Ai Overview
Before diving into specific challenges, it helps to understand why this paradox exists at all. Blockchain was designed to solve a specific problem: how can parties who do not trust each other agree on a shared truth without relying on a trusted third party? If everyone can see every transaction, no one can cheat. Competitors can identify supplier relationships, production volumes, seasonal patterns, and pricing structures just by watching the chain.
Key Takeaways
- Public blockchains expose transaction history permanently, making pseudonymity a weak privacy shield in practice.
- GDPR and similar regulations conflict with blockchain immutability, creating legal barriers for adoption in healthcare and finance.
- Private blockchains solve privacy but introduce trust deficits that undermine the core value proposition of distributed ledgers.
- Zero-knowledge proofs offer the most promising technical solution, allowing verification without data exposure.
- Successful blockchain projects require architecture decisions that match specific industry privacy requirements from day one.
- Layer 2 solutions and off-chain storage provide practical compromises between full transparency and complete privacy.
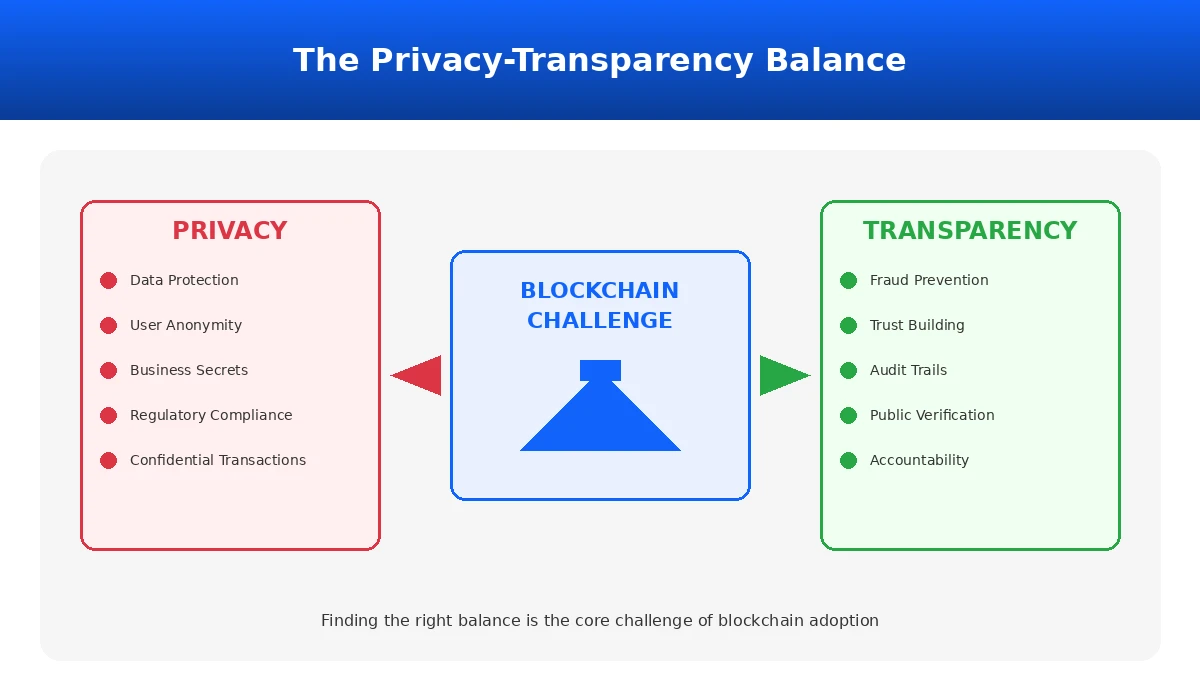
Blockchain technology promised a new way to build trust without intermediaries. The idea was straightforward: put everything on a shared ledger, make it visible to everyone, and remove the need to trust any single party. But here is the problem that developers and organizations discovered once they started building real systems: the transparency that creates trust also destroys privacy.
This is not a theoretical concern. Companies have abandoned blockchain projects after realizing competitors could see their supplier relationships. Healthcare organizations have shelved patient record systems because they could not comply with data protection laws. Financial institutions have delayed adoption because they could not hide trading positions from market participants.
The tension between privacy and transparency sits at the core of almost every blockchain implementation challenge. And solving it requires understanding both the technical constraints and the governance decisions that shape how blockchain systems actually work in production environments.
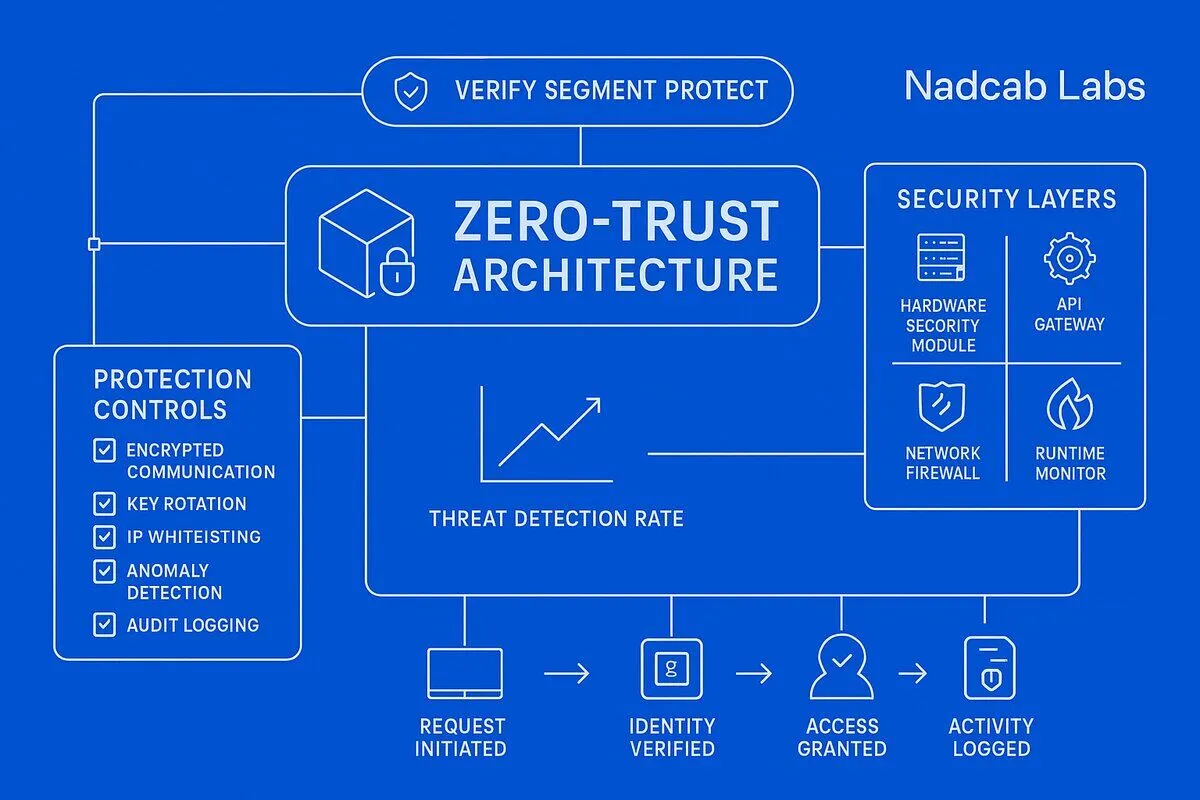
At Nadcab Labs, we have spent over 8 years building blockchain solutions across finance, supply chain, healthcare, and enterprise sectors. This experience has taught us that privacy and transparency problems are not bugs to be fixed. They are fundamental design tradeoffs that require careful architectural decisions from the start of any project.
Understanding the Privacy-Transparency Paradox in Blockchain Development
Before diving into specific challenges, it helps to understand why this paradox exists at all. Blockchain was designed to solve a specific problem: how can parties who do not trust each other agree on a shared truth without relying on a trusted third party?
The answer was transparency. If everyone can see every transaction, no one can cheat. If the ledger is immutable, no one can go back and change history. This works beautifully for preventing fraud and building trust among untrusted parties.
But transparency creates new problems. When everyone can see everything, sensitive information becomes permanently exposed. Business strategies become visible to competitors. Personal financial histories become trackable by anyone with blockchain analysis tools. Medical records become accessible in ways that violate patient privacy expectations.
According to Wikipedia’s blockchain overview, the technology was originally designed for Bitcoin where transaction transparency was a feature, not a bug. But as blockchain expanded into enterprise applications, healthcare records, and supply chain management, what started as a feature became a significant barrier to adoption.
Privacy Challenges: Technical Vulnerabilities Developers Must Address
When building blockchain systems, developers face several privacy vulnerabilities that require architectural solutions. Understanding these challenges is the first step toward building systems that actually work in production.
| Privacy Challenge | Technical Root Cause | Impact Level | Development Complexity |
|---|---|---|---|
| Transaction History Exposure | Permanent ledger visibility | Critical | High |
| Identity Linking | Address reuse and exchange integration | High | Medium |
| Business Data Exposure | On-chain metadata visibility | High | Medium |
| Regulatory Non-Compliance | Immutability vs deletion rights | Critical | Very High |
| Error Permanence | No data deletion capability | Medium | High |
Challenge 1: Permanent Transaction History Visibility
On public blockchains like Bitcoin and Ethereum, every transaction ever made is visible to anyone who wants to look. While wallet addresses are pseudonymous, they are not anonymous. Blockchain analysis firms have built billion-dollar businesses by connecting addresses to real identities through transaction patterns, exchange deposits, and behavioral analysis.
A study from MIT found that a significant percentage of Bitcoin addresses have been de-anonymized through chain analysis alone. This means that the privacy protection offered by pseudonymous addresses is largely illusory in practice.
For developers, this creates a fundamental challenge. Any data you put on a public blockchain becomes permanent public record. There is no delete button. There is no edit function. Once data is on chain, it stays there forever, visible to everyone.
This is why understanding sidechains in blockchain networks becomes critical for enterprise implementations. Sidechains allow organizations to process transactions with different privacy parameters while still benefiting from main chain security.
Challenge 2: Regulatory Compliance Conflicts
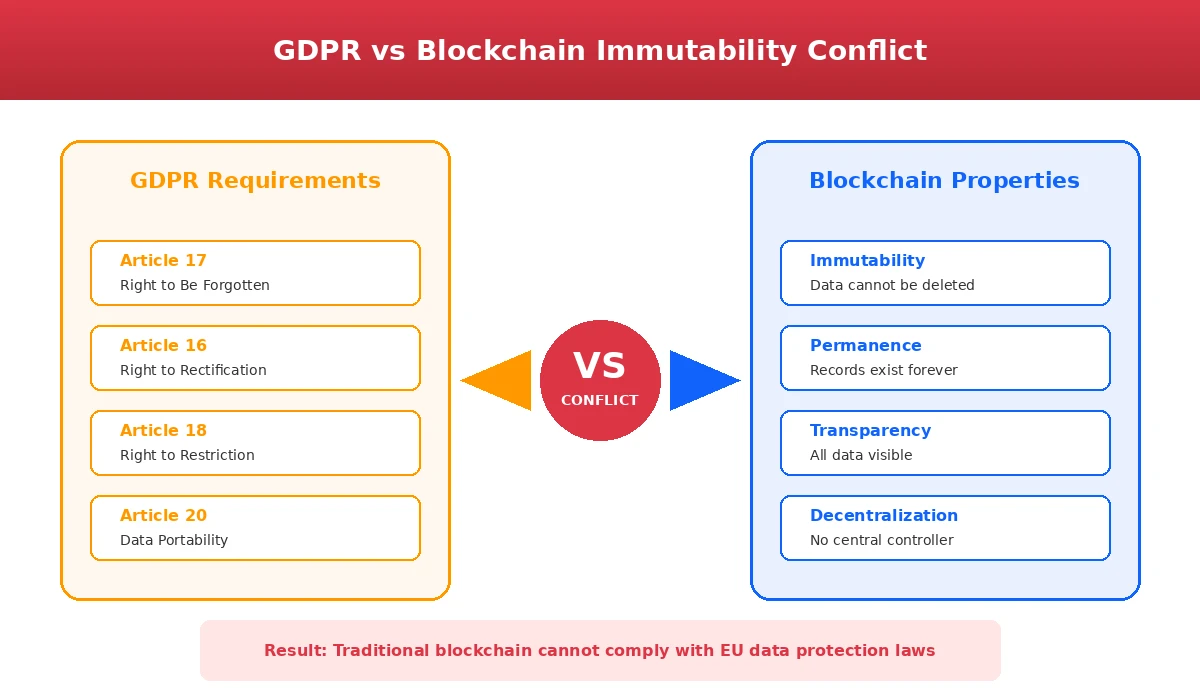
The European Union’s General Data Protection Regulation grants individuals the right to be forgotten. This means people can demand that organizations delete their personal data. But blockchain’s fundamental design prevents data deletion. Once something is recorded, it cannot be removed.
This creates a direct conflict. Organizations operating in the EU cannot use traditional public blockchains for any system that stores personal data about EU residents. The same applies to healthcare data under HIPAA in the United States, financial data under various banking regulations, and similar privacy frameworks worldwide.
The legal interpretation of whether blockchain addresses constitute personal data remains contested. Some regulators have taken the position that any data that could be linked to an individual, even indirectly, qualifies as personal data. Under this interpretation, blockchain transaction histories would fall under GDPR jurisdiction.
Challenge 3: Business Information Exposure
Organizations hesitate to adopt public blockchains because competitors can observe their operations. Consider a supply chain blockchain where every transaction is visible. Competitors can identify supplier relationships, production volumes, seasonal patterns, and pricing structures just by watching the chain.
A manufacturing company we worked with abandoned plans for blockchain supply chain tracking after their analysis revealed that competitors would gain visibility into their production capacity and supplier network. The transparency that would prove product authenticity to customers would also expose trade secrets to competitors.
This challenge extends beyond supply chains. Financial institutions worry that large trades will be visible to other market participants. Pharmaceutical companies fear that production volumes will reveal demand forecasts. Retailers recognize that transaction patterns expose business strategies.
Challenge 4: Identity Exposure Through Transaction Linking
Even with pseudonymous addresses, multiple factors expose user identity. When users deposit funds at cryptocurrency exchanges, their identity becomes linked to blockchain addresses through exchange KYC requirements. When users spend cryptocurrency at retailers, the same linking occurs.
Wallet reuse compounds this problem. Most users reuse addresses across transactions, creating a permanent transaction history linked to their identity once any single transaction is identified. On-chain metadata like usernames or email addresses embedded in transactions creates additional permanent identity links.
Understanding how bridge contracts work is essential for developers building cross-chain systems, as bridges create additional identity correlation opportunities that must be addressed in privacy-conscious architectures.
Transparency Challenges: Trust Problems in Private Systems
When organizations try to solve privacy problems by implementing private or permissioned blockchains, they create new trust problems. The transparency that made blockchain valuable in the first place disappears, and stakeholders question whether the system is actually trustworthy.
The Private Blockchain Trust Deficit
A private supply chain blockchain implemented for a major retailer faced immediate customer skepticism. Customers asked: if the blockchain is truly transparent and trustworthy, why is the data restricted? If only approved participants can see the data, how is this different from a regular database that the company controls?
These questions highlight a fundamental tension. Private blockchains solve privacy problems but undermine the trust benefits that motivated blockchain adoption in the first place. External stakeholders have no way to verify that the system is operating as claimed because they cannot see the data.
Regulators share similar concerns. A private food supply chain blockchain could theoretically hide contaminated products from view. Auditors cannot easily verify what transactions actually occurred if they lack network access. The black box perception undermines confidence in the entire system.
Technical Complexity Creating Transparency Gaps
Even when blockchain data is technically transparent, most users cannot interpret it meaningfully. Viewing blockchain transactions requires understanding wallet addresses, hash functions, transaction structures, and technical protocols. The average consumer or business user cannot audit this information in any practical sense.
This creates a transparency gap. The data is visible but not understandable. The transparency advantage of blockchain becomes useless if ordinary users cannot comprehend the transparent data. A patient cannot meaningfully audit their healthcare record stored on a blockchain if they do not understand the technical format.
Complete transparency also creates information overload. When every transaction and data point is visible, finding important information becomes difficult. The signal gets lost in the noise.
Build Privacy-Compliant Blockchain Systems
Navigate the privacy-transparency tradeoff with expert guidance. Get architecture recommendations tailored to your specific compliance requirements and business needs.
Industry Impact: How Privacy-Transparency Tradeoffs Affect Real Projects
Different industries face different versions of the privacy-transparency challenge. Understanding these variations helps developers and organizations choose appropriate architectural approaches.
| Industry | Primary Privacy Need | Primary Transparency Need | Common Solution Approach |
|---|---|---|---|
| Finance | Trading position confidentiality | Regulatory audit trails | Permissioned networks with ZKPs |
| Healthcare | Patient data protection | Data integrity verification | Off-chain storage with hash anchoring |
| Supply Chain | Supplier relationship protection | Product provenance verification | Selective disclosure with encryption |
| Government | Citizen data protection | Public accountability | Hybrid public-private architectures |
| Real Estate | Transaction price confidentiality | Ownership verification | Permissioned with public attestations |
Finance and Cryptocurrency
Financial institutions face perhaps the most acute version of the privacy-transparency paradox. On one hand, regulators demand complete audit trails and the ability to monitor for suspicious activity. On the other hand, trading positions must remain confidential to prevent front-running and market manipulation.
Bitcoin’s fully transparent ledger creates problems for institutional adoption. Large purchases become permanently visible on-chain, exposing positions to competitors and potentially affecting markets. A significant percentage of institutional investors cite privacy concerns as a barrier to larger cryptocurrency positions.
Understanding how flash loans in blockchain work illustrates another dimension of this challenge. Flash loans enable complex financial operations that leave permanent transaction trails, creating both transparency benefits for auditing and privacy concerns for traders.
The ransomware tracking problem shows the other side. Bitcoin’s transparency allows law enforcement to trace ransom payments through blockchain analysis. While this helps investigate crimes, it also means legitimate users face potential misidentification or scrutiny based on transaction patterns that happen to resemble suspicious activity.
Healthcare
Healthcare presents the clearest case where blockchain transparency conflicts with fundamental privacy rights. Patient medical records are among the most sensitive data categories. HIPAA in the United States and GDPR in Europe impose strict requirements on how this data can be stored, accessed, and shared.
A blockchain containing patient health records would expose medical histories permanently. This creates discrimination risks where insurance companies or employers could potentially access health information and make decisions based on medical conditions. Patients with stigmatized conditions face particular exposure risks.
Most healthcare blockchain projects have stalled due to these regulatory conflicts. The immutability that would ensure data integrity directly contradicts the deletion rights that privacy regulations guarantee to patients.
Supply Chain
Supply chain blockchain projects face the traceability versus confidentiality tension in its purest form. Transparency benefits consumers who want to verify product authenticity, fair trade certification, or sustainable sourcing. But the same transparency exposes business relationships to competitors.
Consider a coffee company using blockchain to prove fair trade certification. Consumers can verify that coffee beans came from certified cooperatives. But competitors can also see which cooperatives supply the company, enabling them to approach those cooperatives directly and undercut existing relationships.
Manufacturing creates additional exposure. Production volumes, seasonal patterns, component sourcing, logistics costs, and inventory levels all become visible through transparent supply chain transactions. Patent and trade secret information embedded in manufacturing process data creates intellectual property exposure risks.
The impact of blockchain on manufacturing is significant when implemented correctly. Our experience shows that blockchain in manufacturing industries requires careful architecture to protect competitive information while maintaining the transparency benefits that justify adoption.
Development Solutions: Technical Approaches to Balance Privacy and Transparency
Several technical approaches have emerged to address the privacy-transparency tradeoff. Each involves different complexity levels, performance implications, and tradeoffs that developers must understand before selecting an approach.
Zero-Knowledge Proofs: Verification Without Disclosure
Zero-knowledge proofs represent the most promising technical solution to the privacy-transparency paradox. They allow one party to prove a statement is true without revealing the underlying data. For blockchain applications, this means proving a transaction is valid without exposing transaction details.
Here is how zero-knowledge proofs work in practice. A user can prove they have sufficient funds to complete a transaction without revealing their total account balance. An organization can prove compliance with regulations without disclosing the specific data being audited. A supply chain participant can prove product authenticity without revealing supplier relationships.
Major financial institutions including JPMorgan and ING Bank are actively researching zero-knowledge proof applications. Initial production deployments are expected in the coming years as the technology matures.
The limitations are significant. Zero-knowledge proofs are computationally expensive, requiring substantial processing power to generate and verify. Implementation complexity is high, and the technology continues to evolve rapidly. Auditing zero-knowledge proof systems requires specialized expertise that most organizations lack.
Permissioned Blockchains: Controlled Access
Permissioned blockchains restrict network access to approved participants. Only pre-approved organizations can view specific data. Participants see transactions relevant to their business relationships. A central authority controls access permissions.
The Hyperledger Fabric framework enables enterprise blockchains where participating organizations control data access. Financial consortiums use this model to share transaction data among members while preventing public visibility.
The tradeoffs are clear. Permissioned blockchains reduce decentralization by reintroducing centralized authority. They increase trust requirements because participants must trust the gatekeeper. They reduce fraud prevention benefits because limited visibility prevents detection by outside parties.
For many enterprise applications, these tradeoffs are acceptable. The blockchain still provides benefits over traditional databases through cryptographic verification, immutable audit trails, and consensus-based validation among consortium members.
Layer 2 and Off-Chain Solutions
Layer 2 solutions move transaction processing off the main blockchain while maintaining final settlement transparency. This approach keeps detailed transaction data private while preserving the security and verification benefits of the base layer.
The pattern works as follows. Detailed transaction data is stored off-chain in private databases or specialized layer 2 networks. Only final settlement results or hash verification is recorded on the main blockchain. Off-chain data uses traditional privacy protections while on-chain data provides cryptographic verification.
The Bitcoin Lightning Network exemplifies this approach. Payment channels process transactions off-chain with final settlement on-chain. Transaction details remain private between channel participants while the blockchain verifies final states.
Understanding layer 2 architecture is essential for building scalable privacy-preserving systems. These solutions also address the scalability limitations that affect public blockchains, making them attractive for high-volume enterprise applications.
The concept connects to how proof of activity in blockchain systems work. Different consensus and validation mechanisms create different transparency and privacy characteristics that developers must account for in their architecture decisions.
Data Masking and Encryption
Encryption protects sensitive data while maintaining blockchain’s structural transparency. Sensitive data is encrypted before recording on the blockchain. Only authorized parties with encryption keys can decrypt the content. Transaction metadata remains visible for auditing while details stay hidden.
This approach maintains blockchain transparency at the structural level while protecting content confidentiality. Auditors can verify that transactions occurred and follow audit trails without accessing encrypted content. Selective revelation allows data owners to share information with specific parties by providing decryption keys.
Key management becomes the critical challenge. Encryption keys must be securely generated, stored, and shared with authorized parties. Lost keys mean permanent data loss since the encrypted content cannot be recovered. Key compromise means privacy breach for all data encrypted with that key.
Privacy-Focused Protocol Design
Some blockchain protocols prioritize privacy at the architectural level. Monero uses ring signatures and stealth addresses to obscure transaction sender, recipient, and amount. Zcash implements zk-SNARKs, a form of zero-knowledge proof, to enable private transactions on a transparent blockchain.
These protocols demonstrate that privacy-preserving blockchain is technically possible. However, they come with significant tradeoffs. Enhanced privacy reduces regulatory visibility, creating money laundering concerns. Extreme privacy creates accountability gaps that regulators view with suspicion.
The Financial Crimes Enforcement Network estimates that a notable percentage of illicit cryptocurrency transfers occur on privacy-focused chains. This has led to increased regulatory pressure including delisting from exchanges and enhanced compliance requirements.
For enterprise applications, privacy-focused protocols may create more regulatory problems than they solve. The privacy benefits must be weighed against compliance risks and reputational concerns.
Solution Comparison: Choosing the Right Privacy Approach
Each privacy solution involves different tradeoffs across multiple dimensions. The following comparison helps developers and organizations evaluate options based on their specific requirements.
| Solution | Privacy Level | Transparency Level | Implementation Complexity | Performance Impact | Best For |
|---|---|---|---|---|---|
| Zero-Knowledge Proofs | High | High (verifiable) | Very High | Significant | Finance, Identity |
| Permissioned Blockchain | Medium-High | Low (restricted) | Medium | Low | Enterprise, Consortiums |
| Layer 2 Solutions | Medium | Medium | High | Low | Payments, High Volume |
| Data Encryption | Medium | Low | Medium | Low | Supply Chain, Healthcare |
| Privacy Protocols | Very High | Very Low | Low (use existing) | Medium | Consumer Privacy Focus |
Implementation Lifecycle: From Requirements to Production
Successfully implementing privacy-preserving blockchain systems requires a structured approach that addresses privacy and transparency requirements at each development phase.
Phase 1: Requirements Analysis
Begin by mapping stakeholder privacy and transparency requirements. Identify which data must remain private, which data requires public verification, and which stakeholders need access to which information. Document regulatory requirements including GDPR, HIPAA, or industry-specific compliance obligations.
Phase 2: Architecture Selection
Select blockchain architecture based on requirements analysis. Choose between public, private, or hybrid approaches. Identify which privacy-preserving technologies to implement. Define data flows that maintain required transparency while protecting sensitive information.
Phase 3: Development and Integration
Implement selected privacy solutions with appropriate testing. Integrate with existing systems while maintaining privacy boundaries. Build access control mechanisms that enforce privacy policies. Develop user interfaces that make privacy features accessible without requiring technical expertise.
Phase 4: Testing and Validation
Test privacy protections under realistic conditions. Verify that transparency mechanisms work as designed. Conduct security audits focused on privacy vulnerabilities. Validate regulatory compliance with legal review.
Phase 5: Deployment and Monitoring
Deploy with monitoring for privacy and transparency metrics. Establish incident response procedures for privacy breaches. Create feedback mechanisms to identify privacy issues in production. Plan for ongoing privacy requirement evolution.
Throughout this lifecycle, organizations benefit from working with experienced blockchain development partners who understand both the technical implementation challenges and the regulatory context that shapes privacy requirements.
Smart Contracts and Privacy: Additional Considerations
Smart contracts introduce additional privacy challenges that developers must address. Contract code on public blockchains is visible to everyone, exposing business logic that organizations may prefer to keep confidential. Contract state changes are publicly observable, revealing information about contract execution.
Understanding how auction contracts work illustrates this challenge. Auction smart contracts must balance the need for bid confidentiality before auction completion with the need for transparent bid verification after completion.
Similar considerations apply to gaming and entertainment applications. When building blockchain-based games, privacy requirements differ from financial applications. Our work on metaverse game development required careful consideration of player data privacy while maintaining game state transparency for fair play verification.
The relationship between blockchain and cloud infrastructure also affects privacy architecture. Understanding serverless computing helps developers design systems where off-chain components handle sensitive processing while blockchain handles verification and settlement.
The Future of Privacy-Preserving Blockchain
The privacy-transparency challenge will not disappear. It is fundamental to blockchain’s design. But the tools for managing this tradeoff continue to improve.
Zero-knowledge proof technology is becoming more efficient and easier to implement. New cryptographic techniques enable more sophisticated privacy preservation while maintaining verification capabilities. Regulatory frameworks are evolving to accommodate blockchain’s unique characteristics.
Organizations that understand these dynamics can make informed decisions about blockchain adoption. Those who ignore the privacy-transparency tradeoff will face implementation failures, regulatory problems, and stakeholder resistance.
The comparison between traditional finance and cryptocurrency continues to evolve. As we have explored in our analysis of fiat versus crypto, each system offers different privacy and transparency characteristics that appeal to different use cases.
Successful blockchain adoption requires honest assessment of privacy and transparency requirements, rigorous architecture design that addresses genuine stakeholder concerns, and implementation by teams with deep expertise in both blockchain technology and the regulatory context where blockchain will operate.
Nadcab Labs Expertise: 8+ Years of Privacy-Focused Development
At Nadcab Labs, we have navigated the privacy-transparency challenge across hundreds of blockchain implementations. Our experience spans financial services requiring regulatory compliance, healthcare projects with stringent patient privacy requirements, supply chain systems balancing transparency and competitive confidentiality, and enterprise applications where data governance is non-negotiable.
We have learned that privacy and transparency problems are not obstacles to overcome. They are design constraints that shape architecture decisions from the earliest project phases. Organizations that treat privacy as an afterthought end up rebuilding systems or abandoning projects entirely.
Our approach begins with comprehensive requirements analysis that maps stakeholder needs against technical capabilities. We help organizations understand which tradeoffs they face and select solutions appropriate to their specific context. We implement privacy-preserving architectures using proven patterns while adapting to unique organizational requirements.
The technology landscape continues to evolve rapidly. New privacy-preserving techniques emerge regularly. Regulatory requirements shift as governments develop blockchain-specific frameworks. Organizations need partners who stay current with these developments and can translate technical advances into practical implementation guidance.
FAQs
Q1.What is the main problem with blockchain's transparency?
Blockchain’s main transparency problem is that transaction visibility necessary for fraud prevention conflicts directly with privacy protection requirements. Public blockchains record all transactions permanently and visibly, allowing behavioral analysis and de-anonymization despite pseudonymous addresses. Organizations cannot hide competitive information, individuals cannot maintain financial privacy, and sensitive data cannot be protected from permanent exposure. This creates a fundamental adoption barrier in regulated industries where privacy is mandatory.
Q2.What are the privacy issues with blockchain?
Blockchain creates five major privacy vulnerabilities:
- Transaction Visibility: Permanent, public transaction records enable behavioral analysis and de-anonymization despite pseudonymous addresses.
- Data Permanence: Once recorded, data cannot be deleted, creating permanent exposure of sensitive information without remediation options.
- Regulatory Conflicts: Blockchain immutability contradicts regulations like GDPR granting “right to be forgotten” and data deletion rights.
- Business Exposure: Competitors gain visibility into supplier relationships, pricing structures, and strategic partnerships through transparent blockchains.
- Identity Linking: Exchange integration, on-chain metadata, and wallet reuse enable identity connection to blockchain activities despite initial pseudonymity.
Q3.What is transparency in blockchain?
Transparency in blockchain refers to the property that all network participants can independently verify transactions without relying on central authorities. Specifically, transparency means:
(1) All transactions are visible to participants,
(2) Participants can verify transaction validity through mathematical proofs,
(3) Transactions cannot be altered after recording, and
(4) Complete audit trails exist for investigation. This transparency builds trust by making fraud detectable and unverifiable claims impossible.
Q4.What are the barriers to blockchain adoption?
Five major barriers prevent blockchain adoption:
- Privacy-Transparency Tradeoff: Organizations must choose between transparency (fraud prevention) and privacy (data protection), often incompatible with business requirements.
- Technical Complexity: Blockchain implementation requires specialized expertise, infrastructure, and significant engineering investment.
- Regulatory Uncertainty: Unclear regulatory treatment creates legal risk in finance, healthcare, and government sectors.
- Performance Limitations: Many blockchains lack transaction throughput for high-volume applications, limiting practical deployment.
- Integration Challenges: Connecting blockchain with existing systems and databases requires extensive development effort.
Q5.How do you balance privacy and transparency in blockchain?
Balancing privacy and transparency requires layered approaches selecting appropriate solutions for specific use cases:
Zero-Knowledge Proofs: Enable transaction verification without data disclosure—proving statement truth without revealing supporting information.
Permissioned Blockchains: Restrict access to approved participants, enabling selective transparency. Only authorized parties view specific transactions.
Layer 2 Solutions: Move transaction details off-chain while maintaining final settlement transparency on-chain.
Data Masking: Encrypt sensitive content on-chain while maintaining transparent transaction structure for auditing.
Private Blockchains: For maximum privacy within single organization, accepting reduced decentralization benefits.
Most successful implementations combine multiple approaches creating compartmentalized transparency.
Explore Services
Related Services
Reviewed by

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.