Ai Overview
In the rapidly evolving landscape of Web3 and decentralized finance, wallet security has emerged as one of the most critical concerns for individuals and organizations alike. 8 billion lost to cryptocurrency wallet hacks and exploits in 2023 alone, the need for robust security solutions has never been more urgent. Imagine a business checking account where any check over $10,000 requires signatures from at least two of the three company executives.
Key Takeaways
- Enhanced Security: Multisignature wallets eliminate single points of failure by requiring multiple approvals for transactions, protecting against hacks and insider threats
- Flexible Governance: Customizable M-of-N signature models (2-of-3, 3-of-5, etc.) enable tailored security for personal, business, and DAO treasury management
- Enterprise Adoption: Major crypto exchanges and Web3 organizations rely on multisignature wallet technology for custody and treasury protection
- Recovery Options: Distributed key management provides backup solutions when individual signers lose access to private keys
- Transparent Compliance: On-chain approval processes create auditable trails for institutional investors and regulatory compliance
1. Introduction to Multisignature Wallets in Blockchain
In the rapidly evolving landscape of Web3 and decentralized finance, wallet security has emerged as one of the most critical concerns for individuals and organizations alike. With over $3.8 billion lost to cryptocurrency wallet hacks and exploits in 2023 alone, the need for robust security solutions has never been more urgent. Traditional single-signature wallets, while convenient, expose users to catastrophic risks when private keys are compromised through phishing attacks, malware, or simple human error.
Based on our 8+ years of experience securing blockchain assets for enterprises and high-net-worth individuals, we’ve witnessed firsthand how single-key failures can devastate businesses and erode trust in the crypto ecosystem. The rise of insider risks, coordinated crypto hacking attempts, and sophisticated social engineering attacks has made it clear that relying on a single private key for asset custody is no longer acceptable for serious blockchain operations.
This is where multisignature wallets in blockchain technology provide a transformative solution. By distributing control across multiple parties and requiring consensus for transaction execution, multisignature wallets fundamentally restructure the trust model of digital asset custody. They eliminate single points of failure while enabling transparent, verifiable governance that aligns perfectly with the decentralized ethos of blockchain technology.
Throughout this comprehensive guide, we’ll explore how multisignature wallets work, why they’re essential for modern blockchain security, and how to implement them effectively for various use cases from personal holdings to enterprise treasury management.
2. What Is a Multisignature Wallet?
A multisignature wallet, often abbreviated as “multisig,” is a type of digital wallet that requires multiple private keys to authorize and execute blockchain transactions. Unlike traditional single-signature wallets where one private key grants complete control, a multisignature wallet distributes authority among multiple participants who must collectively approve transactions.
To understand this concept, think of a crypto wallet like a joint bank account that requires multiple signatures. Imagine a business checking account where any check over $10,000 requires signatures from at least two of the three company executives. No single person can unilaterally move funds, providing protection against fraud and ensuring accountability. The same principle applies to multisignature wallets in the blockchain ecosystem.
Single-Signature vs Multisignature Wallets
Single-Signature Wallet: One private key controls all funds. If that key is lost or compromised, assets are permanently inaccessible or stolen. Think of it as having a single key to a safe—convenient but risky.
Multisignature Wallet: Multiple private keys are required to authorize transactions. For example, in a 2-of-3 multisignature wallet, any two of three designated keyholders must approve a transaction. This provides redundancy and security through distributed control.
The beauty of multisignature wallet technology lies in its flexibility and customization. Organizations can configure multisignature wallets to match their specific security requirements and governance structures, whether that means requiring unanimous approval from all participants or setting threshold requirements where only a subset of signers is needed.
3. How Multisignature Wallets Work in Blockchain
Understanding the technical architecture of multisignature wallets helps appreciate their security advantages. At the core, multisignature wallet functionality relies on cryptographic signature schemes that combine multiple public-private key pairs to create a single wallet address with distributed control.[1]
When a multisignature wallet is created, multiple public keys are registered as authorized signers. The wallet’s smart contract or script defines the signature threshold—the minimum number of signatures required to execute transactions. Each signer retains their private key independently, and the wallet remains secure as long as the threshold number of keys stays protected.
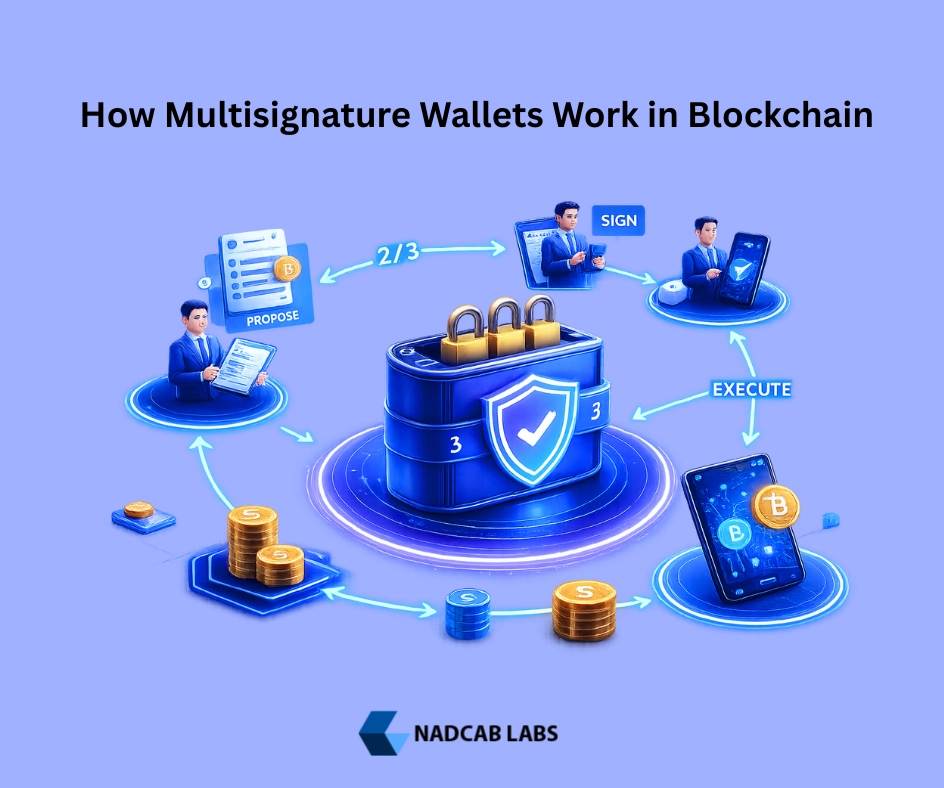
Transaction Lifecycle in a Multisignature Wallet
- Transaction Proposal: One signer initiates a transaction by creating a proposal with details like recipient address, amount, and any additional parameters
- Signature Collection: Other authorized signers review the proposed transaction and digitally sign it with their private keys if they approve
- Threshold Verification: The multisignature wallet’s smart contract verifies that the minimum required number of valid signatures has been collected
- Execution: Once the signature threshold is met, the transaction is broadcast to the blockchain network and executed
- Confirmation: The transaction is confirmed and permanently recorded on the blockchain with a transparent record of all approving signers
Common signature models used in multisignature wallet implementations include:
2-of-3 Configuration: This popular setup involves three keyholders where any two must approve transactions. It’s ideal for small teams or partnerships, providing redundancy if one key is lost while maintaining strong security. For example, a crypto startup might distribute keys among three co-founders, requiring two signatures for treasury transactions.
3-of-5 Configuration: Five designated signers with a requirement for three approvals. This model suits larger organizations or DAOs that need broader consensus while still allowing operations to continue if some signers are temporarily unavailable. Many Web3 projects use this structure for their treasury management.
Enterprise Governance Structures: Large institutions often implement complex multisignature wallets with configurations like 5-of-9 or even 7-of-11, reflecting their organizational hierarchies and compliance requirements. These setups ensure that multiple departments or roles must coordinate before executing significant transactions.
4. Why Multisignature Wallets in Blockchain Are More Secure
The security advantages of multisignature wallets stem from their fundamental design principle: distributed control. By requiring multiple independent approvals, these wallets create multiple layers of protection that address the most common attack vectors in cryptocurrency security.
| Security Threat | Single-Signature Risk | Multisignature Protection |
|---|---|---|
| Private Key Compromise | Complete loss of funds if key is stolen or hacked | Attacker needs multiple keys; single compromise doesn’t grant access |
| Phishing Attacks | Victim unknowingly signs malicious transaction | Additional signers review and reject suspicious transactions |
| Insider Fraud | Single authorized person can steal all funds | Requires collusion among multiple parties; transparent audit trail |
| Malware/Keyloggers | Compromised device exposes complete wallet control | Different signers use different devices; malware on one doesn’t breach wallet |
| Physical Coercion | Holder can be forced to transfer all assets | Single signer can’t complete transaction; coercion becomes impractical |
Elimination of Single Point of Failure: The most significant security advantage of multisignature wallets is the complete removal of single points of failure. In traditional custody models, whether it’s an exchange hot wallet or an individual’s hardware wallet, one compromised key means total loss. Multisignature architecture ensures that no single compromise can drain the wallet, dramatically reducing the attack surface.
Protection Against Private Key Compromise: Even if an attacker successfully steals one private key—through malware, social engineering, or physical theft—they still cannot execute transactions without obtaining additional keys from other signers. This makes multisignature wallets exponentially more secure than single-key alternatives, especially for high-value holdings.
Defense Against Insider Fraud: Our experience working with enterprises has shown that insider threats represent one of the most dangerous security challenges. A multisignature wallet inherently prevents any single employee, contractor, or partner from unilaterally accessing funds. This protection extends beyond malicious intent to include preventing honest mistakes that could result in irreversible losses.
Reduced Risk from Phishing and Malware: Sophisticated phishing campaigns that trick users into signing malicious transactions become much less effective with multisignature wallets. Even if one signer is deceived, additional signers reviewing the transaction details will likely identify the fraud before it’s executed, creating a human verification layer that single-signature wallets lack.
5. Types of Multisignature Wallets in Blockchain

The multisignature wallet ecosystem has evolved to serve diverse needs across different user segments and organizational structures. Understanding the various types helps in selecting the right solution for specific use cases.
Personal Multisignature Wallets: Individual users concerned about security can deploy multisignature wallets to protect their personal crypto holdings. A common approach involves distributing keys across multiple hardware wallets stored in different physical locations, or sharing control with trusted family members. This provides robust protection against loss or theft while maintaining personal sovereignty over assets.
Business and Enterprise Multisig Wallets: Companies operating in the Web3 space rely heavily on multisignature wallets for corporate treasury management. These implementations typically feature role-based access control where executives, financial officers, and board members hold different keys. Transaction approval workflows can mirror traditional corporate governance structures, ensuring financial controls translate effectively to the blockchain environment.
DAO and Treasury Multisignature Wallets: Decentralized Autonomous Organizations use multisignature wallets to manage community treasuries worth millions or even billions of dollars. DAO multisig setups often involve elected council members or trusted community representatives who collectively safeguard and deploy resources according to governance proposals. This model has become the standard for DeFi protocols and NFT projects managing community funds.
Custodial vs Non-Custodial Multisig Models: The multisignature wallet landscape includes both custodial services where third parties hold some keys, and fully non-custodial solutions where all keys remain under direct user control. Custodial multisig services offer convenience and recovery options but introduce counterparty risk, while non-custodial security model implementations maximize sovereignty at the cost of placing full responsibility on keyholders.
6. Key Benefits of Using Multisignature Wallets
Beyond the core security advantages, multisignature wallets provide numerous operational and governance benefits that make them attractive for both personal and institutional use.
Shared Ownership and Control: Multisignature wallets enable true shared ownership of digital assets without requiring trust in any single party. For partnerships, joint ventures, or married couples managing crypto assets together, multisig provides a technical solution that mirrors legal joint ownership arrangements. This shared control model prevents disputes and ensures all parties have visibility into asset management.
Transparent On-Chain Approval Process: Every transaction from a multisignature wallet is permanently recorded on the blockchain along with evidence of which signers approved it. This creates an immutable audit trail that provides transparency for stakeholders, regulators, and auditors. Organizations can easily prove who authorized specific transactions and when, meeting corporate governance requirements.
Better Compliance and Audit Readiness: From our extensive work with regulated entities, we’ve found that multisignature wallets significantly simplify compliance obligations. The multi-party approval process aligns with financial industry requirements for dual control and segregation of duties. External auditors can verify transaction approval patterns and ensure proper internal controls are functioning, which is particularly valuable for companies undergoing financial audits or preparing for regulatory examination.
Improved Recovery Options for Lost Keys: One of the most practical benefits of multisignature wallets is enhanced key recovery. If one signer loses their private key, the wallet remains fully functional using the remaining keys, and a new signer can be added to replace the lost key. This prevents the catastrophic permanent loss scenarios that plague single-signature wallets, where losing the only private key means losing all funds forever.
7. Common Use Cases of Multisignature Wallets in Blockchain
Real-world adoption of multisignature wallet technology spans numerous applications across the cryptocurrency ecosystem. Understanding these use cases illustrates the versatility and importance of multisig solutions.
Crypto Exchanges and Custody Platforms: Major cryptocurrency exchanges use multisignature wallets to secure customer funds held in cold storage. By distributing keys among multiple security officers and requiring several approvals for withdrawals, exchanges protect billions of dollars in assets from both external attacks and internal fraud. This architecture has become a fundamental requirement for any serious custody operation.
DAO Treasury Management: Decentralized Autonomous Organizations leverage multisignature wallets as their primary treasury management tool. Popular DAOs managing hundreds of millions in assets typically use multisig councils where elected members collectively control spending. This structure provides security while maintaining decentralized governance, allowing communities to fund proposals and manage resources without centralized control.
Web3 Startups and Project Funds: Blockchain startups raising significant capital through token sales or VC investments universally adopt multisignature wallets for treasury management. Distributing keys among founders, investors, and advisors ensures no single party can misappropriate funds, building trust with stakeholders and demonstrating responsible financial stewardship.
Family Offices and Institutional Investors: High-net-worth individuals and institutional investors entering the cryptocurrency market prioritize multisignature wallet solutions for asset custody. The ability to implement familiar governance structures with multiple approvers, combined with the enhanced security profile, makes multisig the only acceptable option for serious institutional capital.
| Use Case | Typical Configuration | Primary Benefit |
|---|---|---|
| Exchange Cold Storage | 5-of-7 or higher | Maximum security for customer funds |
| DAO Treasury | 3-of-5 council | Decentralized governance with security |
| Startup Treasury | 2-of-3 or 3-of-4 | Founder protection and investor oversight |
| Personal Holdings | 2-of-3 | Loss prevention and family backup |
| Institutional Investment | 4-of-6 or higher | Compliance and audit trail |
8. Multisignature Wallets vs MPC Wallets vs Smart Contract Wallets
The blockchain wallet security landscape includes several competing technologies that address similar problems through different technical approaches. Understanding the distinctions helps in choosing the right solution.
| Feature | Multisignature Wallets | MPC Wallets | Smart Contract Wallets |
|---|---|---|---|
| Architecture | Multiple full keys, threshold signatures | Distributed key shares, never assembled | Programmable logic on-chain |
| Transparency | Fully visible on-chain | Off-chain computation | Transparent smart contract code |
| Transaction Costs | Moderate gas fees | Lower fees (single signature) | Higher gas costs |
| Recovery Options | Replace lost signers with remaining keys | Reconstruct from threshold shares | Programmable social recovery |
| Best Use Case | Treasury management, DAOs, enterprises | High-frequency trading, custodial services | Consumer wallets, advanced automation |
Core Architectural Differences: Multisignature wallets use complete, independent private keys held by different signers, with transaction approval happening on-chain through signature verification. MPC (Multi-Party Computation) wallets distribute a single private key as encrypted shares among multiple parties who collaboratively sign transactions without ever reconstructing the full key. Smart contract wallets replace traditional key-based security with programmable on-chain logic that can implement complex rules and recovery mechanisms.
When Multisig is the Better Choice: Multisignature wallets excel when transparency and auditability are paramount. The on-chain approval process provides clear evidence of who authorized each transaction, making multisig ideal for DAOs, enterprise treasuries, and any situation requiring compliance or public accountability. The simplicity and battle-tested nature of multisignature wallet technology also provides confidence for conservative institutions entering the space.
When MPC or Account Abstraction Fits Better: MPC wallets suit scenarios requiring frequent transactions where gas efficiency matters, such as exchange operations or high-frequency trading. Smart contract wallets (account abstraction) work best for consumer applications where advanced features like social recovery, gas sponsorship, or automation justify the complexity. However, these alternatives trade off the transparency and proven security model that makes multisignature wallets trusted for high-stakes custody.
9. Supported Blockchains for Multisignature Wallets
Multisignature wallet support varies significantly across different blockchain networks, with implementation approaches ranging from native protocol features to smart contract solutions.[2]
Ethereum Multisignature Wallets: Ethereum’s smart contract capabilities enable sophisticated multisignature wallet implementations. Popular solutions like Gnosis Safe (now Safe) have become industry standards, offering flexible M-of-N configurations with user-friendly interfaces. Ethereum’s multisig implementations benefit from the network’s mature tooling ecosystem and extensive security auditing.
BNB Chain and Polygon Support: EVM-compatible chains like BNB Chain and Polygon support the same multisignature wallet smart contracts as Ethereum, providing lower transaction costs for multisig operations. Many organizations deploy their multisignature wallets on these Layer 1 alternatives or sidechains to reduce gas expenses while maintaining equivalent security guarantees.
Bitcoin Multisig Architecture: Bitcoin pioneered multisignature functionality at the protocol level using P2SH (Pay-to-Script-Hash) and later SegWit multisig formats. Bitcoin’s native multisig support offers proven security but with more limited flexibility compared to smart contract implementations. Nevertheless, Bitcoin multisignature wallets remain the gold standard for long-term cold storage of the world’s most valuable cryptocurrency.
Layer-2 and Cross-Chain Considerations: Layer-2 scaling solutions like Arbitrum and Optimism support Ethereum-compatible multisignature wallets with dramatically reduced transaction costs. Cross-chain multisig management presents challenges, as key sets and approval processes must be coordinated across different networks, though emerging solutions are beginning to address this complexity.
10. Security Best Practices for Multisignature Wallets
Even with inherent security advantages, multisignature wallets require careful configuration and operational discipline to maximize their protective benefits. Our years of experience deploying enterprise multisig solutions have identified critical best practices.
Key Distribution Strategy: The security of a multisignature wallet depends critically on how keys are distributed among signers. Keys should be spread across different individuals, organizations, and geographic locations to prevent coordinated compromise. For high-value wallets, we recommend distributing keys across multiple jurisdictions to provide protection against localized threats or legal actions.
Avoiding Signer Centralization: A common mistake is distributing multiple keys to the same person or storing them in the same location “for convenience.” This defeats the entire purpose of multisignature wallets. Each key should have a truly independent custodian, using different hardware devices, different physical locations, and different security procedures. Geographic and organizational diversity among signers creates resilience against both technical attacks and human coordination failures.
Hardware Wallet Integration: Every signer in a multisignature wallet should use a hardware wallet to store their private key. Hardware devices provide protection against malware and remote attacks that could compromise keys stored on internet-connected computers. Combining multisignature architecture with hardware wallet security creates multiple layers of defense that are extraordinarily difficult to breach.
Emergency Signer Replacement Planning: Organizations must establish clear procedures for replacing signers when keys are lost, compromised, or when personnel changes occur. This includes maintaining secure documentation of the multisignature wallet configuration, backup communication channels among signers, and pre-authorized replacement procedures that don’t require the compromised key for execution.
Critical Security Reminder
Never store multiple multisignature wallet keys in the same location, even temporarily. The security model fundamentally relies on geographic and organizational separation of keys. A multisignature wallet with co-located keys is no more secure than a single-signature wallet.
11. Challenges and Limitations of Multisignature Wallets
While multisignature wallets provide substantial security benefits, they introduce operational complexities and limitations that users must understand and manage effectively.
Slower Transaction Execution: The need to collect multiple signatures inevitably slows transaction execution compared to single-signature wallets. What takes seconds with a single key might require hours or days with a multisignature wallet, especially if signers are in different time zones or have limited availability. This latency can be problematic for time-sensitive operations or when rapid market responses are needed.
Coordination Between Signers: Effective multisignature wallet operation requires reliable communication channels among signers. Organizations need established procedures for transaction review, approval workflows, and emergency decision-making. The human coordination overhead increases with the number of signers, and miscommunication can lead to delayed transactions or operational disruptions.
Gas Costs and Contract Complexity: Smart contract-based multisignature wallets consume more gas than simple transfers due to the additional on-chain logic required for signature verification and execution. For Ethereum mainnet operations, these costs can be significant, particularly during network congestion. The complexity of multisig contracts also increases the attack surface and requires more thorough auditing to ensure security.
UX Issues for Non-Technical Users: Multisignature wallet interfaces remain less intuitive than consumer wallet applications. The concepts of transaction proposals, signature collection, and threshold requirements confuse many users. Educational overhead and technical support requirements are substantially higher for multisig implementations, which can hinder adoption among less technical stakeholders.
12. Real-World Examples of Multisignature Wallets in Action
Examining real implementations demonstrates how multisignature wallets function in practice and highlights their value across different contexts.
Case Study: DAO Treasury Protection
A prominent DeFi protocol managing a $200 million treasury implemented a 4-of-7 multisignature wallet with council members distributed across different countries. When one council member’s credentials were phished in a sophisticated attack, the attacker attempted to propose a malicious transaction draining the treasury.
The multisignature wallet architecture prevented any loss because:
- The compromised signer could only propose transactions, not execute them
- Other council members reviewing the proposal immediately identified suspicious recipient addresses
- The malicious proposal was rejected before reaching the 4-signature threshold
- The compromised signer’s key was replaced without interrupting treasury operations
This incident demonstrated how multisignature wallet security extends beyond technical protections to include human review processes that catch sophisticated attacks.
Exchange Cold Wallet Architecture: Major cryptocurrency exchanges secure customer funds using complex multisignature wallet configurations. A typical setup involves 6-of-9 multisig where keys are distributed among security officers, executives, and third-party custodians across multiple geographic locations. Some exchanges implement time delays on large withdrawals, requiring signatures to be collected over 24-48 hours to prevent hasty decisions during emergencies. This architecture has proven effective in preventing both external hacks and insider theft.
Startup Fund Governance Workflow: A blockchain startup that raised $15 million uses a 2-of-3 multisignature wallet where keys are held by the CEO, CTO, and lead investor. All operational expenses require approval from any two keyholders, ensuring oversight without giving any single party unilateral control. The arrangement provides investor protection while allowing the founding team operational flexibility. When the startup needed to make payroll during a period when the CEO was traveling without internet access, the CTO and investor could approve the transaction, preventing any disruption.
13. How to Choose the Right Multisignature Wallet Setup
Selecting appropriate parameters for a multisignature wallet requires balancing security requirements, operational efficiency, and stakeholder relationships. The right configuration depends on your specific context and risk profile.
Number of Signers: More signers generally provide better security but increase coordination overhead. For personal use, 2-3 signers often suffice. Small businesses typically use 3-5 signers. Large organizations or high-value DAOs might employ 7-11 signers to ensure distributed control and prevent any small group from dominating decisions. Consider that each additional signer adds complexity to transaction approval processes.
Approval Thresholds: The signature threshold should be high enough to prevent unauthorized transactions but low enough to maintain operational efficiency. A 51% threshold (such as 3-of-5) provides reasonable security while allowing transactions to proceed even if some signers are unavailable. Higher thresholds like 66% or 75% offer stronger protection but risk operational paralysis if multiple signers become unavailable simultaneously.
Role-Based Permissions: Advanced multisignature wallet implementations support different approval requirements for different transaction types. For example, small routine transactions might require 2-of-5 signatures while large transfers require 4-of-5. Time-locked transactions or specific contract interactions might have custom approval rules. This flexibility allows organizations to balance security with operational efficiency.
Business vs Personal Requirements: Personal multisignature wallets prioritize recovery and inheritance planning, often involving family members or trusted advisors. Business implementations focus on segregation of duties, audit trails, and compliance with corporate governance policies. Understanding your primary objectives—whether security, governance, compliance, or recovery—guides configuration decisions.
14. Future of Multisignature Wallets in Blockchain Security
The multisignature wallet ecosystem continues evolving with new technologies and use cases emerging that will shape the future of blockchain asset custody.
Integration with Account Abstraction: Ethereum’s ERC-4337 account abstraction standard enables combining multisignature security with programmable wallet features like gas sponsorship, batched transactions, and customizable validation logic. Future multisignature wallets will offer enhanced user experiences while maintaining the security benefits of threshold signatures, blurring the line between multisig and smart contract wallet approaches.
Automation and Policy-Based Approvals: Emerging solutions integrate AI and automated policy enforcement with multisignature wallets. For example, routine transactions meeting predefined criteria might auto-approve with reduced signature requirements, while unusual patterns trigger enhanced review. This automation preserves security while reducing the operational burden of manual approval for every transaction.
Enterprise Adoption Trends: Traditional financial institutions increasingly recognize multisignature wallets as the only viable custody model for institutional cryptocurrency holdings. We’re seeing major banks, asset managers, and corporations implementing multisig infrastructure for their blockchain operations. This enterprise adoption will drive development of more sophisticated governance features and better integration with existing financial systems.
Regulatory Alignment and Compliance: Regulators worldwide are developing custody standards for digital assets, and many proposed frameworks explicitly reference multisignature wallets as a recommended practice. Future regulations will likely mandate certain multisig configurations for licensed custodians and financial institutions operating in the crypto space, cementing the technology’s role in compliant asset custody.
15. Conclusion: Are Multisignature Wallets in Blockchain Worth It?
After exploring multisignature wallet technology from technical architecture through practical implementation, the value proposition is clear. For anyone managing significant cryptocurrency holdings—whether personal wealth, business treasury, or community funds multisignature wallets represent a fundamental security upgrade that dramatically reduces risk.
The security benefits speak for themselves: elimination of single points of failure, protection against key compromise, defense against insider fraud, and resilience to the full spectrum of attack vectors that plague single-signature wallets. These advantages aren’t theoretical; they’ve been proven through countless real-world incidents where multisignature wallet architecture prevented what would have been catastrophic losses.
Beyond security, multisignature wallets provide governance structures that align with organizational needs and compliance requirements. The transparent on-chain approval process, ability to distribute control among stakeholders, and built-in accountability mechanisms make multisig essential infrastructure for professional blockchain operations.
Who Should Use Multisignature Wallets: Multisignature technology is appropriate for cryptocurrency exchanges, DeFi protocols, DAO treasuries, Web3 startups, traditional companies with crypto holdings, high-net-worth individuals, family offices, and anyone else who cannot afford to lose their digital assets. Essentially, if the funds matter enough that losing them would be significant, they should be protected with a multisignature wallet.
The operational challenges—coordination overhead, slower transactions, and user experience friction—are real but manageable with proper planning and tooling. The industry continues developing solutions that reduce these frictions while preserving security benefits. For serious cryptocurrency custody, these challenges are a worthwhile trade-off for the security and governance advantages gained.
Final Thoughts on Long-Term Web3 Asset Protection: As the blockchain ecosystem matures and more value flows into decentralized systems, security practices must evolve accordingly. Single-signature wallets may suffice for small experimental holdings, but they’re inadequate for serious asset custody. Multisignature wallets represent the current state-of-the-art in self-custodied security, and their adoption will only accelerate as individuals and institutions recognize the inadequacy of single-key models.
From our 8+ years of experience implementing blockchain security solutions, we’ve seen multisignature wallet technology prevent numerous disasters and enable organizations to operate with confidence in the crypto space. The technology is mature, battle-tested, and ready for widespread adoption. The question isn’t whether to use multisignature wallets, but rather how to implement them most effectively for your specific needs.
Whether you’re an individual looking to protect life savings, a startup managing investor capital, or an enterprise entering the blockchain space, multisignature wallet technology should be a cornerstone of your security strategy. The peace of mind that comes from distributed control and resilient key management is invaluable in an ecosystem where mistakes are permanent and reversals are impossible.
Build My Crypto wallet Now!
Turn your dream into reality with a powerful, secure crypto wallet built just for you. Start building now and watch your idea come alive!
Frequently Asked Questions
Q1.What are multisignature wallets in blockchain?
Multisignature wallets in blockchain are crypto wallets that require approvals from multiple private keys before a transaction is executed, improving security by eliminating single-key control.
Q2.How do multisignature wallets work?
A multisignature wallet works by collecting a predefined number of digital signatures from authorized signers before allowing funds to move on the blockchain.
Q3.Why are multisignature wallets more secure than regular wallets?
Multisignature wallets reduce the risk of hacks and insider fraud because no single person can access or transfer funds alone, even if one private key is compromised.
Q4.What is an M-of-N multisignature wallet?
An M-of-N multisignature wallet requires M approvals out of N total signers, such as 2-of-3 or 3-of-5, to authorize a blockchain transaction.
Q5.Who should use multisignature wallets in blockchain?
Multisignature wallets are ideal for businesses, DAOs, crypto exchanges, investment groups, and individuals managing high-value digital assets collaboratively.
Q6.Can multisignature wallets be used for personal crypto storage?
Yes, individuals can use multisignature wallets to add added security by splitting signing authority across multiple devices or trusted parties.
Q7.Which blockchains support multisignature wallets?
Multisignature wallets are supported on major blockchains including Bitcoin, Ethereum, BNB Chain, Polygon, and several Layer-2 networks.
Q8.What happens if one multisignature wallet key is lost?
If one key is lost, transactions can still proceed as long as the remaining signers meet the required approval threshold defined in the wallet setup.
Q9.Are multisignature wallets the same as MPC wallets?
No, multisignature wallets rely on multiple on-chain signatures, while MPC wallets split a single private key into encrypted shares managed off-chain.
Q10.What are the limitations of multisignature wallets in blockchain?
Multisignature wallets may involve slower transaction approvals, higher setup complexity, and increased gas costs compared to single-signature wallets.
Explore Services
Related Services
Reviewed by

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.





