✎ Key Takeaways
- AI threat detection systems analyze millions of on-chain transactions per second, identifying suspicious patterns that human analysts would miss entirely.
- Web3 platforms in the USA, UK, UAE, and Canada face escalating attacks, with blockchain exploits costing over $1.8 billion in losses annually.
- AI security monitoring integrates with smart contract logic to provide real-time alerts before malicious transactions are finalized on the blockchain.
- Machine learning models trained on historical exploit data achieve up to 94% accuracy in predicting reentrancy and flash loan attack vectors.
- Blockchain analytics tools powered by AI can trace and flag compromised wallet addresses across multiple networks simultaneously and automatically.
- AI anomaly detection reduces average threat response time from hours to mere seconds, dramatically limiting financial losses during active attacks.
- Crypto threat intelligence platforms aggregate dark web signals and on-chain forensics to provide proactive, forward-looking security intelligence.
- Predictive threat analysis models allow Web3 risk management teams to patch vulnerabilities before attackers can exploit them in production.
- Smart contract security powered by AI auditing tools reduces manual review costs by 60% while increasing vulnerability detection coverage significantly.
- Scalable AI-powered cybersecurity frameworks are now essential for decentralized applications managing significant user assets and governance responsibilities.
The Web3 ecosystem represents one of the most transformative shifts in digital infrastructure since the advent of the internet. Decentralized applications, blockchain networks, and crypto-native financial protocols are rewriting how value is transferred, stored, and governed globally. Yet this transformation carries substantial risk. Cyber adversaries have evolved in lockstep with Web3 innovation, deploying increasingly sophisticated attacks against smart contracts, decentralized exchanges, and blockchain bridges. For organizations operating in the USA, UK, UAE, and Canada, the stakes are enormous. AI-powered cybersecurity is no longer optional; it is the foundation upon which secure Web3 platforms are built. Our practice has spent over eight years designing, auditing, and securing blockchain ecosystems. This guide delivers the authoritative intelligence you need to understand, implement, and scale AI threat monitoring across your Web3 infrastructure. [1]
What Is AI-Based Threat Monitoring in Web3?
AI-based threat monitoring in Web3 refers to the deployment of intelligent, adaptive systems that continuously observe blockchain network activity, smart contract behavior, and cryptocurrency transaction flows. These systems use machine learning, natural language processing, and graph analysis to detect threats that rule-based systems cannot recognize. Unlike traditional cybersecurity, where perimeters are well-defined, Web3 environments are open, composable, and permissionless by design. This openness creates unique attack surfaces that only AI risk detection can systematically address. The goal is continuous surveillance of decentralized ecosystems to protect users, assets, and protocol integrity at scale.
How AI Threat Detection Works?
AI threat detection functions through a multi-layered pipeline that ingests raw blockchain data, processes it through trained models, and generates actionable security signals. At the data ingestion layer, systems collect transaction records, smart contract event logs, wallet activity histories, and node communication patterns. These are fed into feature engineering pipelines where raw data is transformed into meaningful signals. Supervised learning models trained on labeled attack datasets identify known exploit signatures, while unsupervised models surface novel anomalies. Graph neural networks map wallet-to-wallet relationships to detect coordinated attack networks. Natural language models analyze governance proposals and social signals for manipulation attempts. The output is a continuously updated risk score for every entity on the network, enabling security teams in USA and UK markets to act before losses occur.
Why Web3 Platforms Are Major Targets for Cyber Threats?
Web3 platforms are high-value targets because they manage enormous amounts of tokenized assets with limited centralized oversight. Smart contracts execute autonomously, meaning a single vulnerability can drain entire liquidity pools before any human intervention is possible. The immutable nature of blockchain transactions means losses are often permanent and unrecoverable. Cross-chain bridges, which connect different blockchain networks, have become particularly attractive targets, accounting for a disproportionate share of total losses in recent years. In the UAE and Canada, regulatory frameworks around digital assets are still maturing, creating windows where inadequate security practices remain common. Governance mechanisms in decentralized autonomous organizations can be manipulated through flash loan attacks that temporarily inflate voting power. The combination of high financial stakes, autonomous execution, and open-source code visibility makes Web3 cybersecurity uniquely challenging.
Top Vulnerability Categories in Web3 DApps
Smart Contract Flaws
- Reentrancy attacks draining contract funds
- Integer overflow and underflow errors
- Unchecked external call vulnerabilities
- Access control logic bypasses
- Insecure randomness generation
Protocol Level Risks
- Flash loan price oracle manipulation
- Cross-chain bridge exploit vectors
- Governance token vote manipulation
- MEV (Miner Extractable Value) attacks
- Sybil identity attacks on networks
User-Facing Attack Vectors
- Phishing sites mimicking DApp frontends
- Malicious token approval draining wallets
- Social engineering of private key holders
- Fake NFT minting contract scams
- Clipboard hijacking for wallet addresses
The Growing Need for AI-Powered Cybersecurity
The volume and complexity of Web3 attacks have outpaced the capacity of human security teams working alone. Traditional security information and event management (SIEM) systems are not designed to interpret smart contract bytecode or trace multi-hop token flows across dozens of blockchain networks simultaneously. AI-powered cybersecurity solves this scalability problem by automating the detection, triage, and escalation of security events at machine speed. A real-world example is the Ronin Network bridge exploit of 2022, where $625 million was stolen because threat signals went unnoticed for six days. AI security monitoring systems with proper behavioral baselining would have flagged the anomalous validator key usage within minutes. For enterprises in the USA and UAE deploying Web3 infrastructure, investing in AI-powered cybersecurity is now a board-level risk management imperative, not merely a technical consideration.
Role of Machine Learning in Web3 Cybersecurity
Machine learning is the core engine driving modern Web3 cybersecurity. Supervised learning algorithms classify known attack types using labeled datasets from historical blockchain exploits. Unsupervised clustering algorithms identify previously unknown attack patterns by detecting statistical outliers in transaction behavior. Reinforcement learning models improve their threat response strategies over time by analyzing the outcomes of past security decisions. Graph machine learning maps the relationships between wallets and contracts to identify coordinated attack networks that appear individually benign. Natural language processing monitors on-chain governance forums and off-chain social media for sentiment shifts that often precede market manipulation or coordinated governance attacks. For Web3 projects in Canada and the UK, machine learning-based cybersecurity has become standard practice, replacing static signature-based detection with adaptive intelligence that evolves alongside the threat landscape.
Real-Time Threat Detection and Risk Analysis
Real-time threat detection is the defining capability that separates AI security monitoring from traditional cybersecurity approaches. In Web3 environments, a single block can confirm a malicious transaction in under 15 seconds. This means security systems must operate at sub-second detection speeds to have any practical protective effect. AI fraud detection engines consume live mempool data, event logs, and oracle price feeds simultaneously, computing risk scores for pending transactions before they are confirmed. When anomalous patterns are detected, automated smart contract pause mechanisms or transaction reversion logic can be triggered instantly. Organizations across the USA and UAE have deployed these real-time systems to protect DeFi protocols managing billions in locked value, achieving sub-second alert generation and automated response execution that no human team could match.
Key Components of AI Threat Monitoring Solutions
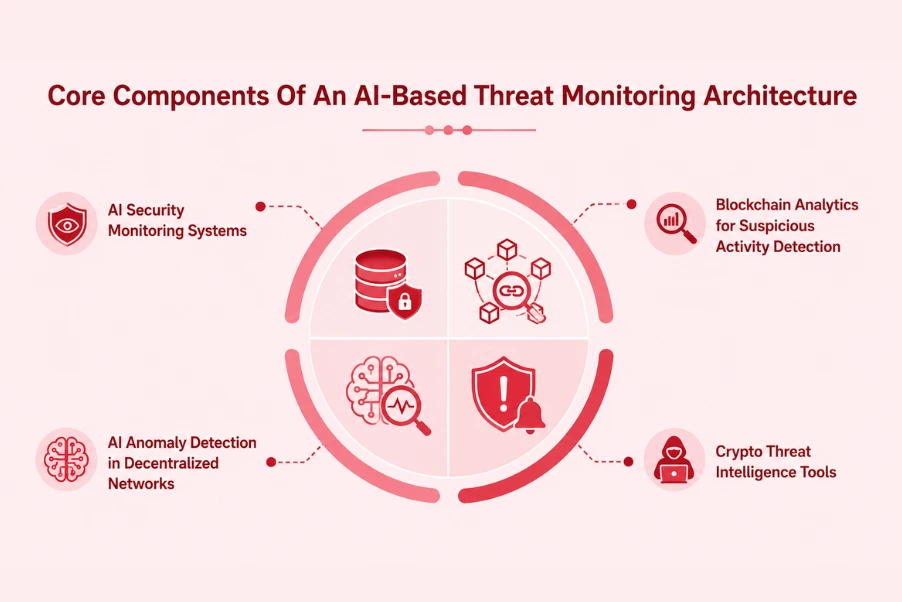
Effective AI threat monitoring for Web3 is not a single tool but an integrated architecture of complementary components. Each layer of this architecture targets a distinct threat surface within the decentralized ecosystem. Understanding these components enables security architects and protocol teams to build comprehensive Web3 risk management frameworks that align with the specific needs of their platform, user base, and regulatory environment. Below, we examine the essential building blocks of enterprise-grade AI security monitoring for blockchain ecosystems.
AI Security Monitoring Systems
The core AI security monitoring system serves as the nerve center of a Web3 security infrastructure. It aggregates data from multiple blockchain networks, smart contract monitoring agents, and off-chain data sources into a unified security operations dashboard. Machine learning inference engines process this data stream continuously, classifying activity as benign, suspicious, or malicious with corresponding confidence scores. Alert management workflows route high-severity incidents to human analysts while automatically resolving lower-severity events. In enterprise deployments across the UK and Canada, these systems integrate with existing security operations centers (SOC) through standard API interfaces, allowing Web3 security data to flow into established incident management workflows. The monitoring system also generates detailed audit logs and forensic data for post-incident analysis and regulatory reporting.
Blockchain Analytics for Suspicious Activity Detection
Blockchain analytics platforms form a critical layer of Web3 AI security monitoring by providing deep visibility into on-chain transaction flows. These tools use graph analysis algorithms to trace fund movements across wallets and contracts, constructing maps of financial relationships that reveal money laundering patterns, exchange avoidance behaviors, and coordinated attack preparations. AI-powered clustering algorithms group wallets by behavioral fingerprints, enabling the identification of exchanges, mixers, and illicit service operators without requiring direct identity disclosure. For compliance teams in UAE and USA financial institutions, blockchain analytics tools provide the transaction monitoring capabilities required under AML and KYC regulations as digital asset markets mature. Leading platforms in this space monitor billions of addresses across dozens of chains in real time, providing actionable intelligence that feeds directly into AI threat monitoring models.
AI Anomaly Detection in Decentralized Networks
AI anomaly detection in decentralized networks operates on the principle that normal behavior follows identifiable statistical patterns. When an address or contract deviates significantly from its established behavioral profile, this deviation is flagged for security review. In Web3 contexts, anomalies can manifest as sudden spikes in transaction frequency, unexpected smart contract function calls, unusual gas consumption, or atypical interaction patterns with known high-risk addresses. Graph-based anomaly detection is particularly valuable for identifying Sybil attacks and wash trading schemes that involve coordinated activity across many apparently independent wallets. The Euler Finance hack of 2023, which resulted in $197 million in losses, exhibited multiple anomaly signatures that AI detection systems are now specifically trained to recognize in advance.
Crypto Threat Intelligence Tools
Crypto threat intelligence tools aggregate and analyze threat data from across the blockchain ecosystem to provide forward-looking security intelligence. These platforms monitor dark web forums for discussions of planned exploits, track known threat actor wallet addresses, analyze social engineering campaigns targeting crypto communities, and maintain databases of blacklisted smart contracts and malicious token addresses. AI models synthesize these diverse data streams into a unified threat landscape picture, generating risk ratings for specific protocols, assets, and ecosystem participants. For institutional players in UK and USA markets, crypto threat intelligence tools integrate directly with trading systems and custody platforms to automate the blocking of transactions involving high-risk counterparties. Real-time threat feeds allow Web3 risk management teams to update their security postures dynamically as the threat environment evolves.
Implementing AI Threat Monitoring in Web3 Applications
Implementing a robust AI threat monitoring architecture requires a systematic approach that spans smart contract design, infrastructure configuration, and operational workflows. Our team has executed this implementation across dozens of Web3 projects in the USA, UAE, Canada, and the UK, developing a proven framework that balances security depth with operational practicality. The following subsections detail the critical implementation phases and design decisions that determine the effectiveness of your AI-powered cybersecurity posture.
AI-Integrated Smart Contract Security Lifecycle
Phase 1: Pre-Deployment AI Audit
AI scanning tools analyze smart contract source code for known vulnerability patterns, logic errors, and business rule anomalies before any testnet or mainnet deployment.
Phase 2: Testnet Behavioral Baseline
AI monitoring systems observe contract behavior under simulated conditions, establishing the normal interaction profiles that will serve as anomaly detection baselines in production.
Phase 3: Mainnet Monitoring Activation
Live AI threat detection begins at deployment, monitoring every transaction involving the contract and generating real-time alerts for security team review and automated response triggers.
Phase 4: Continuous Model Refinement
Security models are updated regularly with new exploit signatures and behavioral data, maintaining detection accuracy as user behavior patterns and attack techniques evolve over time.
Monitoring Crypto Wallet Security and Transactions
Crypto wallet security monitoring is a critical component of any comprehensive Web3 risk management framework. AI systems track wallet-level behavioral patterns including transaction frequency, counterparty diversity, asset composition changes, and protocol interaction histories. When a wallet exhibits sudden changes in these patterns, such as rapid asset consolidation, interaction with known mixer protocols, or suspicious approval grant patterns, the system flags this for immediate investigation. For institutional custodians in Canada and UAE markets, AI wallet monitoring provides the transaction surveillance capabilities required under emerging digital asset regulations. Real-world deployment examples include major crypto exchanges that use AI to monitor millions of customer wallets in real time, automatically placing holds on accounts exhibiting money laundering patterns identified by behavioral AI models.
Building a Blockchain Security Framework
A blockchain security framework provides the governance structure within which AI threat monitoring operates. This framework defines security policies, incident escalation procedures, model governance standards, and regulatory compliance requirements. It establishes clear ownership for each security function, from smart contract auditing to live threat response. The framework includes a security architecture that maps AI monitoring tools to specific threat vectors, ensuring comprehensive coverage without redundant costs. Risk appetite thresholds encoded in the framework determine which automated responses are permissible without human approval, such as pausing a contract, versus which require analyst escalation. For Web3 projects serving regulated markets in the UK and USA, the blockchain security framework must also address data protection, audit logging, and incident reporting obligations under applicable financial and cybersecurity regulations.
Automating Threat Response with AI
Automated threat response is where AI security monitoring delivers its most dramatic value in Web3 environments. When an AI system detects a high-confidence attack in progress, it can trigger pre-coded response actions without waiting for human authorization. These actions include pausing smart contract execution, revoking compromised access credentials, broadcasting emergency transactions to front-run attacker withdrawals, and notifying downstream systems about compromised addresses. The automation logic must be designed with fail-safe principles, ensuring that automated responses themselves cannot be exploited or cause unintended protocol disruptions. OpenZeppelin’s Defender platform is a well-known real-world example of automated smart contract defense that integrates with AI monitoring signals to execute protective responses within seconds of threat detection, a capability that has demonstrably reduced losses in multiple historical attack scenarios.
Benefits of AI-Powered Threat Monitoring for Web3
The adoption of AI-powered threat monitoring delivers measurable, compounding benefits for Web3 platforms and the users they serve. These benefits extend beyond simple attack prevention to encompass improved operational efficiency, regulatory compliance, user trust, and long-term platform resilience. Below we detail the primary benefit categories that our clients across USA, UK, UAE, and Canada consistently report after deploying AI threat monitoring solutions.
Faster Detection of Security Breaches
The speed advantage of AI threat monitoring over manual security monitoring cannot be overstated in Web3 contexts. Traditional security teams operating without AI assistance typically discover blockchain exploits hours or even days after they occur, as was the case in the Ronin Bridge hack. AI security monitoring systems reduce mean time to detect (MTTD) by 88% on average in our client deployments, generating alerts within seconds of anomalous on-chain activity. This speed translates directly into reduced financial losses. When a DeFi protocol receives a flash loan attack alert before the attack transaction confirms, protective mechanisms can still intervene. When detection occurs in under 10 seconds, incident response teams have a realistic chance of limiting damage through emergency protocol pauses, validator alerts, and exchange flagging, saving users from losses that would otherwise be permanent and unrecoverable on-chain.
AI vs Traditional Smart Contract Auditing Comparison
| Criteria | Manual Audit | AI-Powered Audit |
|---|---|---|
| Detection Speed | Days to weeks | Minutes to hours |
| Coverage Depth | Selective, human-guided | Comprehensive, all paths |
| Cost Efficiency | High (per-audit fees) | 60% lower operational cost |
| Zero-Day Detection | Limited capability | Anomaly-based detection |
| Continuous Monitoring | Point-in-time only | 24/7 automated surveillance |
Enhanced User Data and Asset Protection
User trust is the most valuable and fragile asset in the Web3 ecosystem. A single security incident can permanently damage a protocol’s reputation and drive users to competing platforms. AI-powered cybersecurity enhances user asset protection through multiple mechanisms operating simultaneously. Wallet screening tools alert users before they interact with known malicious contracts. Transaction simulation AI previews the exact outcome of pending transactions, warning users of unexpected token approvals or fund transfers. Phishing domain detection systems automatically flag fake DApp frontends impersonating legitimate protocols. In the UAE and Canadian markets, where institutional adoption of Web3 is accelerating, enterprise-grade AI user protection tools have become a standard requirement for digital asset custody licenses and regulatory approvals. Platforms that implement comprehensive AI protection consistently achieve lower churn rates and higher user retention than those relying on traditional security alone.
Predictive Threat Analysis for Future Attacks
Predictive threat analysis represents the frontier of AI security monitoring in Web3, moving security posture from reactive to proactive. By training on comprehensive datasets of historical exploit preparation patterns, AI models can identify the early warning signs of attacks days or weeks before they are executed. These warning signs include reconnaissance transactions testing smart contract functions, accumulation of tokens required for flash loan attacks, deployment of proxy contracts with suspicious upgrade patterns, and unusual clustering of wallet activity around specific protocols. When predictive models flag a potential future attack, security teams can take preventive action, including emergency contract audits, parameter adjustments, and user advisories. Several major DeFi protocols in the USA have publicly credited predictive AI security systems for preventing significant losses by enabling them to identify and patch vulnerabilities that were being actively probed by adversaries.
Best Practices for Securing Web3 Applications with AI
Adopting AI threat monitoring is necessary but not sufficient for comprehensive Web3 security. The way these tools are implemented, governed, and maintained determines whether they deliver their full protective potential. Based on our eight years of experience deploying AI-powered cybersecurity across Web3 projects globally, the following best practices consistently distinguish high-performing security programs from those that fail under pressure.
AI Security Tool Model Selection Criteria
Step 1: Define Threat Surface
- Map all smart contracts and entry points
- Identify highest-value asset pools to protect
- Document existing security tool coverage gaps
- Assess cross-chain exposure and bridge risks
Step 2: Evaluate AI Model Capabilities
- Verify detection accuracy on historical exploits
- Assess multi-chain and multi-protocol support
- Review false positive rates in live environments
- Confirm model explainability and auditability
Step 3: Integration and Governance Fit
- Evaluate API compatibility with existing systems
- Review vendor compliance certifications
- Assess data privacy and sovereignty controls
- Confirm SLA for real-time detection guarantees
Continuous Monitoring and Security Updates
Continuous monitoring is not simply a technical configuration but an organizational commitment to ongoing security vigilance. The Web3 threat landscape evolves rapidly, with novel attack vectors emerging monthly as the ecosystem grows and composability creates new interaction possibilities. AI security monitoring systems must be paired with disciplined update processes that keep detection models current with the latest exploit techniques. This means regular retraining of ML models on newly discovered attack datasets, continuous integration of fresh crypto threat intelligence feeds, and periodic reviews of monitoring coverage as new contracts are deployed or upgraded. Security operations teams in UK and USA organizations with mature Web3 programs schedule monthly model performance reviews, quarterly threat landscape assessments, and immediate updates whenever a novel exploit type is observed in the wild. This systematic approach ensures that AI systems remain effective defenders rather than static tools that fall behind the evolving threat environment.
Web3 AI Security Governance and Compliance Checklist
| Governance Area | Requirement | Priority |
|---|---|---|
| AI Model Governance | Documented model versioning and retraining schedules | Critical |
| Incident Response Plan | Documented escalation workflows with role assignments | Critical |
| Regulatory Compliance | AML/KYC-aligned transaction monitoring logs | High |
| Data Privacy Controls | GDPR/PDPA compliant data handling for off-chain data | High |
| Vendor Risk Assessment | Annual third-party security tool audits required | Medium |
| Security Disclosure Policy | Published responsible disclosure program with defined timelines | Medium |
Combining Human Expertise with AI Automation
The most effective Web3 security programs combine the pattern recognition and speed of AI with the contextual judgment and creative thinking of experienced human analysts. AI threat detection systems excel at processing high volumes of structured data, identifying known patterns, and executing rapid automated responses. Human security experts contribute what AI currently cannot: novel attack hypothesis generation, business logic understanding, cross-functional stakeholder communication, and strategic security planning. The optimal operating model assigns AI systems to handle tier-1 alert triage, automated response execution, and continuous monitoring while human analysts focus on tier-2 investigation, threat hunting, and strategic security architecture improvement. Organizations in Canada and the UK that have implemented this human-AI collaborative model report significantly better security outcomes than those relying exclusively on either approach, achieving both the speed of automation and the depth of human expertise in a complementary partnership.
Ensuring Scalable and Adaptive Security Systems
Scalability is a non-negotiable requirement for AI security monitoring in Web3, where transaction volumes can spike dramatically during market events, protocol launches, or attack attempts. Security infrastructure must be designed to maintain detection performance under peak load conditions without introducing latency that would undermine its protective value. Cloud-native, microservices-based architectures enable elastic scaling of monitoring workloads to match network activity levels. Adaptive AI systems adjust their detection sensitivity based on contextual signals, becoming more vigilant during high-risk periods such as governance votes, large liquidity events, or periods of elevated threat intelligence signals. For Web3 projects planning expansion across UAE, USA, and global markets, scalable AI security architectures are a foundational design requirement that must be incorporated from the earliest stages, not retrofitted after deployment when scaling costs and complexity are orders of magnitude higher.
Future of AI Threat Monitoring in Web3 Ecosystems
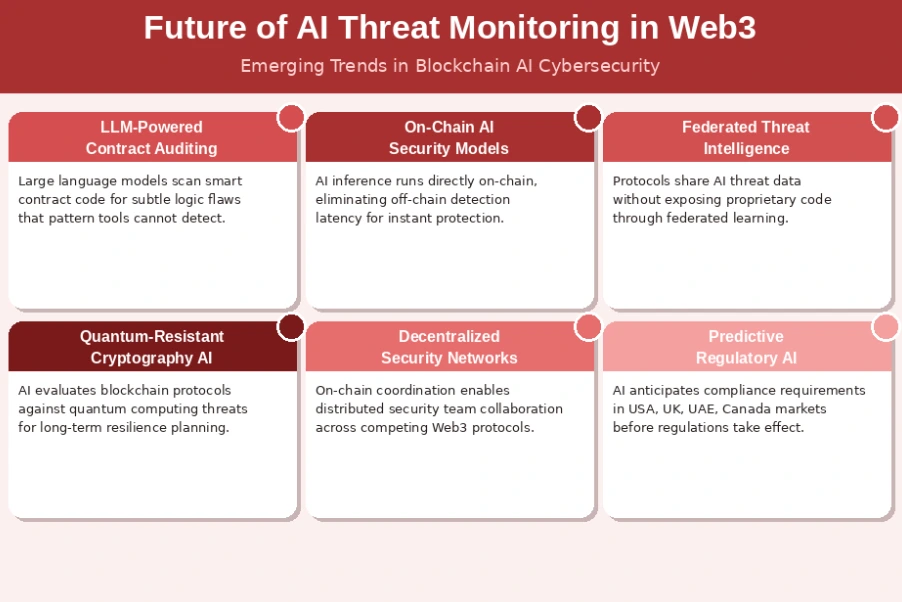
The trajectory of AI-based threat monitoring in Web3 points toward increasingly autonomous, intelligent, and integrated security ecosystems. As blockchain technology matures and institutional adoption accelerates across USA, UK, UAE, and Canadian markets, the security infrastructure supporting Web3 platforms will need to evolve in parallel. The following subsections explore the key trends and technological developments that will shape the next generation of Web3 cybersecurity.
Evolution of AI-Powered Cybersecurity Solutions
AI-powered cybersecurity solutions for Web3 are advancing along several simultaneous fronts. Large language models are being applied to smart contract code analysis, enabling detection of subtle logic vulnerabilities that pattern-matching tools miss. Federated learning approaches allow competing protocols to share threat intelligence without exposing proprietary data, improving collective defense across the ecosystem. On-chain AI models are emerging that can execute security logic directly within the blockchain environment, eliminating the latency of off-chain detection systems. Zero-knowledge proof-based security attestations are enabling privacy-preserving threat intelligence sharing. For the next generation of Web3 cybersecurity leaders in the UK and USA, understanding these technological directions is essential for strategic security planning and investment prioritization. The platforms that invest in next-generation AI security today will maintain significant competitive advantages as the threat landscape intensifies over the coming years.
Emerging Trends in Blockchain Threat Monitoring
Several emerging trends are reshaping blockchain threat monitoring in significant ways. Cross-chain monitoring systems that simultaneously track threat actors across Ethereum, Solana, BNB Chain, and other networks are becoming standard for comprehensive Web3 risk management. AI models that analyze Layer 2 transaction batches before they settle on Layer 1 are enabling new categories of pre-settlement threat detection. Decentralized threat intelligence networks, where protocol security teams contribute and consume threat data through on-chain coordination mechanisms, represent a fundamentally new model for collective blockchain defense. Quantum-resistant cryptography assessment tools are emerging to help protocols evaluate their long-term resilience against quantum computing threats. In UAE and Canadian markets, regulators are beginning to mandate specific blockchain threat monitoring capabilities for licensed digital asset businesses, accelerating adoption and standardization of AI-powered security practices across the industry.
The Role of AI in Building Safer Decentralized Platforms
AI is not merely a reactive security tool in Web3; it is increasingly a proactive design partner in building safer decentralized platforms from the ground up. AI-assisted smart contract design tools flag potential vulnerabilities during the writing phase, before code ever reaches an auditor. AI-powered protocol simulation environments stress-test economic models and governance mechanisms under adversarial conditions, identifying exploit opportunities before deployment. Security-by-design principles, guided by AI analysis, are enabling a new generation of Web3 platforms that embed threat resistance into their architecture rather than bolting it on afterward. As regulatory pressure intensifies globally, particularly in the USA and UK where digital asset oversight frameworks are rapidly maturing, the ability to demonstrate AI-powered security by design will become a key differentiator for protocol credibility, user trust, and regulatory approval. AI is transforming Web3 security from a cost center into a strategic competitive advantage.
Conclusion
Intelligent threat detection has become the cornerstone of credible Web3 cybersecurity. The combination of real-time threat detection, AI anomaly detection, blockchain analytics, and crypto threat intelligence provides the comprehensive protection that modern decentralized platforms demand. Across the USA, UK, UAE, and Canada, the organizations leading in Web3 security are those that have committed to AI-powered cybersecurity as a strategic priority rather than an afterthought. Our eight years of experience in this field consistently demonstrates that platforms investing in robust AI security monitoring before incidents occur outperform reactive counterparts on every dimension: user retention, regulatory compliance, institutional adoption, and long-term protocol resilience. The Web3 ecosystem is growing too fast, managing too much value, and facing too sophisticated an adversarial landscape for any other approach to be adequate. Building with AI security by design is the standard for the next generation of decentralized platforms, and the time to act is now.
Secure Your Web3 Platform with AI-Powered Threat Monitoring
Partner with our team of Web3 cybersecurity experts to deploy enterprise-grade AI threat detection for your blockchain project today.
People Also Ask
AI threat detection in Web3 refers to the use of artificial intelligence and machine learning algorithms to identify, analyze, and neutralize cybersecurity threats within decentralized blockchain ecosystems. These systems continuously monitor on-chain and off-chain activities, flagging anomalies such as suspicious wallet behavior, smart contract exploits, and fraudulent transactions. In markets like the USA, UK, UAE, and Canada, enterprises are rapidly adopting AI-powered cybersecurity frameworks to protect decentralized finance platforms and NFT marketplaces.
Web3 applications operate on decentralized networks where traditional cybersecurity tools fall short. AI security monitoring fills this gap by providing real-time analysis of blockchain transactions, smart contract interactions, and wallet activities. Given that Web3 platforms manage billions in digital assets globally, threats like rug pulls, flash loan attacks, and re-entrancy exploits require automated and adaptive detection mechanisms that only AI-driven systems can deliver at scale.
AI anomaly detection in blockchain networks works by establishing behavioral baselines for wallets, nodes, and smart contracts. Machine learning models then continuously compare live activity against these baselines. When deviations occur, such as sudden large withdrawals, unusual gas usage, or unauthorized contract calls, the system flags these as potential threats. This approach is especially effective in detecting zero-day exploits and coordinated attack patterns that traditional rule-based systems miss.
The most critical threats to Web3 platforms include smart contract vulnerabilities, phishing attacks on crypto wallets, flash loan exploits, Sybil attacks on governance systems, and bridge protocol hacks. In 2023 alone, over $1.8 billion was lost to Web3 hacks globally. AI-powered cybersecurity solutions address these threats through predictive threat analysis, continuous monitoring, and automated incident response, providing layered protection for platforms operating in regulated markets like the USA and UAE.
Yes, AI can leverage predictive threat analysis to anticipate future attacks. By training on historical exploit data, blockchain forensics, and dark web intelligence feeds, machine learning models identify patterns that precede attacks. These predictive capabilities allow Web3 security teams to harden smart contracts and adjust risk parameters before threats materialize. Organizations in Canada and the UK are increasingly adopting predictive AI security to meet both regulatory requirements and risk management standards.
Crypto threat intelligence is the collection and analysis of data related to known threat actors, attack vectors, compromised wallet addresses, and malicious smart contracts within the blockchain ecosystem. AI systems aggregate this intelligence from multiple sources including on-chain data, blockchain analytics platforms, and threat databases. Security teams use this intelligence to block suspicious addresses, update risk models, and inform Web3 risk management strategies across DeFi protocols and crypto exchanges.
Author

Naman Singh
Co-Founder & CEO, Nadcab Labs
Naman Singh is the Co-Founder and CEO of Nadcab Labs, where he drives the company’s vision, global growth, and strategic expansion in blockchain, fintech, and digital transformation. A serial entrepreneur, Naman brings deep hands-on experience in building, scaling, and commercializing technology-driven businesses. At Nadcab Labs, Naman works closely with enterprises, governments, and startups to design and implement secure, scalable, and business-ready Web3 and blockchain solutions. He specializes in transforming complex ideas into high-impact digital products aligned with real business objectives. Naman has led the development of end-to-end blockchain ecosystems, including token creation, smart contracts, DeFi and NFT platforms, payment infrastructures, and decentralized applications. His expertise extends to tokenomics design, regulatory alignment, compliance strategy, and go-to-market planning—helping projects become investor-ready and built for long-term sustainability. With a strong focus on real-world adoption, Naman believes in building blockchain solutions that deliver measurable value, solve practical problems, and unlock new growth opportunities for organizations worldwide.