Solidity 0.8+ |
| Fei Protocol / Rari Capital | 2022 | Reentrancy | ~$80 million | Even audited contracts need continuous review |
| Cream Finance | 2021 | Reentrancy + Flash Loan | ~$130 million | Complex integrations multiply attack vectors |
The financial damage in these incidents is obvious. But the reputational damage is often worse. Users lose trust instantly. In the MLM space, where participant confidence drives the entire business model, a single exploit can collapse an entire network overnight. Platforms that neglect security often never recover.
Our agency has been involved in post-breach analysis for several crypto MLM platforms over the years. In almost every case, the vulnerability was something that could have been caught with a proper audit before deployment. That is not a hindsight observation. It is a pattern we have seen repeatedly across eight-plus years of working in this space.
Protect Your MLM Platform from Smart Contract Exploits
Do not wait for a breach to take security seriously. Our team builds and audits MLM smart contracts with battle-tested patterns that block reentrancy, overflow, and other critical vulnerabilities.
Prevention Techniques Every Developer Must Implement
Preventing reentrancy and overflow attacks is not guesswork. There are well-established techniques that have been proven effective across thousands of production contracts. Here is what developers building crypto MLM development solutions need to implement.
The Checks-Effects-Interactions Pattern
This is the single most important coding pattern for preventing reentrancy. The idea is simple: perform all checks first (require statements), then update the contract state (effects), and only then make external calls (interactions). By the time the external call happens, the state already reflects the withdrawal, so a reentrant call will fail the initial check.
// SAFE CODE - Checks-Effects-Interactions
function withdraw() public {
uint balance = balances[msg.sender];
require(balance > 0); // CHECK
balances[msg.sender] = 0; // EFFECT (state update first)
(bool success, ) = msg.sender.call{value: balance}(""); // INTERACTION
require(success);
}This looks like a small change, but it eliminates the reentrancy vector entirely. When the attacker’s fallback function tries to call withdraw() again, balances[msg.sender] is already zero, and the require statement blocks the second call.
Using OpenZeppelin’s ReentrancyGuard
OpenZeppelin provides a widely used ReentrancyGuard modifier that adds a mutex lock to functions. When a function with the nonReentrant modifier is called, it sets a lock variable. If the same function (or any other function with the modifier) is called again before the first execution finishes, it reverts. This is a belt-and-suspenders approach that works alongside the Checks-Effects-Interactions pattern.
SafeMath and Solidity 0.8+ Built-in Protections
For contracts compiled with Solidity 0.8.0 or later, arithmetic overflow and underflow checks are handled automatically by the compiler. Any operation that would cause a wrap-around simply reverts the transaction. For older contracts, the SafeMath library (also from OpenZeppelin) provides the same protection through wrapper functions like add(), sub(), mul(), and div().
If your MLM platform is still running contracts on Solidity 0.6 or 0.7 without SafeMath, upgrading should be a top priority. We cover more about how to protect smart contracts from attacks in a separate guide focused on broader security strategies.
Code Audits and Penetration Testing
No matter how experienced the developer is, manual code audits and automated security scans are essential. Tools like Slither, Mythril, and Echidna can catch common vulnerability patterns. But automated tools alone are not enough. Human auditors who understand the business logic of MLM systems can catch issues that tools miss, like economic exploits where the math is technically correct but the business outcome is manipulated.
Time Locks and Withdrawal Limits
Adding time-based restrictions and per-transaction withdrawal limits is a practical damage control measure. Even if an attacker finds an exploit, a withdrawal cap of, say, 5 ETH per 24 hours limits how much they can extract before the team detects the issue and pauses the contract. Time locks on critical administrative functions also prevent attackers from making immediate changes to contract parameters.
The Lifecycle of a Smart Contract Vulnerability in MLM Platforms
Understanding how a vulnerability moves from creation to exploitation helps teams build better defenses at every stage. Here is the typical lifecycle.
| Stage | What Happens | Where It Can Be Caught |
|---|---|---|
| 1. Introduction | Developer writes vulnerable code during contract development | Code review, pair programming |
| 2. Deployment | Contract goes live on mainnet with the vulnerability baked in | Pre-deployment audit, testnet simulation |
| 3. Discovery | Attacker or researcher identifies the flaw through code analysis | Bug bounty program, ongoing monitoring |
| 4. Exploitation | Attacker crafts and executes the exploit transaction | Anomaly detection, transaction monitoring |
| 5. Impact | Funds drained, users affected, platform reputation damaged | Emergency pause mechanism, withdrawal limits |
| 6. Response | Team pauses contract, investigates, and plans fix or migration | Incident response plan, upgradeable contracts |
The cheapest place to catch a vulnerability is at stage one. Every stage after that costs exponentially more, both in money and in trust. This is why we always tell clients: invest in security before deployment, not after a breach.
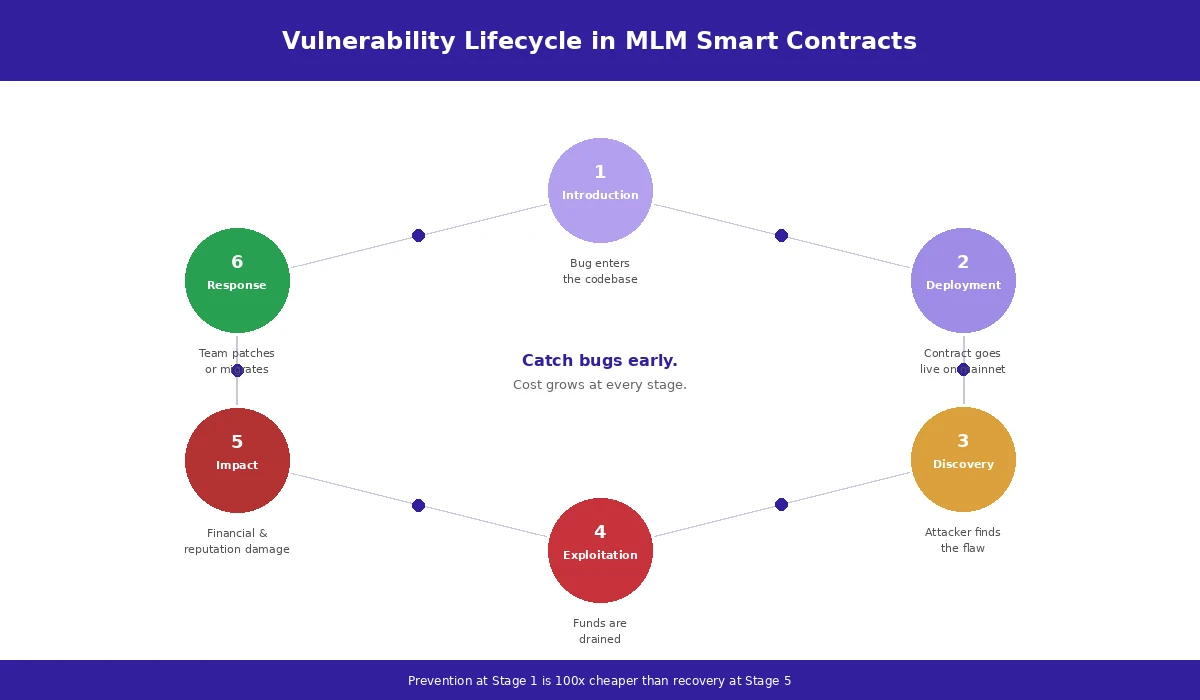
Fig 3: The six-stage lifecycle of a smart contract vulnerability in MLM platforms, from code introduction to incident response.
Best Practices for Secure MLM Smart Contract Development
Beyond specific attack prevention, there are broader best practices that every team building MLM smart contracts should follow. These come from real project experience, not textbooks.
Start with Secure Architecture Planning
Security is not something you bolt on at the end. The architecture of your MLM contract should be designed with security in mind from day one. This means separating concerns (keeping user management, payout logic, and admin functions in separate contracts or modules), using proxy patterns for upgradeability, and minimizing the amount of ETH or tokens held in any single contract at any given time.
The way you structure your referral tree storage, commission calculation, and fund pooling all have security implications. For platforms exploring how Web3 is disrupting traditional network marketing, security-first architecture is what separates sustainable platforms from ones that collapse after a single incident.
Gas Optimization Without Compromising Security
There is always a temptation to use unchecked blocks in Solidity 0.8+ to save gas on arithmetic operations. While this can be appropriate in specific scenarios where overflow is mathematically impossible (like incrementing a loop counter that will never reach 2^256), it should never be used for balance calculations, commission math, or any user-facing financial logic. Gas savings of a few thousand wei are not worth the risk of an overflow exploit.
Multi-Layer Validation Mechanisms
Good contracts do not rely on a single check. They layer multiple validation mechanisms: input validation on every public function, access control to restrict who can call sensitive functions, reentrancy guards on all functions that make external calls, withdrawal rate limiting, and event emission for every state change so off-chain monitoring tools can flag anomalies in real time.
Third-Party Security Audits Are Non-Negotiable
We say this from experience, not as a sales pitch. Every MLM contract that handles real user funds should be audited by at least one independent security firm before going to mainnet. Ideally, you want two audits from different firms, because different auditors catch different things. The cost of an audit (typically $5,000 to $50,000 depending on contract complexity) is a fraction of what you stand to lose in an exploit.
The adoption rate of blockchain MLM platforms is growing fast, and so is the sophistication of attackers targeting them. Platforms that skip audits are playing a dangerous game.
Security Checklist for MLM Smart Contract Developers
| Security Measure | Purpose | Implementation Priority |
|---|---|---|
| Checks-Effects-Interactions pattern | Prevents reentrancy by updating state before external calls | Critical |
| ReentrancyGuard modifier | Adds mutex lock as a second line of defense | Critical |
| Solidity 0.8+ or SafeMath | Prevents integer overflow and underflow | Critical |
| Withdrawal rate limits | Caps maximum drain in case of exploit | High |
| Emergency pause function | Allows team to halt contract during active attack | High |
| Third-party audit | Independent verification of code security | High |
| Event logging and monitoring | Enables real-time anomaly detection | Medium |
| Bug bounty program | Incentivizes ethical hackers to report flaws | Medium |
| Upgradeable proxy pattern | Allows fixing vulnerabilities post-deployment | Medium |
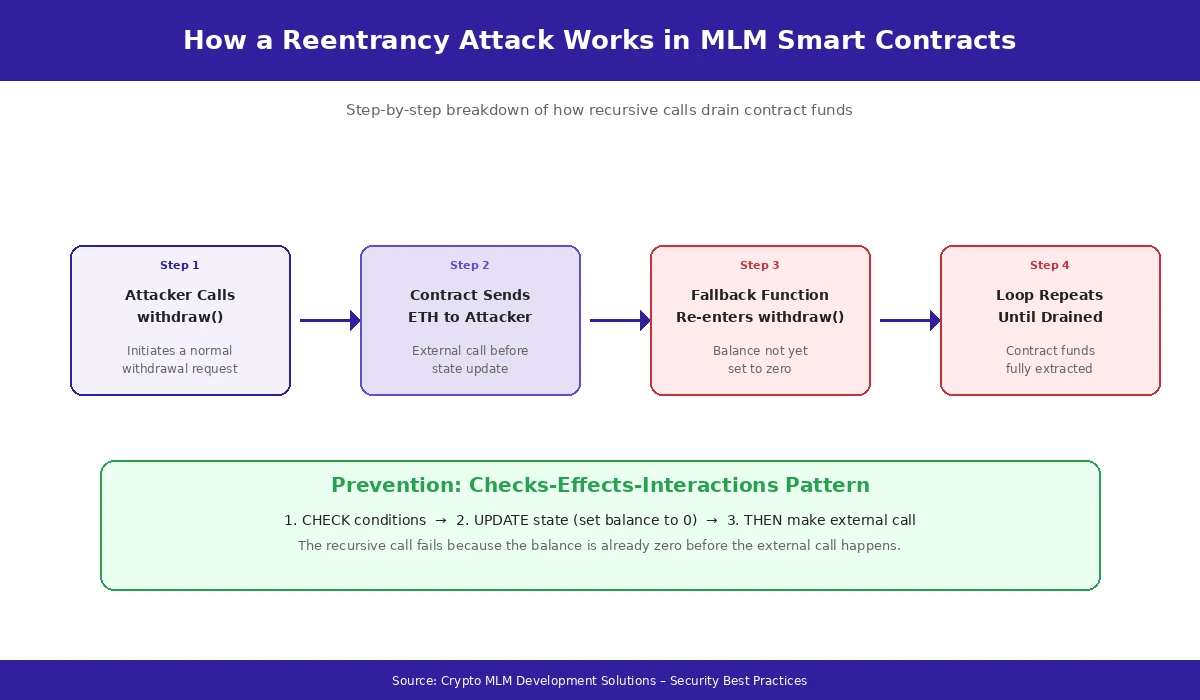
Fig 4: A prioritized security checklist every MLM smart contract developer should follow before mainnet deployment.
Conclusion: Security Is Not Optional in Crypto MLM
Reentrancy and overflow attacks are not theoretical risks. They are proven, documented exploits that have cost the blockchain industry hundreds of millions of dollars. And MLM smart contracts, with their complex multi-level payout structures and frequent external calls, are among the most vulnerable contract types out there.
The good news is that every one of these vulnerabilities is preventable. The Checks-Effects-Interactions pattern stops reentrancy. Solidity 0.8+ stops overflow. ReentrancyGuard adds an extra safety net. Audits catch what developers miss. And withdrawal limits contain the damage even in a worst-case scenario.
But prevention requires intention. It requires developers who understand these attack vectors deeply, architects who design with security as a first principle, and platform owners who invest in audits and testing before they go live. As a team with more than eight years of hands-on experience building and securing crypto MLM development solutions, we can tell you that the platforms that invest in security upfront are the ones that survive and grow.
If you are building or running a crypto MLM platform and you are not sure whether your smart contracts are safe, get them audited. Do not wait until someone finds the vulnerability for you. The cost of prevention is always a fraction of the cost of recovery.
The future of decentralized MLM belongs to platforms that take trust seriously. And trust starts with code that is secure by design.
Frequently Asked Questions
The main reason is structural. MLM contracts distribute payouts to multiple users across several referral levels within a single transaction. Each of those distributions requires an external call to send funds. A standard DeFi swap or lending contract might make one or two external calls per transaction. An MLM payout function could make ten or more. Every one of those calls is a potential entry point for a reentrancy exploit. On top of that, MLM contracts often use loops to traverse the referral tree, which adds further complexity and attack surface that simpler contracts just do not have.
For new contracts compiled on Solidity 0.8 or later, the compiler will automatically revert transactions that would cause an overflow or underflow. That is a huge improvement. However, there are two situations where you still need to be careful. First, if your contract uses unchecked blocks to save gas, those sections bypass the automatic checks. Second, if your platform is running older contracts written in Solidity 0.6 or 0.7 that were never upgraded, those contracts are fully exposed to overflow and underflow bugs unless they use the SafeMath library.
It depends on the complexity of the contract. A relatively straightforward MLM contract with basic referral logic might cost between $5,000 and $15,000 to audit. More complex systems with multiple plan types, token integrations, and admin functions can range from $20,000 to $50,000 or more. That might sound like a lot, but consider that a single exploit can drain the entire contract balance in minutes. We have seen platforms lose hundreds of thousands of dollars because they skipped a $10,000 audit. The math is pretty clear.
Yes. Any blockchain that supports smart contracts with external call capabilities can be vulnerable to reentrancy. This includes BNB Smart Chain, Polygon, Avalanche, Fantom, and other EVM-compatible chains. The underlying vulnerability is in the Solidity code pattern, not in Ethereum itself. If your MLM contract is deployed on any EVM chain and it makes external calls before updating state, it is vulnerable. Non-EVM chains like Solana or Tron have different execution models, so the exact attack pattern differs, but analogous issues can still arise depending on how the contract is written.
The Checks-Effects-Interactions (CEI) pattern is a coding discipline where you structure every function to validate inputs first, update all internal state second, and make external calls last. It is the fundamental fix for reentrancy. ReentrancyGuard is a modifier from OpenZeppelin that adds a mutex lock. When a function with this modifier is executing, no other function with the same modifier can run until the first one finishes. We recommend using both. CEI is your primary defense, and ReentrancyGuard is your safety net. Belt and suspenders. In the eight-plus years we have been building these systems, we have never seen a contract that was exploited through reentrancy when both of these were properly implemented.
First, if your contract has a pause function (and it should), activate it immediately to prevent any further transactions while you investigate. Second, get a professional security audit done as fast as possible. Do not try to diagnose the issue yourself unless you have deep expertise in Solidity security. Third, if the vulnerability is confirmed, you will likely need to deploy a new, fixed contract and migrate user data and funds to it. This is where having an upgradeable proxy pattern pays off, because you can swap the logic contract without changing the address users interact with. If you do not have an upgrade mechanism, the migration will be more complex, but it is still doable. The key is to act fast and not hope the vulnerability goes unnoticed.
Author

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.







