Key Takeaways
- Web3 communication refers to decentralized messaging, data sharing, and identity systems that operate without any central server controlling the flow or content of information.
- Web3 communication protocols like Waku, Matrix, and libp2p replace client-server architectures with peer-to-peer networks where every participant can relay messages independently.
- Decentralized networks eliminate the single points of failure and censorship vectors that make Web2 communication platforms vulnerable to outages, data breaches, and government suppression.
- Blockchain technology anchors Web3 messaging systems by providing tamper-proof identity records, on-chain governance for communication protocol rules, and verifiable message authenticity.
- Smart contracts in Web3 communication enable programmable messaging rules, automated access control, and trustless group governance without any platform administrator holding override authority.
- Web3 communication networks use end-to-end encryption by default with keys controlled by the user’s wallet, ensuring message content is mathematically inaccessible to relay nodes and protocol operators.
- Identity and authentication protocols built on DIDs (Decentralized Identifiers) and Verifiable Credentials create portable reputation systems that work across multiple Web3 messaging systems.
- Secure communication in Web3 addresses enterprise requirements in the USA, UK, UAE, and Canada by providing audit trails and cryptographic proofs that satisfy compliance without centralized data storage.
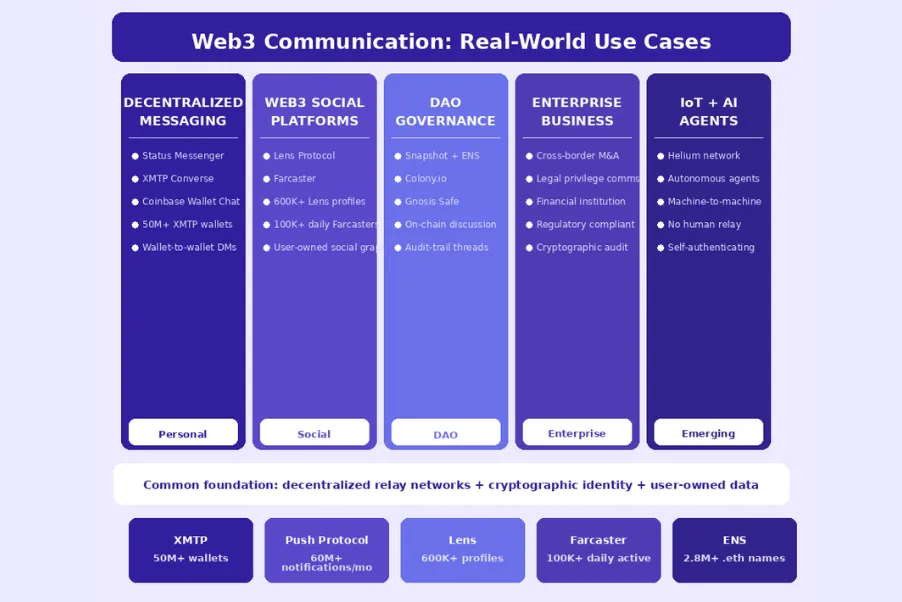
- The growth of Web3 social platforms including Lens Protocol and Farcaster demonstrates commercial demand for decentralized communication infrastructure beyond niche blockchain-native audiences.
- Integration of AI and IoT with Web3 communication infrastructure is creating autonomous machine-to-machine communication layers that require no human intermediary to route, authenticate, or validate messages.
What is Web3 Communication?
Web3 communication describes the complete ecosystem of protocols, networks, and tools that enable information exchange between people and systems without relying on centralized intermediaries to route, store, or validate messages. Organizations seeking professional Web3 services for communication infrastructure are fundamentally challenging the architecture that has governed internet messaging since the earliest email servers: the client-server model where a company controls both the infrastructure and the rules of communication. Web3 communication infrastructure replaces this model with peer-to-peer networks, cryptographic identity systems, and blockchain-anchored governance that distributes authority across thousands of nodes rather than concentrating it in a single corporate entity. The practical significance of this architectural shift extends far beyond ideology: it creates communication systems that are structurally resistant to censorship, impossible to shut down through single points of failure, and incapable of secretly harvesting message content for advertising or surveillance. After eight years of building Web3 infrastructure for clients across the USA, UK, UAE, and Canada, we have witnessed the maturation of Web3 communication from experimental protocols to production-grade systems serving millions of users across every category of application.
Evolution from Web2 to Web3 Communication
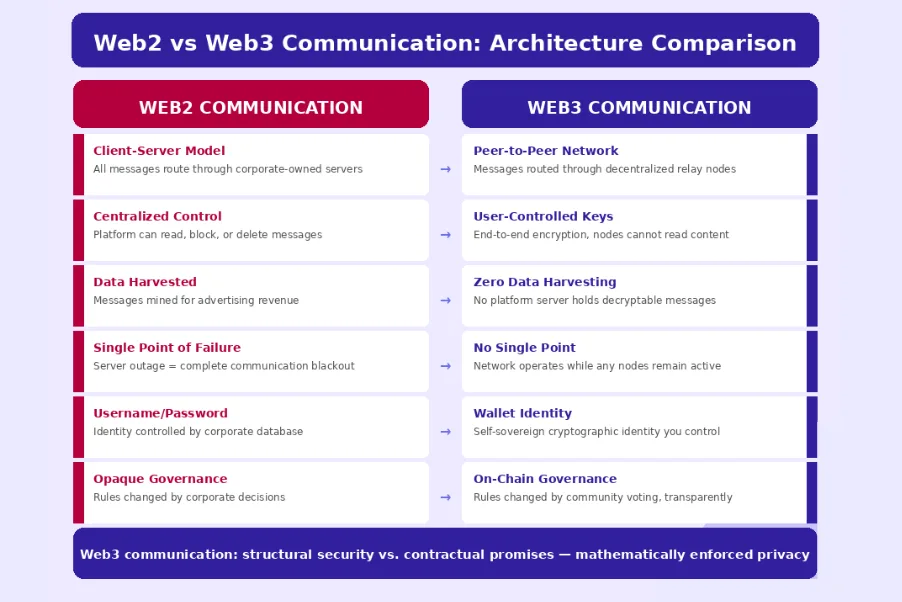
The transition from Web2 to Web3 communication represents a fundamental architectural inversion rather than an incremental improvement. Web2 communication is built on a hub-and-spoke model where every message, regardless of the distance between its sender and recipient, travels through corporate-owned servers that can read, modify, delay, or block it. When you send a message via WhatsApp, it travels to Meta’s servers, which decrypt it (despite the end-to-end encryption claim), apply spam filtering and content moderation, and then re-encrypt it before delivering it to the recipient. Every participant in this exchange must trust Meta to behave honestly, to protect their data, and to remain operational.
The 2021 WhatsApp outage that took the platform offline for six hours for 2 billion users worldwide illustrated the catastrophic single-point-of-failure risk of centralized communication infrastructure. Web3 communication protocols eliminate this dependency entirely: messages are routed through a peer-to-peer network of independent nodes where no single entity controls routing, no server decrypts message content in transit, and the network remains operational as long as any subset of nodes remains active. This architectural shift has been driven by growing demand from users, enterprises, and regulators in the UK, USA, UAE, and Canada who recognize that communication infrastructure is critical national and economic infrastructure that should not be controlled by a handful of private corporations.
Why Web3 Communication Matters Today?
The case for Web3 communication has grown more compelling with each passing year as the consequences of centralized communication architecture become more visible and more severe. Social media platforms have demonstrated that communication infrastructure owned by private companies is subject to opaque content moderation decisions that can silence entire communities without due process, warning, or appeal. Governments in multiple countries have demonstrated the willingness to order communication platforms to block messages, hand over user data, or implement surveillance backdoors, with platforms having little practical ability to resist these demands when their infrastructure is physically located within those governments’ jurisdictions.
Enterprise communication platforms have suffered repeated data breaches that exposed confidential business conversations and personal data at massive scale, with the Slack breach in 2021 and multiple Microsoft Teams vulnerabilities demonstrating that even enterprise-grade Web2 communication is not immune. Web3 communication addresses all three of these failure modes simultaneously: its decentralized architecture makes targeted censorship technically and economically prohibitive, its end-to-end encryption architecture makes surveillance backdoors structurally impossible, and its distributed storage model eliminates the concentrated data honeypots that make centralized platforms irresistible targets for attackers.
Key Features of Web3 Communication Systems
Web3 communication systems share a set of defining characteristics that distinguish them from both traditional Web2 messaging and simple encrypted messaging apps. Self-sovereign identity is the foundational feature: users control their own cryptographic identities through wallet keys rather than usernames and passwords stored in a provider’s database, making account ownership verifiable and portable across different applications. End-to-end encryption with user-controlled keys ensures that message content is mathematically inaccessible to any relay node in the network, with encryption keys derived from the user’s wallet rather than generated by the messaging platform. Censorship resistance is structural rather than policy-based: because no single entity controls the network’s relay infrastructure, there is no single point at which content can be filtered or blocked without the network detecting and routing around the interference.
Decentralized governance allows communities to collectively control the rules of their communication environment through on-chain voting, smart contract-enforced policies, and transparent rule changes that cannot be made unilaterally by any administrator. Interoperability between different Web3 messaging applications through common protocol standards enables users to communicate across application boundaries while maintaining a single persistent identity, analogous to how email enables communication between users of different email providers through a common protocol standard.
Decentralized Networks
Decentralized networks are the physical and logical infrastructure layer of Web3 communication, comprising thousands of independently operated nodes that collectively provide the routing, storage, and relay functions that centralized servers perform in Web2 architectures. Unlike the hub-and-spoke topology of centralized communication systems where all traffic flows through a small number of managed servers, decentralized networks use mesh topologies where each node connects to multiple peers and can route messages through many alternative paths. The resilience properties of this architecture are extraordinary: the internet itself was designed by DARPA to survive nuclear attacks by routing around damaged nodes, and Web3 communication networks inherit this resilience principle at the application layer. libp2p, developed by the Protocol Labs team as part of the IPFS project, is the foundational peer-to-peer networking library used by most Web3 communication protocols.
It handles peer discovery, connection multiplexing, stream-based communication, and protocol negotiation between nodes, providing a common networking foundation that allows different Web3 communication applications to interoperate at the network layer while implementing their own application-level protocols on top. The Ethereum network itself is a prominent example of a decentralized network where thousands of globally distributed nodes maintain a shared state without any central coordinator, demonstrating the scalability and reliability achievable by well-designed peer-to-peer communication architectures.
Blockchain Technology
Blockchain technology serves as the trust layer for Web3 communication systems, providing tamper-proof record keeping for identity registration, governance decisions, and message authentication that cannot be provided by any single centralized authority. In the context of Web3 communication, blockchain’s most important contribution is the public key infrastructure it enables: every participant in a Web3 communication network has a wallet address (derived from their public key) that serves as their verifiable identity, with cryptographic proofs of action authenticity (signatures) that any network participant can independently verify without trusting any certificate authority.
The Ethereum Name Service (ENS) demonstrates blockchain technology’s role as a communication addressing layer: ENS names like alice.eth provide human-readable addresses that resolve to wallet addresses, IPFS content hashes, and other decentralized resource identifiers, enabling Web3 communication participants to reach each other through memorable identifiers while the underlying address resolution is performed by immutable smart contracts rather than centrally controlled DNS servers. Blockchain-based governance mechanisms allow Web3 communication protocol communities to propose, vote on, and implement protocol changes through transparent on-chain processes that prevent any single organization from unilaterally modifying the rules that all participants have agreed to.
Smart Contracts in Communication
Smart contracts extend Web3 communication capabilities beyond simple peer-to-peer messaging into programmable, rule-governed communication environments that enforce community standards, manage access permissions, and automate communication workflows without any administrator holding override authority. Access control contracts define which wallet addresses can participate in specific communication channels, with membership rules enforced mathematically by the contract rather than by a platform’s terms of service that an administrator can modify or selectively enforce. Token-gated communication channels use smart contracts to verify NFT or token ownership before granting access to specific conversation spaces, enabling exclusive communication environments where membership is verifiable on-chain and cannot be revoked by platform administrators.
Communication governance contracts allow community members to vote on moderation policies, feature additions, and protocol parameters, creating democratic communication environments where the rules reflect the community’s actual preferences rather than a corporation’s business interests. Real-world implementations include the Lens Protocol, which uses smart contract-based social graphs deployed on Polygon to allow users to carry their followers, content, and reputation across different applications built on the protocol, and the XMTP (Extensible Message Transport Protocol), which uses Ethereum signing keys for message authentication and consent management, enabling wallet-to-wallet messaging with smart contract-based permission controls.
Peer-to-Peer Messaging Systems
Peer-to-peer messaging systems are the direct message exchange layer of Web3 communication, handling the actual transmission of message content between participants without routing through any centralized relay server that could intercept or modify message content. The Status messaging protocol, one of the earliest and most feature-complete Web3 P2P messaging implementations, uses the Waku protocol to route encrypted messages through a decentralized network of relay nodes, with each message encrypted using the Double Ratchet algorithm (the same cryptographic protocol used by Signal) before entering the network. Waku, which evolved from the original Whisper protocol in the Ethereum ecosystem, now operates as an independent peer-to-peer messaging protocol designed specifically for Web3 communication applications, providing message relay, content topic filtering, and optional incentivized node operation through the Waku incentivization model.
The Matrix protocol, while not exclusively Web3, has achieved significant adoption in the decentralized communication space through its federated server architecture that enables interoperability between independently operated homeservers, with bridge implementations connecting Matrix networks to Ethereum wallet addresses and providing a migration path for organizations transitioning from centralized to decentralized communication infrastructure. Enterprise teams in the UK and Canadian financial sectors have begun evaluating peer-to-peer messaging systems for internal communication use cases where regulatory requirements for data sovereignty and auditability align well with the cryptographic audit trail properties of blockchain-anchored messaging systems.
Web3 Communication Protocol Categories
Messaging Protocols
- XMTP (wallet-to-wallet)
- Waku (P2P relay network)
- Status Messaging
- Matrix (federated)
- Push Protocol (notifications)
Data Sharing Protocols
- IPFS (content addressing)
- libp2p (P2P transport)
- Filecoin (incentivized storage)
- Ceramic Network (streams)
- OrbitDB (distributed DB)
Identity Protocols
- DID (Decentralized IDs)
- ENS (Ethereum names)
- Verifiable Credentials
- Sign-In with Ethereum
- Ceramic DID sessions
Messaging Protocols
Messaging protocols in the Web3 communication ecosystem handle the direct exchange of information between identified participants, providing the user-facing communication experience that replaces traditional email, chat, and notification systems. XMTP (Extensible Message Transport Protocol) has emerged as the leading wallet-to-wallet messaging standard, using Ethereum signing keys for authentication and consent management, with an open network of relay nodes that any developer can use to build messaging applications. Its adoption by applications including Coinbase Wallet, Converse, and dozens of other Web3 platforms demonstrates the practical momentum of open messaging protocols over proprietary alternatives. Waku is the dedicated Web3 messaging relay network that evolved from Ethereum’s original Whisper protocol, optimized for censorship-resistant message routing through a decentralized network of relay nodes, with support for Store protocol (retrieving messages missed while offline) and Filter protocol (subscribing to specific content topics).
The Push Protocol (formerly EPNS) provides the notification layer of Web3 communication, enabling decentralized applications to send wallet-addressed notifications to users through a network of notification delivery nodes without requiring any personal contact information from recipients. Matrix, while predating the Web3 movement, has become a critical infrastructure component through its federated architecture that enables independent server operators to collectively provide a global messaging network with no central point of control.
Data Sharing Protocols
Data sharing protocols address the Web3 communication challenge of moving larger data payloads, structured content, and persistent state between participants in a decentralized manner that does not rely on any central file server or content delivery network. IPFS (InterPlanetary File System) is the foundational data sharing protocol of the Web3 ecosystem, using content addressing to identify files by their cryptographic hash rather than their location, ensuring that content retrieved by its hash is always identical to the original regardless of which node delivers it. This property makes IPFS an ideal storage layer for Web3 communication content including message attachments, profile pictures, and communication channel metadata.
Ceramic Network provides the dynamic data layer that IPFS alone cannot supply: because IPFS content addresses are immutable (changing a file produces a different hash), applications that need to update data over time require an additional layer that manages streams of content updates while maintaining a verifiable history. Ceramic’s StreamID system provides a persistent identifier for evolving data like user profiles, social graphs, and application state, with all updates cryptographically signed by the owner and anchored on Ethereum for tamper-proof verification. For enterprise Web3 communication deployments in the USA and UAE requiring large-scale distributed data sharing with economic incentives for reliable storage, Filecoin provides a market-based storage layer where storage providers compete on price and reliability metrics that are verified by the protocol’s proof system.
Identity and Authentication Protocols
Identity and authentication protocols in Web3 communication solve the foundational question of “who is sending this message?” in a way that does not require trusting any central identity provider to verify user identities. Decentralized Identifiers (DIDs), standardized by the W3C, provide a framework for self-sovereign identities where the identifier is controlled by its owner through cryptographic means rather than registered with any central authority. A DID document published on a blockchain or other decentralized registry contains the public keys and service endpoints associated with the identity, enabling any participant to verify messages signed by that identity without consulting any central certificate authority. ENS (Ethereum Name Service) provides the human-readable addressing layer, translating cryptographic wallet addresses into memorable names like alice.eth that can be used as communication addresses across any ENS-compatible Web3 messaging system.
Sign-In with Ethereum (SIWE, EIP-4361) defines the standard authentication flow where users prove ownership of their Ethereum address by signing a structured message, enabling Web3 communication applications to authenticate users with their existing wallet without requiring separate username-password credentials. Verifiable Credentials, another W3C standard, enable participants to carry portable, cryptographically verified claims about their identity, qualifications, and reputation across different Web3 communication systems without requiring the credential issuer to be consulted each time the credential is used.[1]
Storage and Content Delivery Protocols
Storage and content delivery protocols handle the persistent storage and efficient retrieval of Web3 communication content at scale, addressing the challenge that peer-to-peer networks face in reliably serving content to large numbers of simultaneous users without the CDN infrastructure that centralized platforms use. Content addressing through IPFS ensures that Web3 communication content (message attachments, voice messages, images, video) can be retrieved from any node in the network that has cached a copy, automatically distributing load across the network without any central load balancer. Arweave provides permanent, pay-once storage that ensures communication archives remain accessible indefinitely without ongoing payment obligations, making it suitable for regulatory-compliant message archiving in the UK financial services sector and the UAE’s financial free zones where communication records must be retained for specified periods.
The Swarm storage network, developed by the Ethereum Foundation team, provides an incentivized distributed storage system specifically designed for Web3 communication applications, with built-in streaming capabilities for real-time content delivery and a bandwidth incentivization model that rewards nodes for serving content to other network participants. These storage protocols collectively provide the infrastructure for Web3 communication systems to store and deliver content reliably without any dependence on centralized content delivery infrastructure.
How Web3 Communication Networks Work?
Web3 Message Journey: From Sender to Recipient
Step 1: Message Composition & Encryption
Sender composes message in the application. The client generates an end-to-end encryption envelope using the recipient’s public key (derived from their wallet address or DID document), ensuring only the recipient’s private key can decrypt the content.
Step 2: Signature & Authentication
The sender’s wallet signs the message payload with their private key, creating a cryptographic signature that proves message authenticity. Any recipient or relay node can verify this signature using the sender’s public wallet address without trusting any third party.
Step 3: Network Publication
The signed, encrypted message is published to the decentralized communication network. In Waku-based systems, the message is published to a content topic that recipient nodes are subscribed to. In XMTP, it is delivered to the recipient’s XMTP inbox on the relay network.
Step 4: Peer Relay & Propagation
Relay nodes in the network propagate the encrypted message to connected peers using the gossip protocol, ensuring the message reaches multiple network nodes for resilience. No relay node can read the message content due to end-to-end encryption.
Step 5: Recipient Decryption & Delivery
The recipient’s client retrieves the encrypted message from the network, decrypts it using their private key (which never leaves their device), verifies the sender’s signature, and delivers the plaintext to the user’s interface with cryptographic proof of sender authenticity.
Benefits of Web3 Communication
Enhanced Privacy and Security
Enhanced privacy is the most immediately tangible benefit of Web3 communication for users transitioning from centralized platforms, and the technical mechanism that delivers this privacy is fundamentally more robust than the “privacy policies” and “encryption” claims that Web2 platforms make. In Web2 platforms like Gmail, Slack, and even Signal (which does encrypt messages but requires a phone number linked to your real identity), the platform operator has some form of access to user metadata at minimum: who is communicating with whom, when, and at what frequency. This metadata is arguably more revealing than message content for many surveillance purposes, as it reveals relationship graphs, communication patterns, and behavioral rhythms that can infer political affiliations, business relationships, and personal circumstances.
Web3 communication protocols address metadata protection through several complementary mechanisms: onion routing for message envelope obfuscation, anonymous relay networks that hide originating addresses, and pseudonymous wallet identities that separate communication identity from real-world identity. For enterprises in the UK financial services sector subject to GDPR and the UAE entities subject to Federal Law No. 45 of 2021, Web3 communication’s mathematical encryption guarantees provide a stronger privacy foundation than contractual assurances from centralized platform providers who face sovereign government data requests that they cannot legally disclose.
User Data Ownership
User data ownership in Web3 communication is not a policy commitment but a cryptographic guarantee: because messages are encrypted with keys controlled by the user’s wallet rather than the platform, the platform has no ability to access, sell, or share message content regardless of commercial incentives or regulatory pressure. This structural data ownership extends beyond message content to the user’s entire communication identity: their contact graph, message history, group memberships, and reputation all exist as data controlled by the user’s cryptographic keys rather than stored in a corporate database that the user can access only as long as the company chooses to provide access. Ceramic Network’s decentralized data streams demonstrate this principle practically: user profile data, social connections, and application settings stored in Ceramic streams are controlled by the user’s DID and can be updated, deleted, and migrated by the user using their wallet, with no Ceramic operator able to modify or restrict access to user-owned data.
The practical significance for professional users in the USA, Canada, and UAE is substantial: professionals who build communication networks representing years of relationship cultivation need assurance that this asset is not at risk of being lost through platform discontinuation, account suspension, or corporate acquisition that changes platform policies. Web3 communication’s data ownership model provides this assurance cryptographically rather than contractually.
Censorship Resistance
Censorship resistance in Web3 communication is a property of network architecture rather than operator policy, and understanding the distinction between architectural censorship resistance and policy-based censorship promises is essential for evaluating Web3 communication systems. When a centralized platform like Twitter or WhatsApp claims to “not censor” users, this is a policy claim that can be reversed at any time by regulatory pressure, advertiser pressure, or change of ownership. When a Web3 communication network like Waku or XMTP claims censorship resistance, this reflects the mathematical impossibility of any single party blocking messages on a network with thousands of geographically distributed relay nodes.
To effectively censor a sufficiently decentralized network, an attacker would need to simultaneously disable or control the majority of relay nodes worldwide, which is economically prohibitive and logistically nearly impossible for most adversaries. This property is of particular value for users in jurisdictions where government communication monitoring or restriction is a realistic concern, but it is also directly relevant for enterprises in the USA, UK, and Canada who need assurance that communication infrastructure will remain available and unaltered during competitive crises, regulatory investigations, or security incidents where a centralized platform provider might receive legal orders affecting communication availability.
Transparency and Trust
Transparency in Web3 communication networks enables a fundamentally different trust model than the “trust us” approach of centralized platforms, replacing unverifiable claims about platform behavior with cryptographically verifiable proofs of protocol adherence. When Lens Protocol claims that user profiles are owned by users and can be carried across applications, this is not a promise but a demonstrable property of the deployed smart contracts that any developer can independently verify by reading the contract code on Ethereum. When XMTP claims that messages are end-to-end encrypted and relay nodes cannot read message content, this is a verifiable cryptographic property of the protocol’s implementation that security researchers can audit in the open-source codebase.
Blockchain-anchored governance adds another dimension of transparency: every change to a Web3 communication protocol’s rules is recorded immutably on the blockchain with a timestamp and a record of which governance addresses voted for and against the change, creating an auditable history of protocol evolution that any participant can review. This transparency level is qualitatively different from the opacity of centralized platform governance where rule changes are made by internal teams without public record, user input, or verifiable commitment to consistency.
Challenges in Web3 Communication
Scalability Issues
Scalability is the most significant technical challenge facing Web3 communication networks, as the gossip-based message propagation and distributed consensus mechanisms that provide decentralization and censorship resistance inherently create overhead that limits throughput compared to optimized centralized systems. A centralized messaging platform like WhatsApp can process tens of billions of messages daily because every message travels through a small number of highly optimized server clusters. A decentralized communication network that propagates messages through gossip protocol across thousands of nodes must solve the challenge of ensuring messages reach all relevant nodes efficiently without creating bandwidth congestion from redundant propagation paths. The Waku protocol’s active research program on GossipSub optimizations, bandwidth incentivization, and sharding-based message topic distribution represents the current state of Web3 communication scalability solutions. Sharding divides the message space into topic-based partitions where different subsets of nodes handle different content topics, reducing the per-node bandwidth requirements and enabling the network to scale with the number of participating nodes. Layer 2 scaling solutions for blockchain-anchored communication, where messages are batched into rollup transactions, provide another avenue for improving throughput while maintaining the security properties of Layer 1 blockchain anchoring for message authentication and governance.
| Challenge | Current State | Mitigation Approaches | Maturity |
|---|---|---|---|
| Message throughput | Lower than Web2 at scale | Sharding, L2 rollups | In progress |
| Latency vs centralized | Higher for gossip routing | Light push, dedicated nodes | Improving |
| Mobile battery/data | Relay network intensive | Light clients, push services | Active research |
| User onboarding | Wallet-first is a barrier | Embedded wallets, social login | Deployed solutions |
| Key management | Loss = account loss | Social recovery, MPC wallets | Deployed solutions |
| Regulatory compliance | Evolving globally | Zero-knowledge compliance proofs | Early research |
| Spam prevention | No central moderator | Token-gating, ZK reputation | Partial solutions |
User Adoption Barriers
User adoption barriers for Web3 communication are primarily rooted in the complexity gap between the familiar experience of centralized messaging apps and the wallet-first interaction pattern of most Web3 communication systems. The requirement to understand and manage cryptographic keys before sending a first message is a fundamental UX challenge that has limited Web3 communication adoption primarily to blockchain-native users who have already navigated wallet setup for other Web3 applications. Addressing this barrier requires applying the same embedded wallet and social login techniques that are transforming Web3 gaming and DeFi onboarding to the communication context: platforms like XMTP have begun supporting message account creation from social login-generated embedded wallets, enabling users to start communicating with a Web3-powered messaging app using just their email address while the wallet complexity is managed transparently by the application.
The network effect challenge compounds the adoption barrier: users are most willing to adopt a new communication platform when their existing contacts are already there, and a new Web3 messaging system must cross a critical threshold of adoption before it provides enough contact network to compete with established platforms. Federated protocols like Matrix address this through server federation that allows different user communities to communicate across organizational boundaries, and through bridge implementations that enable Matrix users to communicate with users on centralized platforms like Slack and Discord during the transition period.
Technical Complexity
Technical complexity in Web3 communication stems from the layered architecture of protocols, the novelty of cryptographic identity systems, and the ongoing evolution of the underlying standards that makes building on unstable APIs a significant investment risk. The Web3 communication protocol ecosystem is actively evolving, with major standards changes like XMTP’s v3 protocol release introducing breaking changes that require application developers to update their integrations. Unlike Web2 communication APIs from large platforms like Twilio or AWS that provide stable, backward-compatible interfaces, Web3 communication protocols are maintained by smaller communities that must balance innovation with backward compatibility, sometimes choosing protocol improvements over API stability.
Key management complexity is a recurring technical challenge: applications must handle the generation, storage, and recovery of cryptographic keys that cannot be reset by any administrator if lost, requiring sophisticated key management UX that does not compromise security. Zero-knowledge proof integration, which enables privacy-preserving credential verification and spam prevention in Web3 communication, requires specialized cryptographic expertise that is in short supply globally. Despite these complexities, the tooling ecosystem has matured significantly, with frameworks like wagmi, viem, and XMTP’s own SDK reducing the implementation complexity for common Web3 communication integration patterns to levels comparable with Web2 API integration.
Regulatory Concerns
Regulatory concerns around Web3 communication represent a genuine tension between the censorship-resistance properties that make these systems valuable and the compliance requirements that regulators in the USA, UK, UAE, and Canada apply to communication infrastructure. The Financial Crimes Enforcement Network (FinCEN) in the USA and the Financial Conduct Authority in the UK have begun examining how anti-money-laundering and counter-terrorism-financing regulations apply to pseudonymous communication infrastructure that could be used for coordinating illicit activity. GDPR in the UK and EU presents a nuanced challenge: the regulation’s right-to-erasure requirement conflicts with blockchain’s immutability when personal data is stored on-chain, requiring careful architecture that stores personal data off-chain with only cryptographic references on-chain.
The UAE’s Federal Law No. 45 on Personal Data Protection and its evolving regulations on virtual asset service providers create a complex compliance landscape for Web3 communication deployments serving UAE-based enterprises. Zero-knowledge proof technology offers a promising technical path through this regulatory tension: ZK proofs can demonstrate compliance properties (such as a user meeting KYC requirements or a message not containing prohibited content) without revealing the underlying personal data, enabling privacy-preserving regulatory compliance that is structurally impossible in traditional communication architectures.
Decentralized Messaging Apps
Decentralized messaging apps use Web3 protocols to provide secure, peer-to-peer communication without relying on central servers. Apps like Status offer chat, wallet, and browsing features in one platform, while XMTP-based apps focus on easy integration with wallets for seamless messaging. These apps often include token-based access and end-to-end encryption, giving users more privacy, control, and a censorship-resistant alternative to traditional messaging platforms.
Web3 Social Platforms
Web3 social platforms allow users to own their profiles, content, and connections instead of relying on centralized platforms. Protocols like Lens store user data on blockchain and enable multiple apps to share the same social graph. Others like Farcaster use hybrid systems for better performance. This approach ensures data portability, censorship resistance, and gives users full control over their digital identity and social interactions.
Business Communication in Web3
Web3 communication is becoming important for businesses that need secure and private communication. Industries like finance, legal, and healthcare benefit from end-to-end encryption, tamper-proof records, and decentralized storage. This reduces reliance on centralized platforms and improves data protection. Web3 communication also allows controlled access and verifiable records, making it ideal for handling sensitive information across global teams.
Integration with AI and IoT
The integration of AI and IoT with Web3 communication is enabling direct, secure machine-to-machine interaction without human involvement. AI agents can use blockchain-based identities (wallets) to send messages, verify actions, and even perform transactions autonomously. Similarly, IoT devices can communicate through decentralized networks, ensuring reliability even if central servers fail. This is useful for systems like smart cities, environmental monitoring, and automated services. Web3 communication ensures these interactions are secure, censorship-resistant, and verifiable. Projects like decentralized IoT networks show how devices can operate independently while maintaining trust and efficiency through blockchain-based communication systems.
Growth of Decentralized Applications (dApps)
As decentralized applications (dApps) grow, the need for Web3 communication is increasing. Each dApp whether in DeFi, NFTs, DAOs, or gaming—requires secure and direct communication with users. For example, DeFi apps notify users about risks, DAOs need discussion platforms for governance, and NFT platforms support peer-to-peer deals. Using centralized communication tools would weaken decentralization, so developers prefer Web3-based messaging systems. This demand is driving innovation, better tools, and improved user experience. As more dApps adopt decentralized communication, it is accelerating the overall growth and mainstream adoption of Web3 technology across different industries.
Emerging Communication Protocol Innovations
Web3 communication is rapidly evolving with new innovations that improve privacy, security, and scalability. Technologies like zero-knowledge proofs allow users to verify information (like identity or reputation) without revealing full details. Messaging Layer Security (MLS) is being integrated to enable secure and scalable group chats. Additionally, decentralized identity systems allow users to share only necessary information, such as age or credentials, without exposing full identity. These advancements help Web3 communication systems become more efficient and user-friendly while maintaining decentralization. Overall, these innovations are closing the gap between Web2 and Web3 communication capabilities.
Custom Web3 Communication Solutions
Custom Web3 communication solutions are built by analyzing existing business communication systems and gradually shifting them to decentralized alternatives. Instead of replacing everything at once, companies focus on specific use cases like secure cross-border communication. Developers often use existing protocols like XMTP, Waku, or libp2p to save time and ensure reliability. Custom smart contracts can be added to manage access, governance, and compliance based on business needs. This approach allows enterprises to adopt Web3 communication in a practical, scalable way while maintaining security, flexibility, and operational continuity during the transition.
Integration with Existing Systems
Many businesses prefer integrating Web3 communication with their current systems rather than replacing them completely. Bridge solutions allow Web3 protocols to connect with platforms like Slack, Discord, or email, enabling smooth communication across systems. API gateways help existing applications send and receive messages through decentralized networks without complex changes. Identity integration allows employees to log in using familiar tools while Web3 handles security in the background. Hybrid setups also help meet compliance requirements by combining decentralized communication with traditional data storage, making adoption easier and more practical.
Security and Scalability Support
Ensuring security and scalability in Web3 communication requires careful planning and ongoing management. It starts with identifying potential risks, then selecting protocols that protect against threats like data interception or censorship. Regular monitoring and testing help maintain performance as usage grows. Unlike centralized systems, Web3 requires tracking multiple nodes instead of one server. Scalability is improved through distributed networks and load testing. For high reliability, systems use multiple relay nodes across regions with automatic failover. This decentralized approach provides strong security, better uptime, and resilience compared to traditional communication systems.
Authoritative Standards for Web3 Communication Deployments
Standard 1: Private keys used for Web3 communication signing must never be stored on application servers. All signing operations must occur client-side on the user’s device or within their wallet software to prevent server-side key compromise.
Standard 2: Message encryption keys must be rotated regularly using forward secrecy mechanisms like the Double Ratchet algorithm, ensuring that compromise of a current key does not enable decryption of historical messages.
Standard 3: All personal data referenced in Web3 communication systems must comply with applicable data protection regulations in the user’s jurisdiction. GDPR, PIPEDA, and UAE PDPL require distinct compliance implementations.
Standard 4: Communication protocol smart contracts must be formally audited before mainnet deployment. Communication infrastructure handling business-critical or sensitive data requires the same security review rigor as financial contracts.
Standard 5: Decentralized communication deployments must implement fallback mechanisms for offline message storage and delivery to ensure messages are not lost when recipients are temporarily offline or disconnected from the relay network.
Standard 6: Identity recovery mechanisms must be implemented for all Web3 communication deployments. Loss of private keys without recovery means permanent loss of communication identity; social recovery and MPC wallet solutions must be offered to users.
Standard 7: Spam prevention mechanisms must be implemented at the protocol level before production deployment. Unprotected Web3 communication endpoints have been overwhelmed by automated spam in multiple real-world deployments.
Standard 8: Cross-chain communication implementations must verify message provenance on the originating chain before acting on message content, preventing cross-chain spoofing attacks where false messages appear to originate from trusted contracts.
Build Your Web3 Communication Infrastructure
Our team designs and deploys decentralized communication systems for enterprises across USA, UK, UAE, and Canada. Protocol selection to production deployment.
Frequently Asked Questions
Web3 communication refers to information exchange systems that operate without centralized intermediary servers controlling the routing, storage, or validation of messages. Unlike Web2 communication platforms like WhatsApp or Slack where a corporation owns and controls all message infrastructure, Web3 communication uses peer-to-peer networks, cryptographic identity systems, and blockchain-anchored governance to distribute authority across thousands of independent nodes. This means no single company can read messages, block users, or shut down the network unilaterally.
The main Web3 communication protocols span four functional categories. Messaging protocols include XMTP for wallet-to-wallet messaging, Waku for peer-to-peer relay networking, Status for comprehensive decentralized messaging, and Push Protocol for wallet-addressed notifications. Data sharing protocols include IPFS for content-addressed file distribution and Ceramic Network for mutable decentralized data streams. Identity protocols include DIDs, ENS, and Sign-In with Ethereum. Transport protocols like libp2p provide the underlying peer-to-peer networking foundation that most Web3 communication systems use.
Web3 communication provides mathematically enforced privacy through end-to-end encryption with user-controlled keys, which is fundamentally stronger than the policy-based privacy promises of Web2 platforms. In XMTP and Status implementations, messages are encrypted using the Double Ratchet algorithm before entering the relay network, ensuring relay nodes cannot decrypt message content even if they wanted to. However, metadata privacy (who is communicating with whom) remains an active research challenge that current protocols address only partially through gossip-based routing that obscures originating addresses.
Yes, enterprises across the USA, UK, UAE, and Canada are increasingly adopting Web3 communication infrastructure for specific use cases where centralized platforms create unacceptable risks. Financial institutions use decentralized communication for cross-border M&A discussions where jurisdictionally neutral key custody is required. Legal firms use it for attorney-client privilege communications that cannot be accessed by foreign court orders. The cryptographic audit trails provided by blockchain-anchored messaging also satisfy some financial sector compliance requirements, though regulatory frameworks for decentralized communication are still evolving.
Waku and XMTP are complementary Web3 communication protocols that address different aspects of decentralized messaging. Waku is a peer-to-peer relay network protocol that handles the transport layer: how encrypted messages are routed through a decentralized network of relay nodes. It evolved from Ethereum’s original Whisper protocol and is optimized for censorship-resistant message propagation. XMTP is an application-layer messaging protocol that handles wallet-to-wallet message delivery, consent management, and inbox management, and can use relay networks like Waku for message transport. Applications can use either or both depending on their specific requirements.
Web3 communication systems use several spam prevention mechanisms that do not require any central moderator. Token-gating restricts channel access to holders of specific NFTs or tokens, ensuring only verified community members can send messages to gated spaces. Zero-knowledge reputation systems verify that a sender meets certain criteria without revealing identifying information. Proof-of-work-based rate limiting requires senders to perform computational work before sending messages, making spam economically costly at scale. Consent management systems like XMTP’s opt-in model prevent unsolicited messages from appearing in a user’s primary inbox without the recipient’s prior explicit approval.
Author

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.