Ai Overview
Traditional blockchain networks like Ethereum operate on a principle of transparency. DeFi users face impossible economics: a simple swap that costs a few dollars in execution might cost $50 in fees. The sequencer creates a batch containing anywhere from 100 to 10,000 transactions depending on various factors:. She pays 150,000 gas for the approval and swap = 7,500 gwei = 0.
Key Takeaways
- •Zero knowledge proofs enable verification of information without revealing the underlying data, solving the privacy problem in blockchain systems
- •ZK SNARKs and ZK STARKs are the two main types of zero knowledge proof systems, each with distinct advantages for different applications
- •Privacy focused DeFi platforms use zero knowledge proofs to enable confidential transactions that hide sender, recipient, and amounts
- •ZK rollups represent a breakthrough scalability solution that processes multiple transactions off chain while maintaining security through zero knowledge proofs
- •Identity verification using zero knowledge technology allows users to prove credentials without exposing personal information
- •Zero knowledge proofs improve blockchain scalability by reducing on chain data storage while maintaining cryptographic verification
- •Computational complexity and proof generation times are significant challenges in implementing zero knowledge proof systems at scale
- •Zero knowledge smart contracts enable privacy preserving decentralized applications without sacrificing security or auditability
- •Leading blockchain projects like Zcash, Aztec, and StarkNet have demonstrated successful implementation of zero knowledge technologies
- •Future of DeFi will increasingly integrate zero knowledge proofs as regulatory requirements and user demand for privacy continue to grow
Imagine proving your age at a nightclub without showing your ID. Or verifying you have sufficient funds in your bank account without revealing your exact balance. This is exactly what zero knowledge proofs in DeFi accomplish in the digital financial world. Zero knowledge proofs (ZKPs) are cryptographic tools that allow one party to prove they know something to another party without revealing the actual information itself.
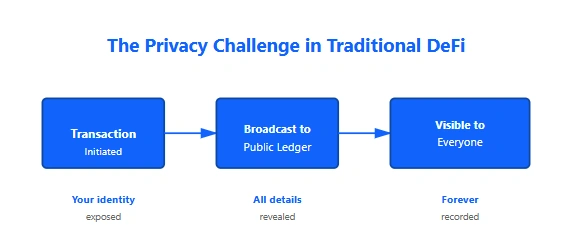
In traditional blockchain systems, every transaction is transparent and visible to everyone. While this transparency ensures security, it compromises privacy. Every DeFi transaction reveals sender, recipient, and transaction amount to the entire network. Zero knowledge proofs solve this privacy paradox by allowing participants to verify transactions and smart contracts without exposing sensitive details.
As blockchain and Web3 continue to reshape the financial landscape, privacy has become paramount. Companies like Nadcab Labs are pioneering privacy focused DeFi solutions using zero knowledge technologies to help institutions and individuals maintain confidentiality while participating in decentralized finance securely and transparently.
Why Privacy is a Challenge in Decentralized Finance?
Traditional blockchain networks like Ethereum operate on a principle of transparency. Every transaction is recorded on a public ledger visible to anyone. While this creates security through visibility, it creates a major privacy problem.
The Transparency Problem: Every DeFi interaction exposes critical information. When you swap tokens on Uniswap, everyone knows your wallet address, the assets you’re trading, the amounts involved, and the exact time of the transaction. This data can be analyzed to reveal your investment strategies, net worth, and financial patterns.
Consider these real world scenarios:
Scenario 1: Front Running A trader sees a large pending transaction in the memory pool and quickly places their own transaction first to profit from the price movement. This is possible only because all transactions are publicly visible.
Scenario 2: Financial Surveillance Blockchain analysis firms track wallet activity to identify users, monitor their transactions, and potentially flag accounts engaged in large DeFi operations to authorities or competitors.
Scenario 3: Competitive Intelligence Hedge funds analyze competitor wallet addresses to understand their trading strategies, portfolio allocations, and investment timing.
Zero knowledge proofs eliminate these problems by allowing transactions to be verified and settled without revealing the participants or amounts involved. This is where privacy in DeFi transactions becomes essential, and why zero knowledge cryptography is becoming a fundamental component of modern decentralized finance.
What Zero Knowledge Proofs Are and How They Work
A zero knowledge proof is a cryptographic method where one party (the prover) can prove to another party (the verifier) that a statement is true without revealing any additional information beyond the truth of the statement itself.
The Password Analogy: Imagine you need to prove to a website that you know your password without actually entering it. The website sends you a random challenge. You use your password with that challenge to generate a unique response. The website verifies this response matches what your password would produce, but never sees the password itself. This is how zero knowledge proofs work in cryptography.
The Three Properties of Zero Knowledge Proofs
Completeness
If the statement is true, an honest prover can always convince the verifier of this fact with high probability.
Soundness
If the statement is false, a dishonest prover cannot convince an honest verifier with more than negligible probability.
Zero Knowledge
The verifier learns nothing except that the statement is true, gaining no additional information.
div style=”max-width: 900px; margin: 0 auto; padding: 0; font-family: ‘Segoe UI’, Tahoma, Geneva, Verdana, sans-serif; line-height: 1.8; color: #333;”>
How Zero Knowledge Proofs Work: Step by Step
Understanding zero knowledge proofs requires breaking down the process into digestible steps. While the underlying cryptography is complex, the fundamental concept is surprisingly intuitive. Let’s walk through a concrete example that demonstrates how zero knowledge proofs actually work in practice.
Step 1: The Prover Has a Secret
The process begins with one party called the prover who possesses a secret piece of information. This could be a password, a private cryptographic key, knowledge of a solution to a mathematical problem, or information about their identity or assets.
Real World Analogy: Imagine you have a secret password to a safe: “BLOCKCHAIN2024”. You want to prove to someone that you know this password without actually telling them what it is. The zero knowledge proof is the mechanism that allows you to do exactly this.
In blockchain and DeFi contexts, the secret might be:
Private Key: Your cryptographic key that proves you own certain assets without revealing the key itself
Account Balance: Proof that you have sufficient funds for a transaction without revealing your exact balance
Transaction History: Proof that funds were correctly transferred from input to output without revealing amounts or participants
Personal Attributes: Proof that you meet certain criteria (age, jurisdiction, credit score) without sharing the actual data
The critical point is that the prover knows the secret but has not yet revealed it. This is the starting position from which everything else flows.
Step 2: The Verifier Issues a Challenge
The second party, called the verifier, wants to confirm that the prover actually knows the secret. The verifier creates a challenge, which is typically a random question or test that can only be answered correctly if the prover truly knows the secret.
Continuing Our Analogy: The verifier asks a random question like: “If you add 7 to the first digit of your password and multiply by 3, what is the result?” The prover who knows the password is “BLOCKCHAIN2024” would calculate: (2+7) x 3 = 27. But someone guessing would have only a tiny probability of getting the right answer.
Why Randomness Matters
The challenge must be random and unpredictable. If the verifier asks the same question every time, a dishonest prover could memorize the answer without knowing the actual secret. By making the challenge random, the verifier ensures that the prover must genuinely know the secret to have a high probability of answering correctly.
In cryptographic systems, this randomness is generated using secure random number generators. The challenge becomes a mathematical problem whose answer depends on both the secret and the random challenge value.
Types of Challenges
Interactive Challenges: The verifier and prover go back and forth, with the verifier issuing multiple random challenges and the prover responding to each one.
Non-Interactive Challenges: A single challenge is issued, and the prover generates a proof that responds to it without further interaction needed.
For blockchain applications, non-interactive proofs are preferred because the verifier (the blockchain network) doesn’t need to engage in back and forth communication. The prover generates a single proof that can be verified by millions of nodes independently.
Step 3: The Prover Generates the Proof
This is the crucial step where the prover uses their secret knowledge to generate a mathematical proof that responds to the verifier’s challenge. The proof is constructed in such a way that it only reveals information about the truth of the claim, not about the secret itself.
The Proof Generation Process
The prover performs the following operations:
1. Encoding the Secret: The prover takes their secret and converts it into a mathematical format that can be used in cryptographic computations. This encoding preserves the structure of the secret but makes it suitable for mathematical manipulation.
2. Applying Cryptographic Functions: The encoded secret is processed through sophisticated cryptographic functions (like polynomial commitments or cryptographic hash functions) that create intermediate values. These functions have the property that small changes in input produce completely different outputs.
3. Computing the Challenge Response: Using the challenge from the verifier and the processed secret, the prover computes a mathematical response. This response is derived from the secret, but an observer cannot reverse engineer the secret from the response.
4. Generating the Final Proof: The final proof is a compact mathematical object (often just a few hundred bytes) that contains everything needed for verification. It includes the cryptographic commitments and challenge responses.
Simple Example: If the secret is “BLOCKCHAIN2024” and the verifier challenges “sum the numeric digits and divide by 2”, the prover would compute: (2+0+2+4)/2 = 4. They would then create a cryptographic proof that proves they can correctly answer this challenge without revealing that their secret is “BLOCKCHAIN2024”.
Computational Intensity
Proof generation is computationally expensive. For complex statements (like proving validity of thousands of transactions), generating a proof can require minutes to hours of computation on a powerful machine. However, this computational work happens off chain and only once. The resulting proof can be verified millions of times very quickly.
This is why zero knowledge rollups are so powerful for scaling. A single powerful prover generates one proof for thousands of transactions, then the blockchain only needs to verify that one proof instead of checking each transaction individually.
Step 4: The Verifier Validates the Proof
The final step is verification. The verifier receives the proof and performs a mathematical check to determine if it is valid. This verification process is designed to be computationally efficient so that it can be performed repeatedly and by many different verifiers.
The Verification Algorithm
The verifier does not need to know the secret. Instead, they use publicly available information to check the proof:
1. Check Proof Format: Verify that the proof is properly formatted and contains all required components. Malformed proofs are immediately rejected.
2. Verify Cryptographic Commitments: Check that the cryptographic commitments in the proof are valid. These commitments bind the prover to their secret without revealing it.
3. Validate Challenge Response: Verify that the prover’s response to the challenge is mathematically correct. This confirms the prover used correct knowledge to generate the response.
4. Accept or Reject: If all checks pass, the proof is accepted and the verifier can be confident that the prover knows the secret. If any check fails, the proof is rejected.
The Critical Property: Soundness
The cryptographic properties of zero knowledge proofs ensure that a dishonest prover cannot create a valid proof for a false statement. The chance of forging a proof is less than one in a trillion, even with enormous computational resources.
This is why zero knowledge proofs are secure for blockchain applications. If someone tries to submit a fraudulent proof (for example, claiming they have funds they don’t actually have), the mathematical properties of the proof system make it virtually impossible to succeed.
Verification in Blockchain: In blockchain systems, every node can independently verify proofs. If a ZK rollup submits a proof to Ethereum claiming “these 5000 transactions are valid”, any Ethereum node can verify this proof in milliseconds. If the proof is invalid, all nodes will reject it. This makes the system trustless and secure.
Verification Speed vs Proof Generation
There is a deliberate asymmetry in zero knowledge proof systems:
Proof Generation: Computationally expensive (minutes to hours)
Proof Verification: Computationally cheap (milliseconds)
This asymmetry is perfect for blockchain. A single powerful prover (like a rollup operator) spends computation resources to generate proofs, but millions of lightweight blockchain nodes can verify them instantly. This is how zero knowledge proofs enable massive scalability.
Core Principles of Zero Knowledge Cryptography
Zero knowledge proofs are built on several fundamental principles that ensure they work correctly and securely:
1. Non-Interactive Proofs
Modern zero knowledge proofs can operate non-interactively, meaning the prover generates a proof without needing back and forth communication with the verifier. This is crucial for blockchain applications where multiple verifiers need to check the same proof.
2. Succinct Proofs
The proof size remains small regardless of the complexity of the statement being proven. For DeFi applications, this means transaction proofs can be verified efficiently on expensive blockchain networks without requiring massive amounts of data storage.
3. Computational Efficiency
Verification of a zero knowledge proof should be computationally efficient, allowing blockchain nodes to validate proofs quickly. Generation of proofs can be more computationally intensive, but verification must be fast.
4. Cryptographic Soundness
The cryptographic basis ensures that it is mathematically impossible for a dishonest party to generate a valid proof for a false statement. This relies on hard mathematical problems that cannot be solved efficiently.
Types of Zero Knowledge Proofs: SNARKs vs STARKs
There are two primary types of zero knowledge proof systems used in blockchain and DeFi applications, each with different tradeoffs and use cases.
| Feature | ZK SNARKs | ZK STARKs |
|---|---|---|
| Proof Size | Very small (288 bytes) | Larger (45 kilobytes) |
| Verification Time | Very fast (milliseconds) | Slower (seconds) |
| Setup Requirement | Requires trusted setup ceremony | No trusted setup needed |
| Quantum Resistance | May be vulnerable to quantum computing | More resistant to quantum attacks |
| Computational Overhead | More complex setup for circuits | More flexible and scalable |
| Primary Use Cases | zkSync, Polygon Zero, Privacy coins | StarkNet, Scalability solutions |
Understanding ZK SNARKs
SNARK stands for Succinct Non Interactive Argument of Knowledge. SNARKs produce very small proofs that are fast to verify, making them ideal for blockchain applications where every byte of data costs money to store.
Real World Application: Zcash, the first major privacy focused cryptocurrency, uses zk SNARKs to enable shielded transactions. Users can send ZEC coins without revealing the sender, receiver, or transaction amount, while the network still validates that all coins are properly accounted for.
Understanding ZK STARKs
STARK stands for Scalable Transparent Argument of Knowledge. STARKs do not require a trusted setup and provide more transparent security assumptions, though proofs are larger and slower to verify.
Real World Application: StarkNet is building an Ethereum layer 2 scaling solution using STARKs. The network proves the correctness of thousands of transactions in a single STARK proof, which is then submitted to Ethereum mainnet for verification.
How Zero Knowledge Proofs Improve Privacy in DeFi Transactions
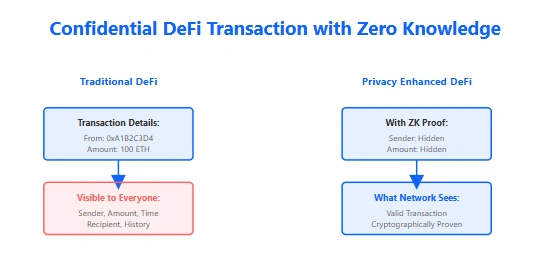
Privacy enhanced DeFi transactions using zero knowledge proofs represent a fundamental shift in how decentralized finance operates. Instead of broadcasting transaction details to the entire network, users can prove transaction validity without revealing sensitive information.
Confidential Transactions in DeFi
A confidential transaction uses zero knowledge proofs to hide the transaction amount while still allowing verification that the transaction is valid. The blockchain can verify that no funds were created or destroyed without seeing the actual amounts.
The Role of Zero Knowledge Proofs in Secure Smart Contracts
Zero knowledge smart contracts extend privacy from transactions to the contract logic itself. These allow decentralized applications to execute complex operations while maintaining privacy for sensitive parameters.
Smart Contract Example: A privacy preserving lending protocol could use zero knowledge proofs to verify that a borrower has sufficient collateral without revealing the exact amount. The smart contract can execute based on this private verification, maintaining both security and confidentiality.
Applications of ZK Smart Contracts
Private Decentralized Exchanges: Swap tokens without revealing the trading pairs or amounts, preventing MEV (Miner Extractable Value) attacks and front running.
Confidential Lending Markets: Borrow and lend assets while keeping collateral amounts and loan terms private from competitors and analysts.
Private Governance: Vote on protocol decisions without revealing voting patterns, protecting minority stakeholder interests from discrimination.
How ZK Technology Improves Blockchain Scalability
One of the most transformative applications of zero knowledge proofs is solving the blockchain scalability trilemma. By using zero knowledge proofs, blockchains can process more transactions while maintaining security and decentralization.
ZK Rollups Explained
ZK rollups are layer 2 scaling solutions that bundle thousands of off chain transactions and create a single zero knowledge proof verifying their correctness. This proof is submitted to the main blockchain, allowing massive throughput increases with minimal on chain data.
How ZK Rollups Work
Zero knowledge rollups represent one of the most promising solutions to blockchain scalability. They allow layer 2 networks to process thousands of transactions per second while maintaining the security guarantees of the base layer blockchain. But how do they actually work? Understanding the architecture and process of ZK rollups reveals why they are transformational for decentralized finance.
Core Concept: ZK rollups bundle hundreds or thousands of transactions together, prove their validity using a single zero knowledge proof, and submit only that proof to the main blockchain. This dramatically reduces on chain data requirements while maintaining cryptographic security.
The Problem ZK Rollups Solve
Ethereum mainnet can process approximately 15 transactions per second. During peak usage, this causes congestion and drives gas fees to hundreds of dollars per transaction. DeFi users face impossible economics: a simple swap that costs a few dollars in execution might cost $50 in fees.
The fundamental bottleneck is that every transaction must be stored on chain and verified by thousands of nodes. This creates security but destroys scalability. We need a solution that maintains security while dramatically increasing throughput.
Zero knowledge rollups achieve this miracle through a clever architecture: they process transactions off chain (where they’re not constrained by network limitations) but prove their correctness on chain (where security is guaranteed). This separation of execution from verification is the key to their power.
Step 1: Transactions Collected Off Chain
The first step in the ZK rollup process begins with users submitting transactions to the layer 2 network instead of directly to Ethereum. These transactions are collected by specialized nodes called sequencers.
The Role of Sequencers
A sequencer is a node that receives transactions, orders them, and executes them against the rollup state. The sequencer serves similar functions to Ethereum validators but operates at layer 2:
Transaction Collection: Users submit transactions (token transfers, smart contract calls, etc.) directly to the sequencer. These transactions bypass Ethereum mainnet and are processed immediately at layer 2 speeds.
State Maintenance: The sequencer maintains the current state of all accounts, balances, and smart contracts on the rollup. When a transaction is received, it updates this state.
Transaction Ordering: The sequencer determines the order in which transactions are processed. This is important because transaction order can affect outcomes (especially relevant for DeFi applications like DEX trades).
Immediate Confirmation: Once the sequencer accepts a transaction, it is immediately confirmed. Users see their transaction finalized at layer 2 speeds (typically under 1 second).
User Experience at This Stage
From the user’s perspective, transacting on a ZK rollup feels much faster than Ethereum:
Ethereum Mainnet: Submit transaction, wait 12+ seconds for inclusion in block, hope for no reorg, watch gas prices fluctuate. Finality in ~15 minutes.
ZK Rollup: Submit transaction, confirmed by sequencer in under 1 second. Finality on mainnet depends on proof submission timing (usually within minutes).
Real DeFi Example: On Uniswap at layer 2 (zkSync Era, Arbitrum, Polygon), you can swap tokens and see the transaction confirmed in less than 1 second for a fraction of a cent. On Ethereum mainnet, the same swap takes a minute and costs $5-50 in gas fees.
Data Availability Considerations
At this stage, transaction data exists only in the sequencer’s memory and network. To ensure users can always recover their funds, ZK rollups post transaction data to Ethereum. This is called data availability and is critical for the security model.
Even if the sequencer disappears, users can use the transaction data stored on Ethereum to reconstruct the rollup state and withdraw their funds. This is why ZK rollups submit data to Ethereum even though the proof ensures transaction validity.
Step 2: Batch and Process Transactions
Once the sequencer has collected a sufficient number of transactions, it packages them into a batch. This batching is crucial for the economics of ZK rollups: the cost of generating a proof is amortized across many transactions.
The Batching Process
The sequencer creates a batch containing anywhere from 100 to 10,000 transactions depending on various factors:
Time Based Batching: If 10 seconds pass without enough transactions, the sequencer creates a batch of whatever transactions have accumulated. This prevents users from waiting indefinitely.
Size Based Batching: If the batch reaches a certain size (e.g., 5000 transactions), the sequencer immediately creates a batch even if the time period hasn’t elapsed.
Gas Based Batching: The sequencer considers the computational cost of proof generation. Larger batches reduce per transaction costs but increase proof generation time.
Transaction Execution Against State
For each transaction in the batch, the sequencer executes it against the current rollup state:
1. Read Current State: Before executing each transaction, the sequencer reads the current account balances and contract states relevant to that transaction.
2. Validate Transaction: Check that the transaction is valid: sender has sufficient balance, nonce is correct, signature is valid, etc.
3. Execute Transaction: Process the transaction: transfer tokens, execute smart contract code, emit events, etc.
4. Update State: Update account balances, contract storage, and other state variables based on the transaction’s execution.
5. Calculate State Root: After processing the transaction, calculate a cryptographic hash (the state root) representing the new state.
State Transitions
Each transaction in a batch creates a state transition. The sequencer maintains a chain of these state transitions:
This chain of state transitions is what will be proven in the next step. The ZK proof must demonstrate that each state transition is correct, which means every transaction in the batch was valid and executed properly.
Computational Efficiency
At this processing stage, the sequencer can execute transactions using standard EVM (Ethereum Virtual Machine) or custom optimized VMs. No proof generation happens yet. The sequencer simply executes the transactions normally, which is fast because there’s no need for cryptographic computation.
Key Insight: The separation of execution and proving is what makes ZK rollups practical. The expensive proving only happens once per batch, not once per transaction. This massive reduction in computational work is why ZK rollups can achieve 1000+ TPS while still being provably secure.
Step 3: Generate the Zero Knowledge Proof
Once a batch is complete and all transactions have been executed, the real cryptographic work begins: generating the zero knowledge proof. This proof must demonstrate that every transaction in the batch was valid and that the state transitions were correct.
What the Proof Proves
The ZK proof proves the following without revealing any transaction details:
State Transition Validity: Each transaction correctly transitioned the state from its input to its output. If state was {A: 100 ETH, B: 50 ETH} and A sent 10 ETH to B, the output state {A: 90 ETH, B: 60 ETH} is correctly derived.
Transaction Validity: Each transaction is properly signed and authorized. The sender’s cryptographic signature proves they approved the transaction.
Sufficient Balances: Before each transaction, the sender had sufficient balance for the amount being transferred. No funds were transferred from empty accounts.
Nonce Correctness: Each transaction used the correct nonce (sequence number) to prevent replay attacks.
Smart Contract Execution: If the batch includes smart contract calls, the proof shows they executed correctly according to the contract code.
The Proof Generation Process
Generating the proof involves several sophisticated steps:
1. Circuit Construction: The proof system converts the transaction batch and state transitions into a mathematical circuit. This circuit represents all the computations that must be proven.
2. Witness Generation: The sequencer generates the “witness” data: the specific values of intermediate computations needed to satisfy the circuit. This includes transaction data, signatures, state values, etc.
3. Polynomial Commitment: The witness data is converted to polynomials and cryptographically committed to. This binding prevents the prover from changing the data after generating the proof.
4. Challenge Generation: The proof system generates cryptographic challenges based on the commitments (using hash functions for non-interactive proofs).
5. Challenge Response: The sequencer computes responses to the challenges using the witness data and polynomial commitments.
6. Proof Assembly: The final proof is assembled from the commitments and challenge responses. For SNARKs, this is typically just a few hundred bytes.
Computational Requirements
Proof generation is extremely computationally intensive. Generating a SNARK proof for a batch of 5000 transactions might require:
CPU Time: 5 to 60 minutes on a powerful server depending on batch size and complexity
GPU Acceleration: Can reduce time to minutes using GPUs (NVIDIA RTX4090, etc.)
Memory: Hundreds of GB of RAM for storing the witness data
Cost: Approximately $0.01 to $0.10 per transaction in hardware costs
This is why the batch size matters. If the cost of generating a proof is $100 and it proves 10,000 transactions, the cost per transaction is only $0.01. But this cost amortized makes ZK rollups economically competitive with layer 1.
Hardware Infrastructure
Modern ZK rollups require significant hardware infrastructure to generate proofs efficiently:
GPU Clusters: Arrays of high end GPUs specifically configured for cryptographic computation and polynomial arithmetic.
Custom ASICs: Some projects are developing Application Specific Integrated Circuits optimized for proof generation, potentially 100x faster than GPUs.
Distributed Proving: Future designs may allow proof generation to be distributed across many independent provers, making the system more decentralized.
Architecture Note: Companies like Nadcab Labs help projects design and deploy the proving infrastructure necessary to run production ZK rollups. This includes selecting appropriate hardware, optimizing proof generation algorithms, and managing the operational complexity of running proof generation at scale.
Step 4: Submit Proof to Mainchain
Once the proof is generated, it’s submitted to the main blockchain (Ethereum) in a transaction. This is where the magic of ZK rollups truly shines: a single small transaction on mainnet contains cryptographic proof of the validity of thousands of layer 2 transactions.
The Proof Submission Transaction
The proof submission is a transaction to a smart contract on Ethereum. This transaction includes:
The Proof: The cryptographic proof itself (256 bytes for SNARK, 1 5 KB for STARK)
State Commitments: Cryptographic hashes (Merkle roots) representing the initial and final states of the batch
Transaction Data: The original transaction data from the batch (compressed to save space)
Metadata: Batch number, timestamp, and other information needed for verification
On Chain Verification
When the proof submission transaction is included in an Ethereum block, all Ethereum nodes perform the following verification:
1. Parse Proof: Extract the proof and public inputs from the transaction.
2. Load Verifier Contract: Execute the ZK proof verifier smart contract, which contains the verification algorithm.
3. Verify Proof: Run the cryptographic verification algorithm. This takes only milliseconds and a small amount of gas.
4. Update State: If the proof is valid, update the rollup’s Ethereum state root and record the batch as finalized.
5. Reject Invalid Proofs: If the proof is invalid, the entire transaction reverts. The batch is rejected and must be resubmitted (or never will be).
The Verification is Quick and Cheap
The brilliance of zero knowledge proofs is that verification is cheap compared to proof generation:
Verification Time: 1 10 milliseconds per proof (independent of batch size)
Gas Cost: 150,000 to 500,000 gas to verify a proof proving 1000+ transactions
This means the cost per transaction is roughly:
For 5000 transactions: 300,000 gas ÷ 5000 = 60 gas per transaction (vs 21,000 gas for a normal Ethereum transaction)
At $1,000 per ETH with gas price of 50 gwei, a layer 2 transaction costs approximately $0.03, compared to $1.05 for a layer 1 transaction.
Finality and Security
When the proof is accepted on mainnet, the batch reaches finality. This means:
No Reversals Possible: The transactions in the batch cannot be reversed or altered. They are backed by Ethereum’s security.
Cryptographic Certainty: The mathematical properties of zero knowledge proofs ensure that no one could have submitted a false proof. An attacker would need to break the underlying cryptography (harder than factoring the product of two 2048 bit primes).
Bridge to Main Chain: Users can now withdraw their funds to Ethereum mainnet with complete confidence that their layer 2 balances are secure and finalized.
Security Model: ZK rollups inherit Ethereum’s security. Even if every ZK rollup operator and prover is malicious, they cannot steal or lose user funds. The cryptographic proof ensures correctness, and data availability on Ethereum allows users to recover funds if necessary.
ZK Rollups vs Other Scaling Solutions
| Feature | ZK Rollups | Optimistic Rollups | Sidechains |
|---|---|---|---|
| Finality | Cryptographic proof finality (minutes) | Challenge period (7 days) | Depends on sidechain (can be hours) |
| Security Model | Math (one honest prover) | Economic (fraud proofs) | Consensus dependent |
| Throughput | 1000+ TPS | 500+ TPS | Varies widely |
| Transaction Cost | $0.01 $0.10 | $0.05 $0.50 | $0.10 $1.00 |
| Withdrawal Time | Immediate to 1 hour | 7 days or use bridge | Minutes to hours |
| Withdrawal Security | Cryptographic guarantee | Economic guarantee | Sidechain dependent |
Real World DeFi Example: Using a ZK Rollup
Scenario: Alice wants to swap 10 USDC for ETH on Uniswap, which operates on both Ethereum mainnet and zkSync (a ZK rollup).
On Ethereum Mainnet: Alice submits her swap transaction. Within 12 seconds it’s included in a block. Gas price is 50 gwei. She pays 150,000 gas for the approval and swap = 7,500 gwei = 0.0075 ETH = $7.50 in fees. Transaction confirmation takes 15 minutes for security.
On zkSync (ZK Rollup): Alice submits her swap transaction to the rollup sequencer. Within 1 second it’s confirmed. The transaction goes into a batch with 4,999 other transactions. The sequencer generates a proof for all 5,000 transactions (taking about 10 minutes with GPU acceleration). The proof is submitted to Ethereum in a single transaction costing only 300,000 gas = 15 gwei per transaction for Alice = 0.00015 ETH = $0.15 total fees. Her transaction is finalized on Ethereum within 15 20 minutes.
The Difference: 50x cheaper fees ($7.50 vs $0.15), confirmed 1000x faster (1 second vs 15 minutes for initial confirmation), same security guarantee.
Real World Use Cases of Zero Knowledge Proofs in DeFi
Private Payments and Confidential Transactions
Privacy focused DeFi protocols enable financial transactions that are indistinguishable from one another on the blockchain. Users can send tokens to each other without revealing transaction history or amounts.
Real Application: Tornado Cash (though now sanctioned) demonstrated how zero knowledge proofs could be used for privacy preserving cryptocurrency mixing. Users could break the on chain link between sender and receiver while maintaining blockchain security.
Identity Verification Using Zero Knowledge Technology
Zero knowledge proofs enable decentralized identity systems where users can prove attributes about themselves without revealing the underlying data. This is transformational for KYC (Know Your Customer) compliance in DeFi.
Use Case: Age Verification A user can prove they are over 18 years old for a service without revealing their actual birthdate, full name, or any government ID information.
Use Case: Credit Score Verification A borrower can prove their credit score meets minimum requirements for a loan without exposing their complete financial history or score to the lender.
Use Case: Sanctions Compliance Users can prove they are not on government sanction lists without revealing their identity to every service provider they interact with.
Benefits of Zero Knowledge Proofs in Decentralized Finance
Enhanced Privacy
Users maintain financial confidentiality while participating in decentralized systems, protecting trading strategies, holdings, and transaction history from competitors and surveillance.
Increased Security
Cryptographic soundness ensures transactions cannot be forged. Even with access to the public ledger, attackers cannot modify past transactions or create false proofs.
Reduced Transaction Costs
ZK rollups and scaling solutions dramatically reduce gas fees by processing hundreds of transactions in a single proof submission to mainnet.
Scalability Without Compromise
Achieve high throughput and low latency while maintaining the security guarantees of the base layer blockchain.
Regulatory Compliance
Prove compliance with regulations using zero knowledge proofs without revealing customers or transaction details to third parties.
Preservation of Decentralization
Enable privacy and scalability without centralized gatekeepers, maintaining the core value proposition of blockchain technology.
Challenges and Limitations of ZK Technology
Despite their tremendous potential, zero knowledge proof systems face several practical and technical challenges that must be addressed for mainstream adoption.
Computational Complexity
Generating zero knowledge proofs is computationally expensive and time consuming. For complex operations, proof generation can take minutes or hours, making it impractical for real time applications.
Circuit Design Complexity
Creating circuits for zero knowledge proofs requires specialized cryptographic knowledge. Developers must be skilled in both blockchain and complex cryptography to implement ZK solutions.
Trusted Setup Requirements
ZK SNARKs require a trusted setup ceremony where participants generate cryptographic parameters. If these parameters are compromised, the entire system could be attacked. This is a significant trust assumption.
Proof Size and Bandwidth
ZK STARKs produce larger proofs than SNARKs, consuming more blockchain data. For certain applications, larger proofs can offset scalability benefits.
Security Considerations When Implementing ZK Solutions
Implementing zero knowledge proof systems securely requires careful attention to cryptographic principles and protocol design.
Mathematical Soundness
The underlying mathematics must be rigorously proven. Systems should be built on well vetted cryptographic foundations that have been reviewed by the academic community and real world testing.
Implementation Audits
Even mathematically sound systems can have vulnerabilities in implementation. Third party security audits by reputable firms are essential before deploying ZK systems handling significant assets.
Quantum Computing Readiness
Some ZK systems may be vulnerable to quantum computing attacks. Organizations should monitor quantum developments and plan migrations to quantum resistant cryptography.
Privacy Preserving but Not Anonymity
Zero knowledge proofs provide privacy from the public ledger but do not inherently provide anonymity. With proper analysis, address linking and user deanonymization may still be possible.
Leading Blockchain Projects Using Zero Knowledge Technology
Zcash
The pioneering privacy coin using zk SNARKs. Zcash enables completely shielded transactions where all transaction details remain hidden while maintaining blockchain verification.
StarkNet
An Ethereum layer 2 network using STARKs for scalability. Processes thousands of transactions and submits validity proofs to mainnet, achieving 1000 TPS throughput.
Aztec Network
A privacy focused layer 2 for Ethereum using zero knowledge proofs. Enables confidential DeFi applications with private token transfers and transactions.
zkSync Era
An Ethereum scaling solution using zk SNARKs. Offers 8000 TPS throughput with cryptographic finality and minimal transaction fees.
Polygon Zero
Formerly Mir, a SNARK based scaling solution enabling high throughput with extreme succinctness. Proofs are verified in milliseconds on Ethereum.
ICP (Internet Computer)
Integrating zero knowledge proofs for privacy preserving smart contracts on its blockchain, enabling private computation at scale.
Future Trends in Privacy Focused DeFi
The future of DeFi will be shaped by advances in zero knowledge proof technology and changing regulatory landscapes. Several key trends are emerging.
Hardware Acceleration
Specialized hardware (GPUs, ASICs) for zero knowledge proof generation and verification will dramatically reduce computational costs, making ZK applications more practical and accessible.
Standardization and Tools
Developer tools and frameworks for building ZK applications will mature, lowering the barrier to entry and enabling more developers to build privacy focused solutions.
Interoperability
Cross chain zero knowledge systems will enable privacy preserving transactions and data verification across different blockchains, creating a unified privacy layer for Web3.
Regulatory Integration
Regulatory frameworks will evolve to embrace zero knowledge proofs as tools for both privacy and compliance. Selective disclosure features will allow users to prove compliance without compromising complete financial privacy.
Building Privacy Focused DeFi Solutions
Organizations looking to implement zero knowledge proof technology face complex cryptographic and engineering challenges. Nadcab Labs specializes in architecting and developing privacy focused blockchain solutions that leverage zero knowledge technologies. From designing confidential transaction systems to implementing ZK rollup solutions, our team brings deep expertise in both cryptography and blockchain development. Whether you need to add privacy features to existing protocols or build entirely new privacy enhanced DeFi platforms, zero knowledge proof implementation requires partners who understand both the mathematical foundations and real world deployment considerations.
The Privacy Revolution in DeFi
Zero knowledge proofs represent one of the most significant cryptographic advances in blockchain technology. They solve the fundamental paradox of decentralized finance: enabling transparency for security while maintaining privacy for participants.
As blockchain adoption accelerates and regulatory requirements grow more sophisticated, zero knowledge proofs will become essential infrastructure. They enable DeFi platforms to offer institutional grade privacy and compliance tools without sacrificing the security or decentralization that attracted businesses to blockchain in the first place.
Whether through scaling layer 2 networks with ZK rollups, enabling private DeFi transactions, or building privacy preserving smart contracts, zero knowledge technology is reshaping how decentralized finance operates. The future of DeFi is private, scalable, and cryptographically secure.
Frequently Asked Questions
Q1.Can zero knowledge proofs be hacked or broken?
Zero knowledge proofs are based on hard mathematical problems. Breaking them would require solving these mathematical problems, which is computationally infeasible with current technology. However, implementation errors in code or protocol design can create vulnerabilities. This is why rigorous security audits are essential before deploying ZK systems with real assets.
Q2.What is the difference between privacy and anonymity in crypto?
Privacy means hiding transaction details (sender, receiver, amount) from the public ledger. Anonymity means making it impossible to link transactions to real world identities. Zero knowledge proofs provide privacy but not necessarily anonymity. Through address analysis and transaction pattern matching, users could still be deanonymized.
Q3.How long does it take to generate a zero knowledge proof?
Proof generation time depends on the proof size, circuit complexity, and hardware available. For simple proofs, this can take seconds. For complex circuits, proof generation can take minutes or hours. Verification, however, is typically much faster, taking only milliseconds to seconds.
Q4.Can zero knowledge proofs be used for regulatory compliance?
Yes, this is a critical emerging use case. Zero knowledge proofs enable users to prove compliance with regulations (like sanctions screening or KYC requirements) without revealing personal information. Selective disclosure features allow users to prove specific attributes while maintaining privacy for other data.
Q5.What does "trusted setup" mean in ZK SNARKs?
A trusted setup is a ceremony where cryptographic parameters are generated that are needed for the ZK SNARK system. If anyone retained the secret values used to generate these parameters, they could forge false proofs. The ceremony must ensure all secrets are destroyed. Major projects like Zcash conduct public trusted setups with many participants to minimize this risk.
Q6.How do ZK rollups compare to optimistic rollups?
ZK rollups prove transaction validity with zero knowledge proofs, providing cryptographic finality. Optimistic rollups assume transactions are valid and only require fraud proofs if someone challenges them. ZK rollups offer stronger security guarantees but require more computational resources. Optimistic rollups are simpler but have longer withdrawal times.
Q7.Can zero knowledge proofs enable front running attacks?
No, zero knowledge proofs actually help prevent front running. By hiding transaction details including amounts and asset pairs, attackers cannot see profitable opportunities in the memory pool. Privacy preserving DeFi protocols using zero knowledge cryptography are significantly more resistant to MEV attacks compared to transparent blockchain systems.
Q8.What hardware is needed to verify zero knowledge proofs?
Proof verification requires minimal hardware. Standard blockchain nodes can verify proofs efficiently. However, proof generation is computationally intensive and benefits from powerful hardware. GPUs and specialized hardware (FPGAs, ASICs) significantly accelerate proof generation, reducing proof generation time from hours to minutes.
Q9.Will quantum computers break zero knowledge proofs?
Some zero knowledge proof systems may be vulnerable to quantum computers, particularly those based on discrete logarithm problems. However, STARKs and hash based systems are believed to be quantum resistant. The cryptography community is actively developing post quantum zero knowledge proof systems to prepare for the quantum era.
Q10.Are zero knowledge proofs legal?
Zero knowledge proofs as a cryptographic technology are legal. Privacy focused applications using them exist in many jurisdictions. However, regulatory treatment of privacy coins and privacy enhanced platforms varies by country. Some jurisdictions embrace them for compliance use cases, while others restrict trading or hold privacy focused protocols to higher scrutiny.
Explore Services
Related Services
Reviewed by

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.
Latest Blogs

DeFi Protocol Upgrade Governance Mechanisms: Technical Guide 2026
Master DeFi protocol upgrade governance mechanisms in 2026. Learn proxy patterns, timelock security, voting models, and real upgrade case studies for
Expert Insights

DeFi Protocol Upgrade Governance Mechanisms: Technical Guide 2026
Master DeFi protocol upgrade governance mechanisms in 2026. Learn proxy patterns, timelock security, voting models, and real upgrade case studies for


