Key Takeaways
- The State Trie is a tree-shaped data structure that organizes and protects all account-related data on a blockchain network.
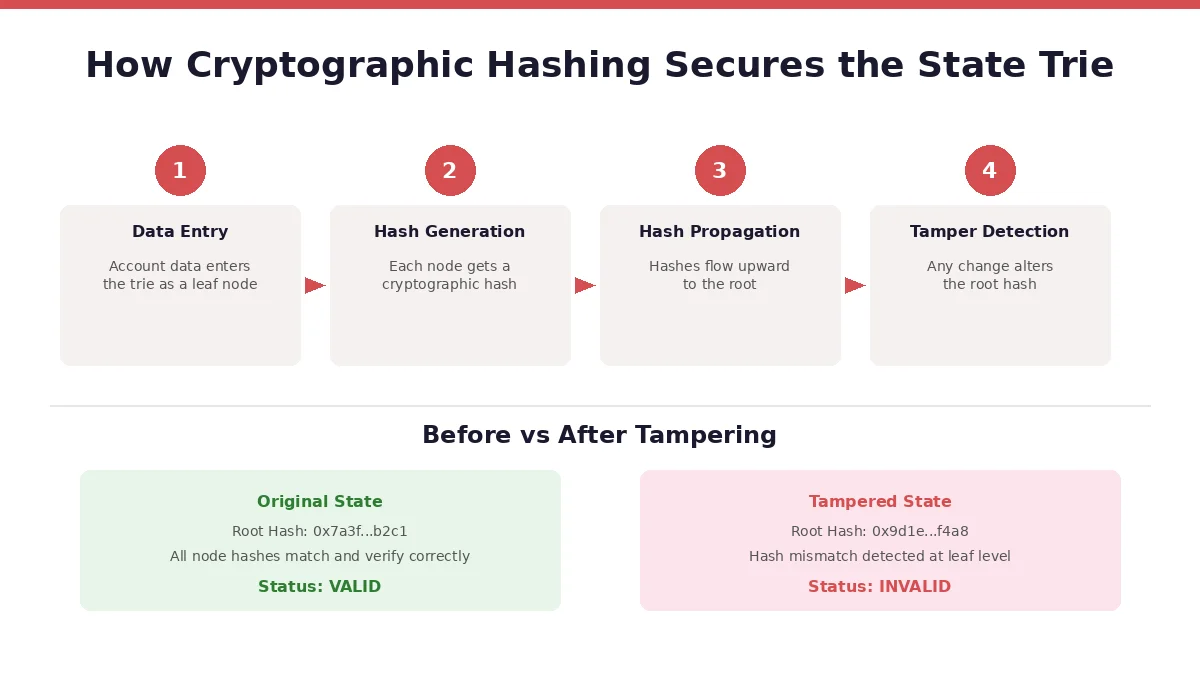
- Cryptographic hashing at every node creates unique fingerprints, making any unauthorized data change instantly visible.
- The root hash of the State Trie is stored in each block header, connecting every piece of state data to the blockchain itself.
- Merkle proofs allow lightweight verification of specific data without downloading the entire blockchain.
- Unlike traditional databases, the State Trie operates across decentralized nodes, removing single points of failure and the need for trust in a central authority.
- Mining and consensus mechanisms work alongside the State Trie to validate state changes before they become permanent.
- The combination of hashing, decentralization, and Merkle-based verification makes the State Trie a core pillar of blockchain data security.
Blockchain networks handle thousands of transactions, smart contracts, and account records every day. But here is the question that most people skip over: how does the network actually keep all that data safe and accurate? The answer sits inside a structure called the State Trie.
If you have ever wondered why nobody can just go in and edit an account balance on Ethereum or fake a smart contract result, the State Trie is a big part of the reason. It is a data structure that sits at the heart of how blockchains organize, store, and verify state information. And while the concept borrows from computer science ideas that have been around for decades, its application in blockchain is what makes it so powerful.
This article breaks down how the State Trie works, why it matters for security, and what makes it different from the way traditional systems handle data. We will walk through the structure itself, the role of cryptographic hashing, and the lifecycle of how data gets protected from the moment a transaction is submitted until it becomes a permanent part of the chain.
What is a State Trie in Blockchain?
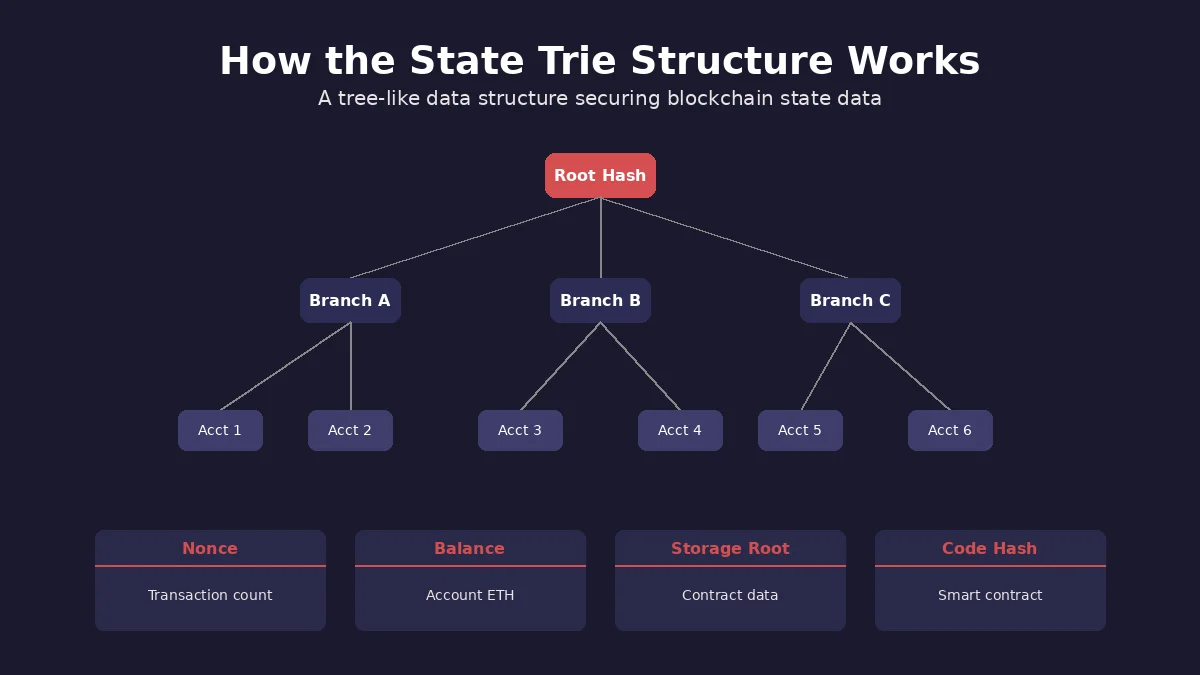
A State Trie, sometimes called a State Merkle Trie, is a specialized data structure that blockchains use to store the current state of every account on the network. Think of it as a snapshot that records what each account looks like at any given moment. This includes things like account balances, the number of transactions sent (called a nonce), and for smart contract accounts, the contract code and storage data.
The word “Trie” comes from the word “retrieval.” It is a type of tree structure where data is stored along branches, and each branch represents a specific path to a piece of information. In the context of blockchain, each path leads to an account, and the data at the end of that path contains the account details.
What sets the State Trie apart from a regular trie is the use of cryptographic hashing. Every node in the tree has a hash value that depends on the data it holds and the hashes of its child nodes. This creates a chain reaction: if even a single byte of data changes somewhere deep in the tree, the hash at the top of the tree (called the root hash) will also change. That root hash is then stored in the block header, tying the entire state of the network to each block on the chain.
This is fundamental to how platforms like Ethereum operate. Every time a new block is created, the State Trie gets updated to reflect the latest state of all accounts. The root hash of this updated trie is included in the new block, making it possible for anyone to verify the accuracy of the state data without needing to trust a single authority.
Understanding the Trie Data Structure and Its Variants
Before getting into the security side of things, it helps to understand the basic structure. A trie is a tree where each node represents a character or a part of a key. When you follow a path from the root down to a leaf, you reconstruct the full key. In blockchain, these keys are typically account addresses (hashed versions of them, to be specific).
There are different types of tries used in blockchain systems. Ethereum, for example, uses a Modified Merkle Patricia Trie. This variant combines three ideas:
Patricia Trie: Compresses paths where nodes have only one child, reducing the overall size of the tree and speeding up lookups.
Merkle Trie: Adds cryptographic hashes to each node, so the data can be verified without needing to check every single entry.
Hexary Trie: Uses 16 branches per node (one for each hexadecimal digit), which matches the structure of Ethereum addresses and makes navigation efficient.
This combination gives the blockchain a structure that is compact, fast, and cryptographically secure. It is not just about storing data. It is about storing data in a way that makes cheating practically impossible. If you want a deeper understanding of how real-world data feeds interact with blockchain architecture, take a look at how real-world data oracles for blockchain work alongside these structures.
How the Merkle Trie Adds a Security Layer
The Merkle component is where the security really kicks in. Named after Ralph Merkle, who patented the concept in 1979, a Merkle tree is a data structure where every leaf node contains a hash of a data block, and every non-leaf node contains a hash of its children. The result is a single root hash that represents the entire dataset.
In the context of the State Trie, this means that the root hash is a compressed summary of every single account on the blockchain. If someone tries to change the balance of one account, that change will produce a different hash for that leaf node. That different hash will then propagate upward through the tree, ultimately changing the root hash. Since the root hash is recorded in the block header and shared across all nodes, any tampering will be immediately obvious.
This property is what makes the State Trie so valuable for security. You do not need to check every piece of data to confirm that nothing has been altered. You just need to compare root hashes. If they match across nodes, the state is consistent. If they do not match, something has gone wrong, and the network knows exactly where to look.
How Does the State Trie Secure Blockchain Data? A Detailed Breakdown
Now that we have covered the basics, let us get into the specifics of how the State Trie actually protects the data sitting on a blockchain. The security is not a single mechanism. It is a layered system where multiple features work together.
1. Cryptographic Hashing at Every Node
Every node in the State Trie is hashed using a cryptographic hash function. Ethereum uses Keccak-256, which produces a fixed-length 256-bit hash output regardless of the input size. The important thing about cryptographic hashing is that it is a one-way function. You can turn data into a hash quickly, but you cannot reverse-engineer the data from the hash. Even a tiny change in the input, like changing a single digit in an account balance, produces a completely different hash output.
This means that every node in the trie carries a unique fingerprint of the data it represents. Since parent nodes hash the hashes of their children, this fingerprint extends all the way up the tree to the root. The root hash, therefore, is a fingerprint of the entire state of the blockchain at that point in time.
2. Root Hash Anchoring in Block Headers
The root hash of the State Trie is stored in the header of each block. This is a critical design choice. It means that the state of every account on the network is mathematically tied to the blockchain itself. When a miner or validator produces a new block, the root hash they include must match the result of applying all the transactions in that block to the previous state. If it does not match, the block gets rejected by other nodes.
This anchoring is what makes it impossible to silently alter state data. Even if someone managed to change a value in their local copy of the State Trie, the root hash they would calculate would differ from the one agreed upon by the rest of the network. The block would fail validation, and the tampered data would never become part of the official chain. The difficulty of this process is closely related to how mining difficulty in blockchain contributes to the overall security of the system.
3. Merkle Proofs for Efficient Verification
One of the most practical security features of the State Trie is the ability to generate Merkle proofs. A Merkle proof is a small set of hashes that allows someone to verify that a specific piece of data exists in the trie without downloading the entire thing. This is especially useful for light clients, which are devices that do not store the full blockchain but still need to verify transactions.
Here is how it works: to prove that a specific account has a certain balance, you only need to provide the hash values along the path from that account’s leaf node to the root. The verifier can then recalculate the root hash using those hashes and compare it to the known root hash in the block header. If the hashes match, the data is confirmed. If they do not, the proof fails.
This makes the system both secure and efficient. You get cryptographic guarantees without the overhead of checking every single account.
4. Immutability Through Append-Only Updates
The State Trie does not allow data to be overwritten in the traditional sense. When a transaction changes an account’s balance, the trie does not simply edit the old value. Instead, a new version of the relevant nodes is created, and the old version remains accessible in the historical record. This append-only approach means that you can always go back and verify what the state of any account was at any previous block.
This historical traceability adds another layer of security. Even if a current state is somehow questioned, anyone can walk back through the chain of state trie roots to reconstruct the full history of changes. It is one of the reasons why blockchain is considered an immutable ledger.
What Data Does the State Trie Store for Each Account?
Each account entry in the State Trie contains a specific set of fields. Here is a breakdown of what gets stored and what each field means for security:
| Field | Description | Security Role |
|---|---|---|
| Nonce | Number of transactions sent from the account | Prevents replay attacks by ensuring each transaction is unique |
| Balance | Amount of cryptocurrency held (in Wei for Ethereum) | Verified by the trie hash; any unauthorized change alters the root hash |
| Storage Root | Root hash of the account’s storage trie (for smart contracts) | Secures all contract storage data under a single verifiable hash |
| Code Hash | Hash of the smart contract bytecode (empty for regular accounts) | Guarantees contract code cannot be altered after deployment |
Each of these fields is serialized and hashed together. The resulting hash becomes the leaf node for that account in the State Trie. This tight packaging of data is what allows the trie to provide a complete, verifiable picture of the network state with a single root hash.
Lifecycle of Data Security in the State Trie
The State Trie does not protect data through a single action. It is an ongoing process that repeats with every new block. Understanding this lifecycle makes it easier to see why the system is so resilient. Below is a step-by-step walk through how data goes from a raw transaction to a securely stored state entry.
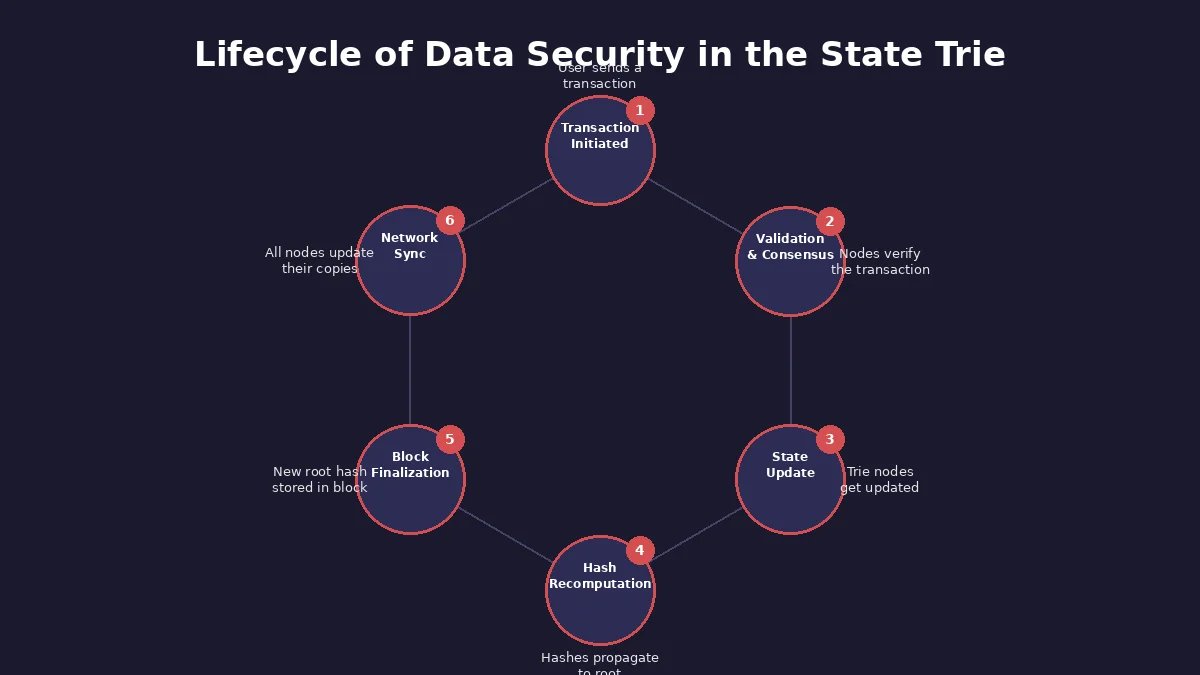
Stage 1 – Transaction Submission: A user signs and submits a transaction using their private key. The digital signature proves ownership and authorization. The transaction enters the mempool, waiting to be picked up by a miner or validator.
Stage 2 – Validation and Consensus: A miner or validator selects the transaction, verifies the signature and checks that the account has enough funds. The transaction is grouped with others into a candidate block. Consensus rules determine which block gets added next.
Stage 3 – State Trie Update: Once validated, the transaction changes account data. For example, if Account A sends 5 ETH to Account B, the balance field for both accounts gets updated in the trie. New nodes are created along the affected paths.
Stage 4 – Hash Recomputation: The hashes of the updated leaf nodes are recalculated. These new hashes propagate upward through the trie, updating every parent node along the way until a new root hash is generated.
Stage 5 – Block Finalization: The new root hash is placed in the block header. The block, including all its transactions and the state root, is added to the blockchain. At this point, the data is effectively sealed.
Stage 6 – Network Synchronization: The new block is broadcast to all nodes. Each node independently applies the transactions, updates their own copy of the State Trie, and verifies that their computed root hash matches the one in the block header. If it matches, the state update is accepted.
This cycle repeats for every block. Each cycle adds another layer of cryptographic verification on top of the previous one, making older data progressively harder to tamper with. The role of RPC nodes in blockchain is also worth understanding here, as they serve as communication endpoints that allow applications to read from the State Trie and submit transactions to it.
State Trie vs Traditional Database Security: A Comparison
To fully appreciate what the State Trie brings to the table, it is useful to compare it against how conventional databases handle data security. The differences are significant and explain why blockchain is considered more resistant to tampering.
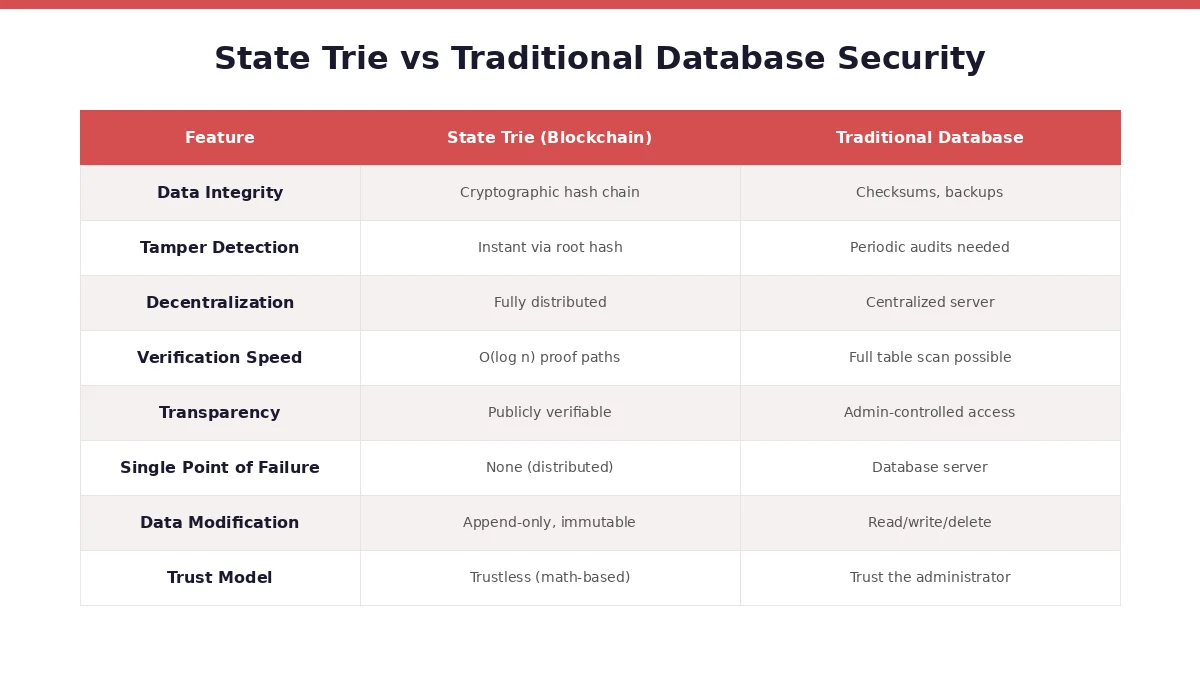
| Parameter | State Trie (Blockchain) | Traditional Database |
|---|---|---|
| Data Integrity Mechanism | Cryptographic hash chain from leaves to root | Checksums and periodic backups |
| Tamper Detection | Instant via root hash mismatch | Requires scheduled audits or anomaly detection |
| Storage Model | Distributed across thousands of independent nodes | Centralized server or server cluster |
| Verification Speed | O(log n) using Merkle proofs | Varies; can require full table scans |
| Transparency | Publicly verifiable by anyone | Access controlled by administrators |
| Single Point of Failure | None; failure of individual nodes does not affect the network | Server failure can result in data loss or downtime |
| Modification Policy | Append-only; old states are preserved | Read, write, update, and delete operations allowed |
| Trust Model | Trustless; security is based on mathematics | Requires trust in the database administrator |
The comparison makes one thing clear: the State Trie is designed for environments where trust cannot be assumed. Traditional databases work well when a single organization controls the data, but blockchain operates in a trustless setting where any participant might be adversarial. The State Trie, combined with decentralized consensus, closes that trust gap.
The Role of Mining and Consensus in State Trie Security
The State Trie does not work in isolation. Its security is backed by the consensus mechanism that the blockchain uses to agree on the correct state. In proof-of-work systems like Bitcoin (and Ethereum before its transition to proof of stake), miners compete to solve a computational puzzle. The winner gets to propose the next block, which includes the updated state trie root.
What makes this relevant to the State Trie is that miners do not just validate transactions. They also execute those transactions against the current state, produce a new State Trie root, and include it in the block. Other nodes then independently repeat this process. If a miner tries to include a fraudulent state root, every other node will calculate a different root hash when they run the same transactions. The fraudulent block will be rejected.
In proof-of-stake systems, validators serve the same purpose. They stake their own cryptocurrency as collateral, and if they propose a block with an incorrect state root, they risk losing that stake. This economic incentive aligns the interests of validators with the integrity of the State Trie.
The computational or economic cost of attacking the consensus layer is what prevents someone from simply forcing an invalid State Trie onto the network. Even if the trie structure itself could theoretically be manipulated on a single machine, the consensus mechanism ensures that no single actor can push that manipulation onto the global state. For a deeper look at how this plays out when consensus breaks down, check out our coverage of how chain splits impact blockchain networks.
Build Secure Blockchain Solutions with the Right Architecture
From State Trie optimization to full-stack blockchain development, our team helps you build systems that are tamper-proof, scalable, and production-ready.
Real-World Examples of State Trie Security in Action
Understanding theory is one thing. Seeing it applied is another. Here are a few real situations where the State Trie’s design has played a direct role in securing blockchain data.
Ethereum’s DAO Hack (2016): When a vulnerability in The DAO smart contract was exploited, the attacker drained funds from the contract. The interesting thing is that the State Trie recorded every step of this exploit. The integrity of the data was never in question because the trie hashes accurately reflected what had happened. The community could verify exactly what went wrong, which led to the controversial decision to fork the chain and reverse the damage. The State Trie did not prevent the smart contract bug, but it ensured that the record of events was perfectly accurate and verifiable.
Light Client Verification: Mobile wallets and browser-based wallets often run as light clients. They do not download the full blockchain. Instead, they request Merkle proofs from full nodes to verify account balances and transaction status. This entire verification model depends on the State Trie’s structure. Without it, light clients would have no way to trust the data they receive.
State Synchronization on New Nodes: When a new node joins the Ethereum network, it needs to catch up with the current state. Instead of replaying every transaction from the genesis block, it can use “snap sync” or “fast sync,” which relies on downloading the State Trie and verifying it against known root hashes. This is only possible because the trie structure guarantees that the downloaded state is valid.
How Decentralization Strengthens the State Trie
The State Trie on its own is a well-designed data structure. But its security is amplified significantly by the decentralized nature of blockchain networks. Every full node on the network maintains its own independent copy of the State Trie. This means there is no single copy that an attacker can target.
If someone were to modify the State Trie on their local node, say, giving themselves a larger balance, that change would immediately be detected when their node tries to communicate with the rest of the network. The root hash on their modified trie would not match the root hash that every other node calculated. Their version of events would simply be rejected.
This redundancy across thousands (or even tens of thousands) of nodes is what makes the State Trie’s security model work at scale. It is not enough to hack one computer or one database. You would need to simultaneously alter the State Trie on a majority of the network’s nodes, which is computationally and economically unfeasible.
Enterprises exploring how to use blockchain for internal and external operations often find that this decentralized state management is one of the strongest arguments in favor of adoption. If you are evaluating blockchain for your business, our enterprise blockchain applications guide walks through the most common use cases and their architectures.
State Trie in the Broader Blockchain Ecosystem
The State Trie does not exist in a vacuum. It is one of several trie structures used in blockchain systems. In Ethereum, for example, there are three main tries:
The Three Main Tries in Ethereum
| Trie Type | What It Stores | Root Hash Location |
|---|---|---|
| State Trie | Account balances, nonces, contract code, and storage | Block header (stateRoot) |
| Transaction Trie | All transactions included in a block | Block header (transactionsRoot) |
| Receipt Trie | Outcome and logs of each transaction | Block header (receiptsRoot) |
All three tries work together to give a complete and verifiable picture of what happened in each block. The State Trie captures the “after” state. The Transaction Trie captures the “what happened.” The Receipt Trie captures the “result.” Together, they form a comprehensive audit trail that anyone can verify independently.
This layered trie system is also relevant when we look at how newer blockchain technologies interact with the physical world. For instance, the convergence of AR, VR, and blockchain in the metaverse raises new questions about how state data will scale as virtual environments generate increasingly complex data sets.
Challenges and Limitations of the State Trie
No system is perfect, and the State Trie has its own set of challenges that developers and blockchain architects continue to address.
State Bloat: As more accounts and smart contracts are created, the State Trie grows larger. On Ethereum, the full state has grown to hundreds of gigabytes. This makes it more expensive to run a full node and increases the time required for state synchronization. Various proposals, including state expiry and statelessness, are being explored to manage this growth.
Computational Overhead: Every time a transaction modifies state data, the trie needs to recompute hashes along the affected path. While this is efficient compared to rehashing the entire dataset, it still adds computational cost that scales with the depth of the trie.
Storage Requirements: Because old states are preserved (to maintain historical verifiability), the total storage footprint keeps increasing. Pruning strategies can reduce this, but they come with tradeoffs in terms of historical data availability.
Complexity for Developers: Working directly with the State Trie requires understanding its specific encoding (RLP in Ethereum), hashing algorithm, and path structure. This adds a learning curve for developers building low-level blockchain tools or custom clients.
Despite these challenges, the core security properties of the State Trie remain solid. The ongoing work in the blockchain community is focused on making the trie more efficient without sacrificing the cryptographic guarantees that make it valuable. If you are building or planning a project that depends on blockchain infrastructure, partnering with an experienced blockchain development company can help you navigate these complexities from the start.
The Future of State Trie Security
Blockchain technology is evolving, and the State Trie is evolving with it. Several developments are shaping the future of how blockchains manage and secure state data.
Verkle Trees: Ethereum’s roadmap includes a transition from Merkle Patricia Tries to Verkle trees. Verkle trees use vector commitments instead of hash-based commitments, which allows for much smaller proofs. This means that verifying state data will require less data transfer, making stateless clients more practical.
State Expiry: Proposals for state expiry would allow the network to archive state data that has not been accessed for a long period. This would reduce the active size of the State Trie while still allowing the data to be recovered if needed.
Sharding: As blockchains explore sharding (splitting the network into parallel processing lanes), each shard will maintain its own State Trie. This introduces new challenges around cross-shard communication and state consistency, but also opens the door to much greater scalability.
These developments show that while the fundamental idea of using a trie-based structure for state management is well-established, the specific implementation continues to be refined to meet the growing demands of blockchain networks.
The State Trie is not just a data structure. It is the mechanism that turns a distributed network of independent computers into a single, trustworthy source of truth. Every hash, every proof, every root recorded in a block header is a statement: this data is accurate, this data has not been tampered with, and anyone can verify it for themselves. That is the foundation on which all blockchain security is built.
Frequently Asked Questions
A Merkle tree is a general data structure where each leaf contains a data hash and each parent contains a combined hash of its children, forming a single root hash. A State Trie is a specific implementation used in blockchain that combines the Merkle tree concept with a Patricia trie structure. While a Merkle tree is used broadly for data verification, the State Trie is purpose-built to store and verify the state of every account on the blockchain, including balances, nonces, contract code, and storage data.
Changing data in the State Trie on a single node is technically possible, but it would have no effect on the network. Any modification would produce a different root hash, which would immediately be detected by other nodes during block validation. For a change to stick, an attacker would need to control the majority of the network’s computing power or stake, which is economically and computationally impractical on established blockchains like Ethereum and Bitcoin.
A simple Merkle tree is efficient for verifying fixed datasets but lacks the ability to quickly insert, update, or look up individual entries by key. Ethereum needs to frequently update account states and look up accounts by their address. The Modified Merkle Patricia Trie adds path compression from the Patricia trie structure and key-based lookups, making it suitable for dynamic state data that changes with every block while still retaining the cryptographic verification benefits of Merkle trees.
When a blockchain forks, the State Trie splits along with it. Each fork maintains its own version of the State Trie from the point of divergence. On the fork that continues as the main chain, the State Trie reflects the state resulting from the accepted block sequence. On the abandoned fork, the trie reflects a different sequence of transactions. Nodes automatically switch to the longest valid chain, discarding the orphaned state and adopting the winning trie version.
Mobile wallets typically run as light clients that do not download the entire blockchain. When they need to check an account balance or verify a transaction, they request a Merkle proof from a full node. This proof contains only the hash values along the path from the specific account to the root of the State Trie. The wallet can then verify this proof against the known root hash in the block header, confirming the data is accurate without needing the full state dataset.
Verkle trees are part of Ethereum’s long-term roadmap and are expected to eventually replace the current Merkle Patricia Trie structure. The main advantage is that Verkle trees produce much smaller proofs, which makes it easier for nodes to verify state data without storing the entire trie. This transition would enable stateless clients and reduce the hardware requirements for running a node, though the core security principle of using a tree-based hash structure for tamper detection will remain the same.
Author

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.







