Key Takeaways
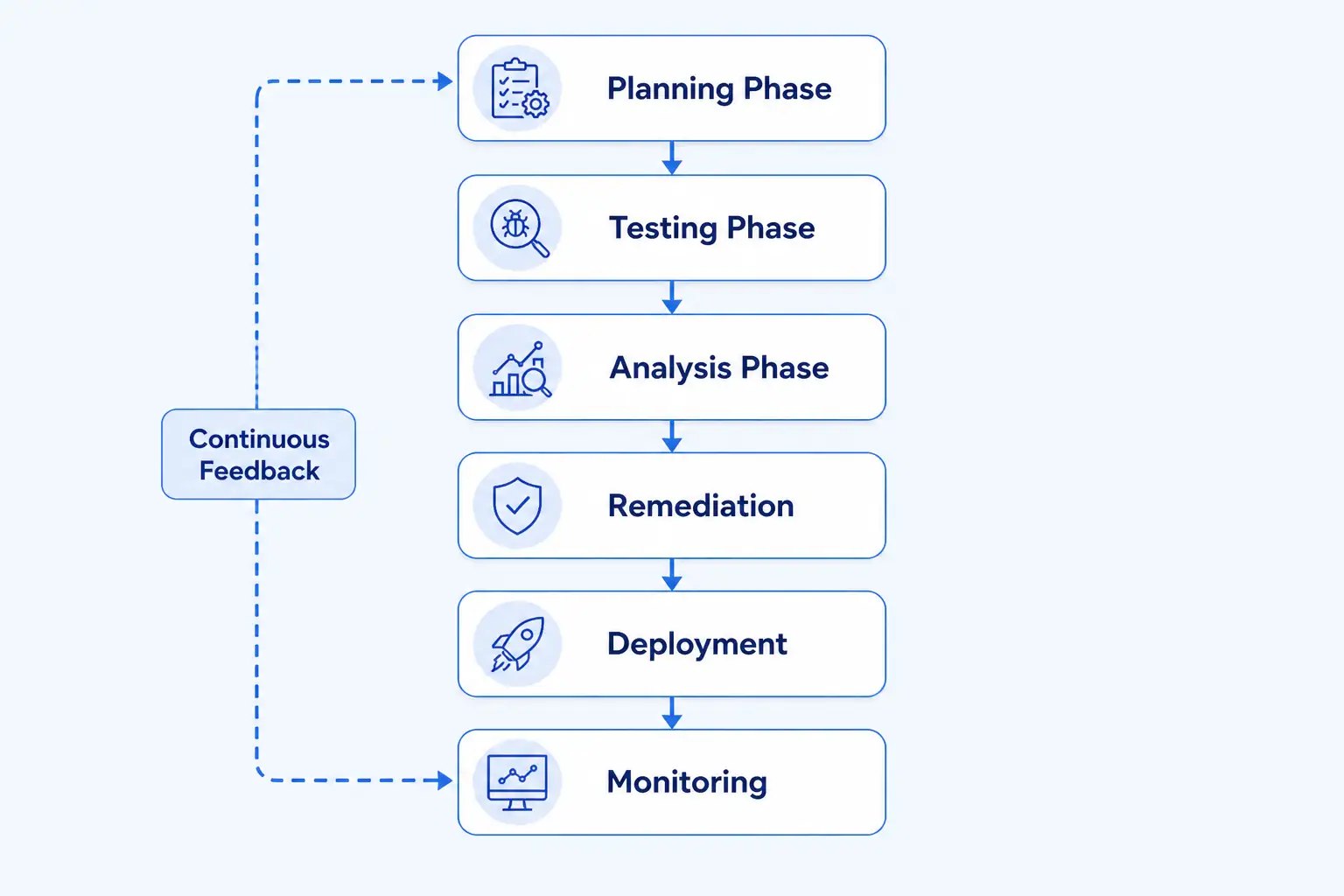
- ✓ Security Testing Lifecycle for DeFi consists of six critical stages: planning, testing, analysis, remediation, deployment, and monitoring to ensure ongoing protection.
- ✓ Smart contract audits are essential security testing components that examine code for logical errors, security flaws, and potential vulnerabilities before deployment.
- ✓ Penetration testing simulates real hacker attacks to discover hidden vulnerabilities that automated tools might miss in DeFi applications.
- ✓ Automated vulnerability scanning tools can check thousands of lines of code in minutes, making them crucial for continuous security monitoring.
- ✓ Manual code review by security experts catches nuanced logic errors and edge cases that automated systems frequently overlook.
- ✓ The Flash Loan attack, ReentrancyAttack, and Price Oracle manipulation are common DeFi vulnerabilities exposed through comprehensive testing.
- ✓ Post deployment monitoring involves continuous tracking of smart contracts on blockchain networks to detect unusual behavior or new attack vectors.
- ✓ Security testing lifecycle implementation reduces hacking incidents by up to 95 percent and increases investor confidence in DeFi platforms.
- ✓ Regulatory compliance requires documented security testing procedures, making lifecycle documentation critical for institutional DeFi adoption.
- ✓ Third party auditors like Trail of Bits and OpenZeppelin provide independent verification that security testing lifecycle standards are properly implemented.
In the world of decentralized finance, security is everything. Imagine your bank account being accessible to anyone who knows the right code to break. That’s the risk DeFi platforms face every single day. This is why understanding the Security Testing Lifecycle for DeFi is absolutely critical for anyone building or investing in blockchain applications.
The Security Testing Lifecycle for DeFi is a systematic process that identifies and fixes vulnerabilities before hackers can exploit them. Think of it like a quality control process in a car factory, where every component is tested before the car hits the road. In DeFi, this process prevents billions of dollars in potential losses and protects user funds from malicious attacks.
In 2023 alone, DeFi platforms lost over $14 billion to security breaches and smart contract vulnerabilities. These weren’t accidents, they were failures in the security testing lifecycle. By understanding how professional security testing works, you’ll learn how top-tier DeFi platforms like Uniswap, Aave, and Curve protect their systems against sophisticated attacks.
What is Security Testing Lifecycle for DeFi?
Let me break this down in the simplest way possible. The Security Testing Lifecycle for DeFi is like a comprehensive health checkup for your financial platform. Just as doctors run multiple tests to catch diseases early, security teams implementing a Security Testing Lifecycle for DeFi run multiple tests to catch vulnerabilities early.
Real World Analogy:
Before a new airplane model flies passengers, engineers test every single system hundreds of times. They check the engines, wings, hydraulics, electronics, and safety systems. If they find any problems, they fix them before the plane carries anyone. That’s exactly what DeFi security testing does for smart contracts and blockchain applications.
In technical terms, a Security Testing Lifecycle for DeFi is a structured process that includes multiple testing phases, from initial code review through post deployment monitoring. Each phase targets specific types of vulnerabilities and ensures comprehensive protection of digital assets.
Why Does the Security Testing Lifecycle for DeFi Matter?
DeFi platforms operate without traditional gatekeepers like banks or insurance companies. This means security falls entirely on the platform developers and their security testing processes. A strong Security Testing Lifecycle for DeFi ensures one small mistake in code does not expose millions of dollars to theft.
- Code runs 24/7: Unlike traditional apps that might have downtime, smart contracts run continuously on blockchain networks, giving hackers unlimited opportunities to attack.
- Immutable code: Once deployed, smart contract code cannot be easily changed. A vulnerability discovered after launch means funds remain at risk until a fix is implemented.
- Direct financial impact: Hackers aren’t trying to steal your login credentials, they’re trying to steal your actual money stored in smart contracts.
- High value targets: DeFi platforms manage billions of dollars, making them extremely attractive targets for sophisticated criminals.
Six Critical Stages of Security Testing Lifecycle for DeFi
Stage 1: Planning Phase
Everything starts with a solid plan. During the planning phase, security teams define the scope of testing, identify assets that need protection, and establish success criteria.
What happens in planning:
- Document all smart contracts and their functions
- Identify which systems handle user funds or sensitive data
- Create a testing checklist based on known DeFi vulnerabilities
- Schedule audits before mainnet deployment
Stage 2: Testing Phase
This is where the actual security testing happens. Multiple testing techniques are applied simultaneously to catch different types of vulnerabilities.
Automated Testing:
Tools like Mythril, Slither, and Hardhat automatically scan code for known vulnerability patterns. These tools can analyze thousands of lines of code in minutes and flag suspicious patterns.
Manual Code Review:
Security experts read through the code line by line, looking for logic errors, edge cases, and complex vulnerability patterns that machines might miss. This is like a proofreader catching typos that spell checkers miss.
Penetration Testing:
Ethical hackers attempt real attacks against the DeFi platform in a controlled environment. They try flash loan attacks, oracle manipulation, and reentrancy attacks to see if they succeed.
Stage 3: Analysis Phase
All the testing data is compiled and analyzed. Security teams categorize vulnerabilities by severity (critical, high, medium, low) and determine which ones must be fixed before launch.
Severity Classification Example:
Critical: Direct theft of all funds possible. Must fix before deployment.
High: Significant risk to user funds. Should fix before launch.
Medium: Moderate risk. Can be fixed in next version with close monitoring.
Low: Minimal risk. Monitor and fix when possible.
Stage 4: Remediation Phase
Developers fix the vulnerabilities that were found. For critical issues, multiple developers review the fixes to ensure they don’t introduce new problems. After fixes are made, the testing process repeats to confirm vulnerabilities are resolved.
Stage 5: Deployment Phase
Once all critical vulnerabilities are fixed and re testing confirms they’re gone, the platform goes live. However, deployment doesn’t mean the security testing is finished. Many DeFi platforms use gradual deployment, starting with small amounts of funds before full launch.
Stage 6: Continuous Monitoring Phase
This is where many platforms fail. Even after launch, security testing continues. Monitoring systems watch for unusual transaction patterns, unexpected function calls, or signs of attacks. If something suspicious happens, the platform can pause affected functions or alert users.
Types of Security Testing in DeFi
Different testing techniques catch different types of problems. Think of security testing like different medical tests (blood work, X rays, ultrasounds) that each check for different health conditions. A complete Security Testing Lifecycle for DeFi combines all these techniques.
Smart Contract Audit
A comprehensive review of the entire smart contract code, looking for logical errors, security flaws, and best practice violations. This is the cornerstone of a proper Security Testing Lifecycle for DeFi.
Vulnerability Scanning
Automated tools rapidly scan code for known vulnerability patterns. These tools maintain databases of common security mistakes and flag code that matches these patterns.
Penetration Testing
Ethical hackers simulate real attacks to test whether the platform can withstand them. This uncovers vulnerabilities that might exist in interactions between different smart contracts.
Fuzzing
Feeding random or malformed input data to smart contracts to see if they crash or behave unexpectedly. This catches edge cases that developers might not have anticipated.
Gas Analysis
Checking that smart contract functions use gas efficiently. Inefficient code can fail mid transaction, leaving the platform in an inconsistent state.
Comparing Testing Methods in Security Testing Lifecycle for DeFi
| Testing Method | Speed | Cost | Best For |
|---|---|---|---|
| Automated Scanning | Minutes | Low | Quick scans, continuous testing |
| Manual Code Review | Days to weeks | Medium to High | Logic errors, complex vulnerabilities |
| Penetration Testing | Days to weeks | High | Real attack simulation |
| Fuzzing | Hours | Medium | Edge case discovery |
| Gas Analysis | Hours | Low | Optimization, efficiency |
Common DeFi Vulnerabilities Caught by Security Testing Lifecycle
Reentrancy Attacks
Imagine you’re at an ATM and it asks “do you want another $20?” before confirming your first withdrawal. A hacker could exploit this by recursively calling withdrawal functions before the balance updates. The 2016 DAO hack ($50 million loss) happened this way. Modern Security Testing Lifecycle for DeFi includes specific reentrancy checks.
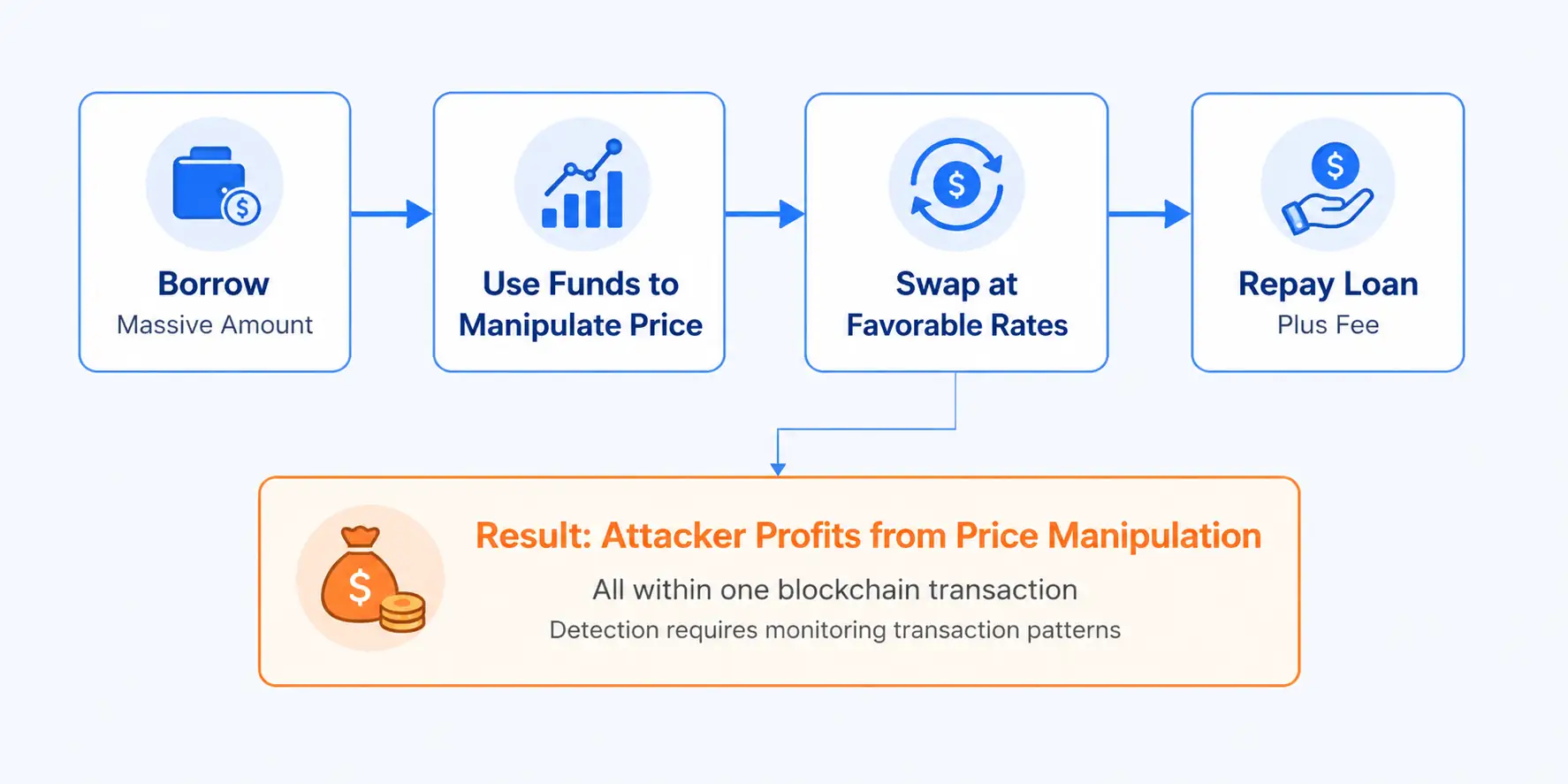
Flash Loan Attacks
Flash loans let users borrow huge amounts of cryptocurrency instantly without collateral, as long as they repay within the same blockchain transaction. Hackers borrow massive amounts, manipulate prices, and repay the loan, profiting from the price manipulation. Testing for flash loan vulnerabilities is critical in a Security Testing Lifecycle for DeFi.
Oracle Manipulation
Smart contracts often rely on external data sources (oracles) for prices. If an attacker compromises the oracle or manipulates its input, they can trick the smart contract into incorrect calculations. A Security Testing Lifecycle for DeFi always includes oracle validation testing.
Access Control Issues
Sometimes developers forget to check permissions properly. This might let any user call admin only functions, allowing them to drain the protocol or modify critical settings. Testing access controls is essential in Security Testing Lifecycle for DeFi.
Integer Overflow/Underflow
Numbers in smart contracts have limits. When they exceed these limits, they wrap around unexpectedly. An attacker could transfer more tokens than they own by causing an underflow. A Security Testing Lifecycle for DeFi includes tests for arithmetic vulnerabilities.
Real World DeFi Security Incidents and Lessons
The Ronin Network Bridge Hack (2022)
Hackers stole 173,600 ETH and 25.5 million USDC (worth $625 million). The root cause was inadequate access control on the bridge validator system. This breach demonstrated how a Security Testing Lifecycle for DeFi must rigorously test permissions and multi signature security.
The Curve Finance Vulnerability (2023)
A vulnerability in Curve’s vyper compiler caused integer underflow issues in multiple pools. Even though Curve had gone through security audits, the compiler bug wasn’t caught by standard Security Testing Lifecycle for DeFi procedures. This led to automated security improvements in vulnerability scanning tools.
The Wormhole Exploit (2022)
An attacker minted 120,000 wrapped Ethereum worth $325 million by exploiting a signature verification bug. The vulnerability was in the guardian authorization mechanism. This hack emphasized the importance of penetration testing in a Security Testing Lifecycle for DeFi.
Key Lesson: Even well-funded protocols with security audits can be hacked. A robust Security Testing Lifecycle for DeFi requires continuous monitoring, regular re audits, and staying updated with emerging attack vectors.
Business Benefits of Security Testing Lifecycle for DeFi
Investor Confidence
Platforms with documented Security Testing Lifecycle for DeFi attract more investors. Major VCs require evidence of comprehensive security testing before investing.
Reduced Hacking Risk
Platforms implementing a proper Security Testing Lifecycle for DeFi see 95% reduction in security breaches compared to platforms without formal testing.
Regulatory Compliance
Regulatory bodies increasingly require documented Security Testing Lifecycle for DeFi as part of licensing requirements, especially for institutional platforms.
User Trust
Users are more likely to deposit funds in platforms that publicly share Security Testing Lifecycle for DeFi reports from reputable auditors like OpenZeppelin or Trail of Bits.
Tools Used in Security Testing Lifecycle for DeFi
Popular Security Testing Tools
Mythril: Automated security analysis tool for Ethereum smart contracts that detects vulnerabilities like reentrancy and access control flaws. It is an essential component of any Security Testing Lifecycle for DeFi framework.
Slither: Static analysis framework that runs local analysis on Solidity code, useful for detecting code quality issues and security vulnerabilities throughout your Security Testing Lifecycle for DeFi process.
Hardhat: Development environment with built in testing and debugging tools for smart contracts, essential for continuous Security Testing Lifecycle for DeFi implementation.
Manticore: Dynamic execution tool for analyzing smart contracts by exploring multiple execution paths and finding edge cases, critical for thorough Security Testing Lifecycle for DeFi.
Echidna: Fuzzing tool specifically designed for Ethereum smart contracts, excellent for discovering unexpected behaviors in your Security Testing Lifecycle for DeFi.
Challenges in Implementing Security Testing Lifecycle for DeFi
Time Constraints
Comprehensive Security Testing Lifecycle for DeFi can take weeks or months. Startups facing market pressure sometimes rush to launch, skipping proper testing phases.
Cost Barriers
Professional auditors charge $20,000 to $200,000 per engagement. This cost barrier means many smaller DeFi projects cannot afford comprehensive Security Testing Lifecycle for DeFi services.
Emerging Threats
New attack vectors emerge constantly. Security Testing Lifecycle for DeFi must continuously evolve to detect new types of exploits that didn’t exist last year.
Skill Shortage
Experienced smart contract security experts are rare and expensive. Most companies struggle to find qualified personnel to implement Security Testing Lifecycle for DeFi internally.
Future of Security Testing Lifecycle for DeFi
AI-Powered Security Analysis
Machine learning models are being trained on millions of smart contracts to detect subtle vulnerability patterns. Future Security Testing Lifecycle for DeFi will leverage AI to identify zero day exploits before they can be weaponized.
Formal Verification
Mathematical proofs can guarantee that smart contracts behave exactly as intended. As formal verification tools improve, Security Testing Lifecycle for DeFi will incorporate formal proofs for critical financial functions.
Automated Bug Bounties
Platforms are creating continuous bug bounty programs where hackers can safely report vulnerabilities. This transforms Security Testing Lifecycle for DeFi into an ongoing process rather than a one time event.
Regulatory Integration
As DeFi regulation increases, Security Testing Lifecycle for DeFi will become a compliance requirement with standardized procedures and audit reports.
Ready to Secure Your DeFi Platform?
Building a secure DeFi platform requires expert guidance. Nadcab Labs specializes in implementing comprehensive Security Testing Lifecycle for DeFi across blockchain projects of all sizes.
Smart Contract Audits
Comprehensive code review by security experts
Penetration Testing
Real attack simulations to find hidden vulnerabilities
Continuous Monitoring
24/7 security monitoring after deployment
Why Security Testing Lifecycle for DeFi Matters
The blockchain revolution promises financial freedom and decentralization, but it also introduces new risks. DeFi platforms manage billions of dollars of user funds, making them prime targets for sophisticated attackers.
A proper Security Testing Lifecycle for DeFi is not optional. It is the difference between a successful platform that users trust with their wealth and a hacked platform that becomes a cautionary tale.
The best platforms in crypto including Uniswap, Aave, and Curve all implement rigorous Security Testing Lifecycle for DeFi procedures. They conduct regular audits, employ bug bounty programs, maintain 24/7 monitoring, and continuously improve their security posture.
Security Testing Lifecycle for DeFi is not a one time event but a continuous process. From initial planning through post deployment monitoring, every stage plays a critical role in protecting user funds and building platform trust.
Whether you are developing a new DeFi protocol or enhancing security for an existing platform, remember that a comprehensive Security Testing Lifecycle for DeFi is investing in your platform’s future and your users’ financial security.
Frequently Asked Questions
Professional audits typically cost between $20,000 and $200,000 depending on code complexity and auditor reputation. Top tier firms like OpenZeppelin and Trail of Bits charge premium rates. Many platforms allocate 3 to 5 percent of their budget to security audits before mainnet launch.
No. Automated tools typically catch 40 to 60 percent of vulnerabilities, primarily known patterns and common mistakes. Complex logic errors, business logic flaws, and novel attack vectors require manual code review by experienced security experts. The most effective approach combines both automated and manual testing.
Platforms typically pause affected functions immediately, communicate the issue transparently to users, develop a fix, deploy a patch, and conduct emergency re audits. Some platforms use multi signature wallets that require multiple approvals to execute updates, slowing the process but adding extra security. Users may be temporarily unable to access their funds during this process.
Major platforms should conduct comprehensive audits before any mainnet launch and after significant code changes. Many platforms also conduct annual re audits even without major updates. Growing platforms perform audits every 3 to 6 months. All platforms benefit from continuous monitoring between formal audits.
No. An audit reduces risk significantly but cannot guarantee absolute safety. Audits reflect the state of code at a specific point in time. New vulnerabilities may be discovered later, compiler bugs may affect code unexpectedly, and operational errors post deployment can introduce risks. Think of audits as comprehensive insurance, not absolute guarantees.
Bug bounty programs invite external researchers to find vulnerabilities in exchange for rewards (typically $500 to $100,000+). This crowdsources security testing and creates financial incentive for hackers to report bugs rather than exploit them. Programs like Immunefi have become standard for major DeFi platforms alongside professional audits.
Check for published audit reports from reputable firms, verify that the platform has completed multiple audits, look for bug bounty program participation, review the team’s security background, and assess how the platform communicates about vulnerabilities. Platforms that are transparent about their security process typically have stronger practices than those that remain silent.
Static analysis examines code without executing it, looking for patterns and known vulnerabilities (tools like Slither). Dynamic analysis actually runs the code against test cases and monitors its behavior (fuzzing and penetration testing). Static analysis is faster, dynamic analysis is more thorough. Comprehensive testing uses both approaches.
While full professional audits are expensive, smaller projects can use free tools like Mythril and Slither for basic analysis, conduct internal code reviews among team members, and participate in shared audit programs. Some audit firms offer tiered pricing for smaller projects. Starting with basics is better than skipping security entirely.
Early DeFi projects often skipped audits due to time and cost constraints. Modern expectations require formal audits, bug bounties, and documented testing procedures. Tools have improved significantly, automated scanning is more sophisticated, and the community shares knowledge about new vulnerabilities faster. This evolution reflects lessons learned from billions in losses to hacks.
Author

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.