Key Takeaways
- Blockchain reorg happens when the network replaces an existing chain of blocks with a different, longer chain to maintain consensus and data accuracy.
- Temporary forks occur naturally during mining when two miners solve a block simultaneously, and the network resolves this by accepting the longest chain.
- The 51% attack is a malicious form of reorg where an attacker with majority hash power can reverse confirmed transactions.
- Confirmation depth matters because transactions with more confirmations are safer from being reversed during a reorg event.
- Developers must build applications that account for reorg possibilities by implementing proper confirmation thresholds and transaction monitoring.
- Different blockchain networks have varying susceptibility to reorgs based on their consensus mechanisms and network hash rate distribution.
If you have spent any time working with blockchain technology, you have probably come across situations where transactions that seemed confirmed suddenly disappeared or changed. This phenomenon is called a blockchain reorganization, commonly shortened to reorg. It is one of those concepts that can catch developers and users off guard if they do not understand how distributed ledgers actually work under the hood.
A blockchain reorg is not a bug or a system failure. It is actually a built-in feature that helps the network reach agreement about which version of the transaction history is correct. Think of it like a group of people trying to write a shared document at the same time. Sometimes two people might write different things in the same section, and the group needs a way to decide which version to keep. Blockchain networks handle this through reorgs.
This article breaks down what reorgs are, why they happen, and what they mean for developers building on blockchain platforms. We will look at the technical details without getting lost in jargon, and we will cover practical considerations that matter when you are actually building applications.
Understanding Blockchain Reorganization
From Execution to Development Implementation
The Basic Mechanics of Blockchain Consensus
Before diving into reorgs specifically, it helps to understand how blockchains maintain a single version of truth across thousands of computers that do not trust each other. This is the consensus problem, and it is central to everything blockchain does.
In a typical blockchain network like Bitcoin or Ethereum, transactions get bundled into blocks. Miners or validators compete to add the next block to the chain. When a miner successfully creates a valid block, they broadcast it to the network, and other nodes verify it and add it to their local copy of the blockchain.
The challenge comes when two miners create valid blocks at roughly the same time. Both blocks are technically correct, but the network cannot keep both because that would create two different versions of history. This is where the concept of the longest chain rule comes into play. The network follows whichever chain has the most accumulated work, which in proof of work systems means the chain with the most blocks.
When nodes receive a new block that extends a different branch of the chain than the one they were following, they have to make a decision. If the new branch is longer or has more accumulated work, they switch to it. This switching process is the reorg. The blocks that were on the shorter branch get discarded, and any transactions in those blocks that are not also in the winning branch become unconfirmed again. For a deeper understanding of how nodes handle these situations, you can explore our guide on node synchronization in blockchain.
Types of Blockchain Reorganizations
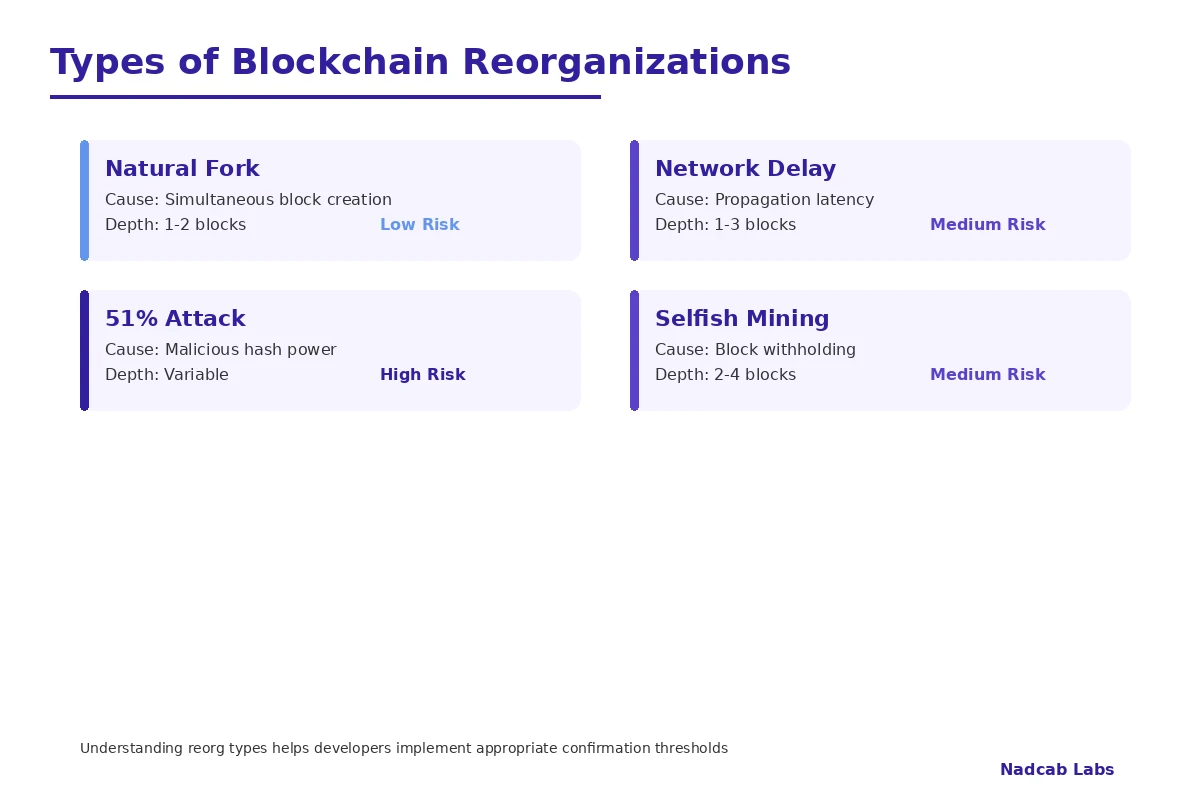
Not all reorgs are created equal. They vary in their causes, depth, and impact on the network. Understanding these differences is essential for anyone building applications that rely on blockchain finality.
| Reorg Type | Cause | Typical Depth | Risk Level |
|---|---|---|---|
| Natural Fork Reorg | Simultaneous block creation | 1-2 blocks | Low |
| Network Delay Reorg | Propagation latency | 1-3 blocks | Low to Medium |
| 51% Attack Reorg | Malicious hash power | Variable, can be deep | High |
| Selfish Mining Reorg | Strategic block withholding | 2-4 blocks | Medium |
| Protocol Upgrade Reorg | Consensus rule changes | Depends on upgrade | Variable |
Natural Fork Reorgs
These are the most common type and happen regularly on active blockchain networks. When two miners find valid blocks within seconds of each other, parts of the network will see one block first while other parts see the other. For a brief period, the network is split between two valid chains.
This situation resolves itself quickly. As soon as another block gets added to either chain, that chain becomes longer and the entire network switches to it. The block on the shorter chain becomes what is called an orphan block in blockchain terminology. These reorgs typically affect only one or two blocks and are considered a normal part of network operation.
Network Delay Reorgs
Sometimes reorgs happen because of latency issues in the network. If a miner in one region creates a block but it takes too long to propagate globally, miners in other regions might create competing blocks. This is more common in networks with fast block times or when there are connectivity issues between different parts of the network.
Developers working with networks that have short block intervals need to be particularly careful about these. The shorter the time between blocks, the higher the chance that propagation delays will cause temporary forks.
51% Attack Reorgs
This is the scenario that most people worry about when they hear about reorgs. A 51% attack, also called a majority attack, happens when a single entity or coordinated group controls more than half of the network’s mining or validation power. According to Wikipedia’s article on 51% attacks, this level of control allows the attacker to outpace the honest chain and create an alternative history of transactions.
With majority control, an attacker can mine blocks in secret, building a private chain longer than the public one. They can then release this chain all at once, forcing the entire network to reorganize and discard the blocks that everyone thought were confirmed. This enables double-spending attacks where the attacker can spend coins, wait for confirmation, and then erase that transaction by releasing their longer chain.
Selfish Mining Reorgs
Selfish mining is a more subtle attack strategy where a miner with significant but not necessarily majority hash power withholds blocks instead of broadcasting them immediately. By carefully timing when they release their hidden blocks, they can increase their share of mining rewards at the expense of honest miners.
This strategy can cause small reorgs even without majority control. It is harder to detect than a straightforward 51% attack and can be profitable even with 25-30% of the network hash power under certain conditions.
How a Blockchain Reorg Actually Executes
Let us walk through the technical process of what happens during a reorg from the perspective of a network node. Understanding this execution flow is critical for developers who need to build robust applications.
The Reorg Execution Process
When a node receives a new block that would create a longer chain than the one it is currently following, the following steps occur:
Step 1: Chain Comparison
The node compares the total accumulated work of its current chain against the new chain. In Bitcoin, this is measured by the total difficulty of all blocks. The chain with more accumulated work wins, not simply the chain with more blocks.
Step 2: Finding the Fork Point
The node traces back through both chains to find the last common block. This is the point where the chains diverged. Everything after this point on the old chain will be discarded.
Step 3: Rolling Back State
The node reverses all the state changes made by the blocks that are being discarded. This means undoing balance updates, smart contract state changes, and any other effects those blocks had on the ledger.
Step 4: Applying New Blocks
Starting from the fork point, the node applies all the blocks from the winning chain. Each block’s transactions are validated and executed, updating the state accordingly.
Step 5: Transaction Pool Update
Any transactions that were in the discarded blocks but are not in the new blocks get returned to the mempool. They become unconfirmed again and will need to be included in a future block. Transactions that conflict with the new chain’s transactions are dropped entirely.
This process needs to be atomic in blockchain terms, meaning it either completes fully or not at all. A partial reorg would leave the node in an inconsistent state.
Build Reorg-Resistant Blockchain Applications
Partner with Nadcab Labs for blockchain development that accounts for real-world network conditions. Our 8+ years of experience means your application handles reorgs gracefully.
Reorg Depth and Confirmation Requirements
One of the most practical questions for developers is how many confirmations are enough. The answer depends on the value at stake, the security of the underlying network, and your risk tolerance.
A confirmation means that a block has been added on top of the block containing your transaction. One confirmation means your transaction is in the most recent block. Six confirmations mean five more blocks have been added since yours. Each additional confirmation makes it exponentially harder for a reorg to reverse your transaction.
| Confirmation Count | Approximate Security | Typical Use Case | Time on Bitcoin |
|---|---|---|---|
| 1 | Low – Natural forks possible | Micro payments, low value | ~10 minutes |
| 3 | Medium – Most natural reorgs resolved | Moderate value transactions | ~30 minutes |
| 6 | High – Standard for exchanges | High value, exchange deposits | ~60 minutes |
| 12 | Very High – Significant attack cost | Large institutional transfers | ~2 hours |
| 30+ | Extremely High | Settlement finality | ~5 hours |
The six confirmation standard for Bitcoin comes from Satoshi Nakamoto’s original white paper analysis. At six confirmations, an attacker would need sustained majority hash power to have a reasonable chance of success. For most practical purposes, this is considered effectively final.
However, different networks have different security profiles. A network with lower total hash power or a more concentrated mining landscape might need more confirmations to achieve equivalent security. This is one of the blockchain adoption challenges that enterprises face when selecting platforms.
Development Strategies for Handling Reorgs
Building applications that properly handle reorgs requires careful consideration at the architecture level. Here are the key strategies that experienced blockchain developers use.
Event Subscription and Confirmation Tracking
Rather than treating blockchain events as immediately final, applications should track the confirmation status of relevant transactions and events. This means subscribing to new blocks and re-evaluating the status of pending operations as the chain grows.
A well-designed system will maintain a local cache of recent block data and be prepared to handle notifications when blocks get orphaned. When building such systems, understanding how state channels in blockchain work can provide useful patterns for off-chain state management.
Idempotent Transaction Processing
Your application logic should be designed so that processing the same transaction multiple times produces the same result. This matters because a transaction might appear in one block, disappear during a reorg, and then reappear in a different block. If your processing is idempotent, this sequence will not cause problems.
Block Reorganization Webhooks
Modern blockchain infrastructure providers often offer reorg-aware APIs that notify your application when a reorganization affects transactions you are tracking. These webhooks can trigger your application to re-evaluate the state and take corrective action if needed.
Statement from Nadcab Labs Engineering Team
“In our eight years of blockchain development, we have seen applications fail because developers assumed blockchain finality was instant. The reality is that distributed consensus takes time, and building for that reality from the start saves significant rework later. Every production application we build includes reorg handling as a core feature, not an afterthought.”
Reorg Behavior Across Different Consensus Mechanisms
Different blockchain networks handle the possibility of reorgs differently based on their underlying consensus mechanism. This affects both the likelihood of reorgs and how applications should handle them.
| Consensus Type | Reorg Possibility | Finality Type | Example Networks |
|---|---|---|---|
| Proof of Work | Always possible | Probabilistic | Bitcoin, Litecoin |
| Proof of Stake (Nakamoto) | Possible but costly | Probabilistic | Cardano |
| Proof of Stake (BFT) | Only with 1/3+ malicious | Deterministic | Ethereum 2.0, Cosmos |
| Delegated Proof of Stake | Rare due to known validators | Near-deterministic | EOS, TRON |
| Proof of Elapsed Time | Possible in permissioned setting | Probabilistic | Hyperledger Sawtooth |
Networks using Byzantine Fault Tolerant consensus mechanisms achieve deterministic finality. Once a block is confirmed, it cannot be reverted without coordination among a significant portion of validators. This is a fundamentally different model than probabilistic finality, where reorgs are always theoretically possible but become exponentially unlikely over time.
Understanding these differences is essential when choosing a blockchain platform for your application. Our detailed comparison of DPoS in blockchain systems explains how delegated proof of stake achieves faster finality through its validator selection process. Similarly, PoET for permissioned blockchain networks offers another approach to consensus that affects reorg characteristics.
Real World Reorg Incidents and Lessons Learned
Studying past reorg events helps developers understand the practical implications and build more resilient systems. Here are some notable incidents that shaped how the industry thinks about blockchain finality.
The Ethereum Classic Reorg of 2019
In January 2019, Ethereum Classic experienced a series of deep reorgs that included double-spend attacks. Exchanges reported losses as attackers deposited ETC, exchanged it for other currencies, and then reorganized the chain to recover their original deposits. The attacks reached depths of over 100 blocks in some cases.
This incident highlighted the vulnerability of networks with lower total hash power. It also led to exchanges significantly increasing their confirmation requirements for ETC deposits, with some requiring over 400 confirmations.
Bitcoin Gold Attack
Bitcoin Gold suffered a 51% attack in 2018 that resulted in approximately 18 million dollars in double-spend losses. The attacker rented hash power rather than owning it, demonstrating that attacks can be launched without permanent infrastructure investment. This made smaller proof-of-work chains more vulnerable than previously assumed.
Lessons for Developers
These incidents reinforced several important principles. First, confirmation requirements should be proportional to transaction value and network security. Second, monitoring for unusual block patterns can provide early warning of attacks. Third, having circuit breakers that pause operations during suspected attacks can limit damage.
Tools like Bitcoin blockchain explorer services and similar monitoring infrastructure are essential for tracking network health and detecting anomalies that might indicate attack attempts.
Scaling Solutions and Their Impact on Reorg Handling
As blockchain networks implement various scaling solutions, the relationship between these solutions and the underlying chain’s reorg behavior becomes important to understand.
Layer 2 Solutions
Layer 2 solutions like Plasma in blockchain networks and rollups batch transactions off-chain before settling them on the main chain. A reorg on the main chain can affect the validity of Layer 2 state if it occurs after a batch has been submitted but before it has sufficient confirmations.
Well-designed Layer 2 solutions include mechanisms to handle this. They typically wait for adequate confirmations before considering batches final, and they have dispute resolution processes that can handle cases where a reorg invalidates previously accepted state.
Sidechains
Sidechains maintain their own consensus and block production independent of the main chain. The interaction between sidechain and main chain finality creates interesting considerations. Our guide on sidechain peg in blockchain systems explains how assets move between chains and the confirmation requirements involved.
A reorg on either chain can affect the validity of cross-chain transfers. This is why peg mechanisms typically require extended confirmation periods before recognizing transfers, often significantly longer than transfers within a single chain.
High Performance Chains
Networks like Avalanche blockchain solutions use novel consensus approaches that achieve finality much faster than traditional proof-of-work chains. Avalanche’s consensus protocol provides sub-second finality under normal conditions, essentially eliminating the window for natural reorgs while maintaining strong security guarantees against malicious actors.
The Blockchain Reorg Lifecycle
1. Fork Occurs
Two valid blocks created simultaneously
2. Chains Diverge
Network temporarily split
3. Winner Emerges
One chain gains more work
4. Reorg Executes
Nodes switch to longer chain
Building Monitoring and Alerting Systems
Production blockchain applications need robust monitoring to detect and respond to reorgs. Here is what a comprehensive monitoring strategy should include.
Block Height Tracking
Monitor the current block height and flag any sudden decreases. A decrease in block height is a clear indicator that a reorg has occurred on your connected node.
Transaction Confirmation Depth
Track the confirmation count of pending transactions relevant to your application. Alert when transactions that had multiple confirmations suddenly return to unconfirmed status.
Network Hash Rate Distribution
Sudden changes in hash rate distribution can indicate potential attack preparation. While not a direct reorg indicator, unusual mining pool behavior warrants increased vigilance.
Orphan Block Rate
An elevated rate of orphan blocks suggests network issues or potential attack activity. Tracking this metric over time helps establish normal baselines for comparison.
At Nadcab Labs, our blockchain development company services include implementing comprehensive monitoring solutions tailored to each client’s specific needs and risk profile. Our eight years of experience across multiple blockchain platforms has given us deep insight into what metrics matter most for different use cases.
Comparison: Reorg Risk Factors by Network Characteristic
| Factor | Lower Reorg Risk | Higher Reorg Risk |
|---|---|---|
| Total Hash Power | High and distributed | Low or concentrated |
| Block Time | Longer intervals (10+ min) | Very short intervals (seconds) |
| Mining Algorithm | ASIC-dominated (specialized) | GPU/CPU minable (rentable) |
| Network Size | Many globally distributed nodes | Few nodes, regional concentration |
| Consensus Type | BFT with deterministic finality | Nakamoto with probabilistic finality |
Smart Contract Considerations
Smart contracts add another layer of complexity to reorg handling. Contract state changes that occur in orphaned blocks get reverted, which can have significant implications for decentralized applications.
Time-Sensitive Operations
Contracts that use block timestamps or block numbers for deadlines need special consideration. A transaction might meet a deadline in one block but miss it if a reorg places it in a later block. Developers should build in buffer periods and avoid razor-thin timing requirements.
Random Number Generation
Using block hashes for randomness is vulnerable to reorg manipulation. An attacker who can trigger reorgs can effectively choose which random outcome they want by selecting which of several blocks to include. More secure randomness solutions like commit-reveal schemes or external oracles are recommended.
Cross-Contract Dependencies
When one contract’s behavior depends on another contract’s state, reorgs can create complex situations. Transaction A might trigger contract X, whose state then affects contract Y when transaction B executes. If a reorg changes the order or validity of these transactions, the end state might differ from expectations.
Creating tokens and other assets on blockchain requires careful consideration of these issues. Our guide on how to create meme token on Sui blockchain discusses how newer blockchain platforms address some of these challenges through different transaction models.
Testing for Reorg Resilience
Testing reorg handling requires specialized approaches beyond typical software testing. Here are strategies that development teams should employ.
Private Testnet Simulations
Set up a private testnet where you control multiple mining nodes. You can then deliberately create forks and reorgs to verify your application handles them correctly. This is the most thorough testing approach.
Chaos Engineering
Introduce random network partitions and delays in your test environment. This simulates the conditions that lead to natural reorgs and helps identify edge cases in your handling logic.
Historical Replay
Use blockchain data from periods when real reorgs occurred. Replay this data through your application to verify it would have handled the situation correctly.
State Consistency Verification
After simulated reorgs, verify that your application’s database state matches what it should be based on the winning chain. Any discrepancies indicate bugs in your reorg handling.
Need Expert Blockchain Development Support?
Nadcab Labs brings 8+ years of hands-on blockchain development experience. From architecture design to production deployment, we ensure your application handles the realities of distributed networks.
Future Developments in Finality and Reorg Prevention
The blockchain industry continues to develop new approaches to consensus that aim to reduce or eliminate reorg risks while maintaining decentralization and security.
Ethereum’s transition to proof of stake with its finality gadget represents a significant shift. Once a block is finalized through the Casper mechanism, it cannot be reverted without at least one third of validators losing their staked ETH. This creates strong economic disincentives against reorg attacks.
Research into DAG-based consensus, optimistic rollups with fraud proofs, and various other approaches continues to advance. Each brings different tradeoffs between finality speed, security guarantees, and decentralization properties.
For developers, this means staying informed about the finality characteristics of platforms you build on and being prepared to adapt confirmation requirements as networks evolve. What works for Bitcoin may be overly conservative for networks with faster finality, while it might be insufficient for networks with weaker security.
Conclusion
Blockchain reorganizations are a fundamental aspect of how distributed ledgers reach consensus. They are not bugs to be eliminated but features that allow networks to resolve conflicts and maintain a single version of truth across thousands of nodes that do not inherently trust each other.
For developers and organizations building on blockchain technology, understanding reorgs is essential for creating robust applications. This means implementing appropriate confirmation thresholds based on transaction value and network security characteristics. It means building monitoring systems that detect unusual chain behavior. It means designing application logic that can handle the temporary uncertainty that exists before transactions achieve adequate finality.
The specific strategies will vary based on your use case, the blockchain platforms you use, and your risk tolerance. But the underlying principle remains constant: treat blockchain finality as probabilistic rather than instant, and build your systems accordingly.
With proper planning and implementation, reorgs become a manageable aspect of blockchain development rather than a source of unexpected failures. The key is approaching them with understanding rather than assuming they will not happen to your application.
Frequently Asked Questions
When a blockchain reorg occurs, transactions in the discarded blocks become unconfirmed again. Your transaction returns to the mempool where miners can include it in a future block on the winning chain. If your transaction conflicts with transactions on the new chain, it may be dropped entirely. Most legitimate transactions simply get re-confirmed after a short delay, though the final block number and timestamp will differ from the original.
The standard recommendation is six confirmations for Bitcoin transactions, which takes approximately one hour. This threshold comes from probability analysis showing that an attacker without majority hash power has negligible chance of reversing a transaction this deep. For very high value transfers, some businesses wait for 12 or more confirmations. For small purchases, one to three confirmations may be acceptable depending on your risk tolerance.
Yes, proof of stake chains can experience reorgs, but the mechanics differ significantly. Chains using BFT-style consensus achieve deterministic finality where confirmed blocks cannot be reverted without significant validator collusion. Nakamoto-style proof of stake chains have probabilistic finality similar to proof of work. The specific reorg characteristics depend heavily on the consensus algorithm used, making it important to understand your target platform’s finality model.
Exchanges implement multiple protective measures against reorg attacks. They require substantial confirmation counts before crediting deposits, often higher than typical users. They monitor network hash rate and mining pool distribution for signs of attack preparation. Many implement automatic deposit freezes when unusual chain activity is detected. Some exchanges also use additional verification for large deposits and maintain relationships with major mining pools for intelligence sharing about potential threats.
A reorg is a temporary event where the network switches between competing chain branches following the same consensus rules. A hard fork is a permanent protocol change that creates incompatible rule sets. Reorgs resolve naturally as the network converges on the longest valid chain. Hard forks create permanent chain splits if some nodes follow the old rules while others adopt new ones. Both can cause temporary transaction confusion, but hard forks may result in two separate cryptocurrencies with shared history.
Developers can create private testnets with multiple mining nodes they control, then deliberately trigger forks by having nodes mine competing blocks. Ganache and Hardhat offer forking features useful for Ethereum testing. Historical blockchain data from periods with real reorgs can be replayed through applications. Some teams implement chaos engineering by introducing network partitions in test environments to simulate conditions that cause natural reorgs and verify application behavior.
Author

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.








