Credential schema in Web3 defines the standardized structure for digital credentials in decentralized systems. Think of it as a blueprint that specifies what information a credential should contain and how that information should be formatted. Without standardized schemas, credentials issued by one platform would be meaningless to another, creating isolated identity silos. As the W3C published Verifiable Credentials 2.0 as an official web standard in May 2025, credential schemas have become the backbone of interoperable digital identity across blockchain networks and decentralized applications.[1]
Key Takeaways
- Standardization Foundation: Credential schemas define the data structure, field types, and validation rules for digital credentials in Web3.
- Interoperability Enabler: Schemas allow credentials issued on one platform to be recognized and verified across different applications and networks.
- W3C Standards: The Verifiable Credentials Data Model 2.0 became an official W3C standard in May 2025, providing global consistency.
- Privacy Preservation: Well-designed schemas support selective disclosure, allowing users to share only necessary information.
- Fraud Prevention: Cryptographic signatures tied to schema-compliant credentials make tampering and forgery virtually impossible.
- Enterprise Adoption: Organizations like Microsoft, GS1, and EU governments are implementing credential schemas at scale.
- Format Flexibility: Schemas support multiple formats including JSON-LD, JWT, and SD-JWT for different use cases.
What is Credential Schema in Web3?
A credential schema in Web3 is a structured template that defines the attributes, data types, and validation rules for digital credentials. It acts as a contract between credential issuers and verifiers, ensuring that everyone interprets credential data consistently. When a university issues a digital diploma or a government issues an identity document, the schema determines exactly what fields must be included, what format each field should follow, and how the credential should be cryptographically secured.
The Decentralized Identity Foundation describes credential schemas as data templates specifying which attributes a credential should contain, including field names, types, and interpretation guidelines. This standardization eliminates ambiguity. A “graduation date” field means the same thing whether the credential comes from a university in Germany or Japan.
In practical terms, credential schemas enable the Web3 ecosystem to move from fragmented identity silos toward a unified system where credentials flow seamlessly across applications, platforms, and borders.
Core Components of a Credential Schema
Understanding the building blocks of credential schemas helps developers and organizations implement them effectively in Web3 platform solutions.
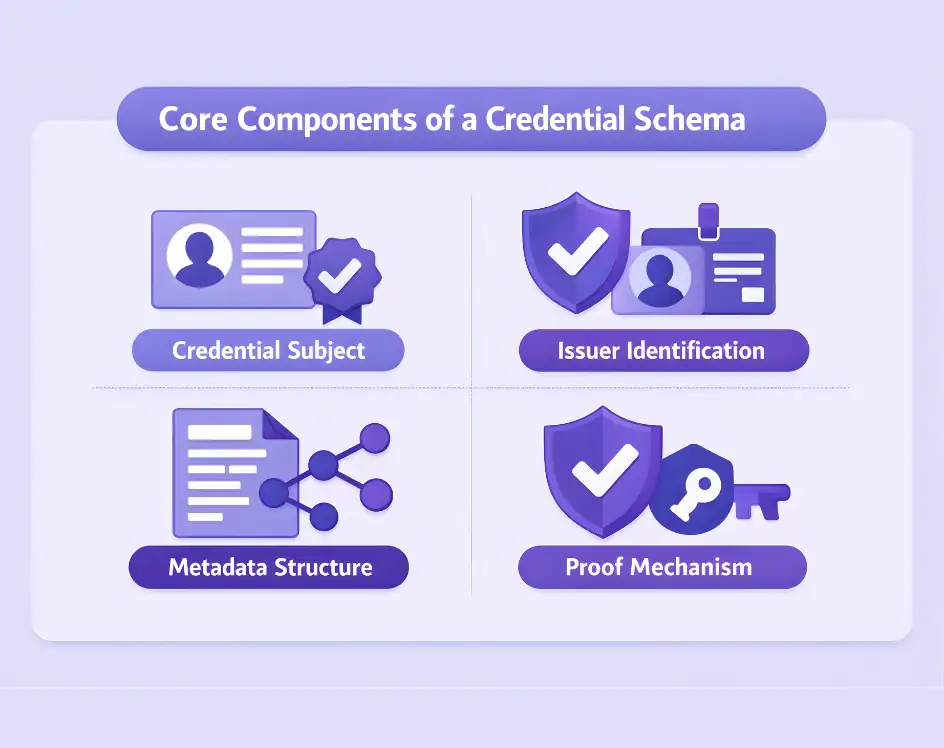
Credential Subject
The credential subject block contains the actual claims about the holder. For an educational credential, this might include degree type, major, graduation date, and institution name. For an employment credential, it could specify job title, employment dates, and company information. The schema defines which fields are required versus optional and what data types each field accepts.
Issuer Identification
Every schema-compliant credential includes information identifying who issued it. This typically uses a Decentralized Identifier (DID) that points to the issuer’s cryptographic keys. The issuer section enables verifiers to confirm the credential came from a legitimate source.
Metadata Structure
Credential metadata includes issuance date, expiration date, credential identifier, and the schema reference itself. This information helps verifiers understand the credential’s context and validity period. Metadata is typically cryptographically signed to prevent tampering.
Proof Mechanism
The proof section contains cryptographic signatures or mathematical proofs that verify the credential’s authenticity and integrity. Depending on the implementation, this could use JSON-LD proofs, JWT signatures, or advanced techniques like BBS+ signatures that enable selective disclosure.
How Credential Schemas Enable Interoperability
Interoperability is the central challenge that credential schemas solve. Without standardization, a credential issued by one system cannot be understood or verified by another. Schemas create a common language for digital identity across the decentralized web.
Cross-Platform Recognition
When credentials follow standardized schemas, a digital diploma issued by a European university can be verified by an employer in Asia using completely different software. The schema ensures both parties interpret the credential identically. The EU’s POTENTIAL pilot, concluded in September 2025 across 19 member states, demonstrated this by successfully verifying credentials issued in one country by service providers in others.[2]
Format Flexibility Within Standards
The W3C Verifiable Credentials standard accommodates multiple data formats while maintaining schema consistency. JSON-LD provides rich semantic context ideal for complex credentials. JWT (JSON Web Tokens) offers simplicity and compatibility with existing enterprise systems. SD-JWT enables selective disclosure for privacy-sensitive applications. Organizations choose formats based on their needs while remaining interoperable through shared schemas.
Ecosystem Convergence
Major identity initiatives are converging on common schema standards. Microsoft Entra Verified ID uses W3C VC and DID standards. The European Digital Identity Wallet mandates OpenID for Verifiable Credentials protocols. The OpenID Foundation demonstrated real-world interoperability in May 2025, bringing together wallets and verifiers across three regions to successfully exchange credentials using standardized schemas.[3]
Types of Credential Schema Formats
Different schema formats serve different purposes. Understanding their strengths helps in selecting the right approach for specific applications.
JSON-LD Based Schemas
JSON-LD (JSON for Linked Data) schemas provide semantic context through vocabulary definitions. This format excels when credentials need to express complex relationships or integrate with semantic web applications. JSON-LD schemas enable rich extensibility, allowing new credential types to reference established vocabularies while maintaining backward compatibility.
JSON Schema
The Verifiable Credentials JSON Schema Specification defines credential structure using standard JSON Schema. This approach is familiar to developers and integrates easily with existing validation tools. JSON Schema provides strict type checking and validation rules that catch malformed credentials before they enter the system.
Domain-Specific Schemas
Certain industries have developed specialized schema standards. ISO 18013-5 defines the schema for mobile driver’s licenses (mDLs). Educational schemas like eduPerson and Open Badges structure academic achievement data. These domain-specific schemas address unique requirements while remaining compatible with broader W3C standards.
Privacy Benefits of Well-Designed Schemas
Credential schemas do more than organize data—they enable sophisticated privacy protections that distinguish Web3 identity from traditional systems.
Selective Disclosure
Modern schemas support revealing only specific fields from a credential. Need to prove you are over 21? Share just the age verification claim without exposing your full birthdate, address, or photo. This capability requires schemas designed with field-level granularity and proof mechanisms like SD-JWT or BBS+ signatures that generate valid proofs for partial credential presentations.
Zero-Knowledge Proofs
Anonymous credentials take privacy further by enabling proofs about credential contents without revealing the contents themselves. A schema might support proving your salary exceeds a threshold without disclosing the exact amount. These advanced cryptographic techniques require schema designs that anticipate such use cases.
Minimized Data Exposure
Traditional identity verification often collects far more data than necessary. Schemas designed for Web3 emphasize minimal disclosure by default. The EU Digital Identity Wallet architecture mandates selective disclosure capabilities, ensuring users share only attributes necessary for each verification request.
Need Custom Credential Schema Implementation?
Designing and implementing credential schemas requires expertise in W3C standards, cryptographic proofs, and blockchain integration. Our team builds compliant, interoperable credential systems for enterprises and platforms.
How Credential Schemas Prevent Fraud
Fraud prevention is a core benefit of schema-based credential systems. The combination of standardized structure and cryptographic security creates credentials that are virtually impossible to forge or manipulate.
Cryptographic Binding
Every schema-compliant credential includes a digital signature created using the issuer’s private key. This signature covers all credential fields defined by the schema. Any modification to the credential, changing a graduation date, altering a job title—invalidates the signature and fails verification.
Issuer Verification
Schemas require credentials to include verifiable issuer identification through DIDs. Verifiers can check that the issuer’s public key matches the signature and that the issuer is authorized to issue that credential type. A fake university cannot issue valid diploma credentials because they lack the cryptographic keys associated with legitimate institutions.
Tamper-Evident Structure
The rigid structure enforced by schemas makes tampering detectable. A credential missing required fields or containing fields with wrong data types fails schema validation before cryptographic checks even begin. This layered approach catches both sophisticated forgery attempts and simple data manipulation.
Implementing Credential Schemas in Web3 Projects
Implementing credential schemas requires careful planning across technical, organizational, and ecosystem dimensions.
Schema Design Phase
Start by identifying credential types needed for your application. Define required versus optional fields based on verification use cases. Consider privacy requirements—will users need selective disclosure? Plan for future extensibility by following W3C vocabulary conventions. Document validation rules for each field.
Technical Integration
Select proof formats based on your ecosystem. JWT works well for enterprises with existing OAuth infrastructure. JSON-LD suits applications requiring rich semantic context. Integrate with consensus mechanisms if credentials require on-chain anchoring. Implement DID resolution for issuer verification. Build or integrate digital wallet support for credential storage.
Testing and Validation
Use W3C test suites to verify compliance with Verifiable Credentials standards. Participate in interoperability plugfests to test cross-platform compatibility. Implement comprehensive schema validation to catch malformed credentials early. Test selective disclosure flows to ensure privacy features work correctly.
Real-World Applications of Credential Schemas
Credential schemas are moving from specification to production across multiple industries.
Education and Certifications
Universities worldwide issue blockchain-anchored diplomas following standardized schemas. Singapore’s OpenCerts has issued over 2 million credentials. RMIT University uses Microsoft Azure and ION blockchain for student-controlled academic credentials. Professional certification bodies use schemas to issue verifiable licenses that employers can check instantly.
Government Identity
Over a dozen US states issue mobile driver’s licenses following the ISO mdoc schema, accepted at TSA PreCheck nationwide. The EU Digital Identity Wallet will require all member states to provide schema-compliant digital identity by 2026. Estonia’s e-Residency program uses verifiable credentials for global business establishment.
Enterprise Applications
Deloitte uses blockchain credentials for professional development verification. Web3 Gaming platforms implement credential schemas for player achievements and reputation. Supply chain systems use schemas to verify product certifications and compliance documents. Financial institutions pilot credential acceptance for faster KYC processes.[4]
Conclusion
Credential schema in Web3 provides the essential standardization layer that makes decentralized identity practical. Without schemas, digital credentials would remain isolated within individual platforms. With schemas, credentials flow freely across applications, organizations, and borders while maintaining security and privacy.
The May 2025 W3C standardization of Verifiable Credentials 2.0 marked a turning point. Enterprises, governments, and developers now have stable specifications to build upon. The EU Digital Identity Wallet mandate creates regulatory pressure driving adoption. Successful interoperability demonstrations prove the technology works at scale.
For organizations building Web3 applications, understanding and implementing credential schemas is no longer optional. Whether issuing educational certificates, verifying professional qualifications, or enabling decentralized authentication, schema-compliant credentials provide the foundation for trustworthy digital identity in the decentralized web.
Frequently Asked Questions
A credential schema is a template defining what information a digital credential must contain, including field names, data types, and validation rules, ensuring all parties interpret credentials consistently.
Schemas enable interoperability by ensuring credentials issued on one platform can be understood and verified by any other platform following the same standard.
Well-designed schemas support selective disclosure, allowing users to reveal only specific credential fields. Advanced schemas enable zero-knowledge proofs that verify claims without exposing data.
The W3C Verifiable Credentials Data Model 2.0, standardized in May 2025, defines how digital credentials should be structured, secured, and exchanged across decentralized systems.
Yes, the W3C standard accommodates multiple formats including JSON-LD and JWT. Interoperability testing has demonstrated credentials in different formats verifying successfully across platforms.
Typically, only schema references and cryptographic proofs go on-chain. Actual credential data stays in user wallets for privacy, with blockchain providing immutable verification anchors.
Author

Aman Vaths
Founder of Nadcab Labs
Aman Vaths is the Founder & CTO of Nadcab Labs, a global digital engineering company delivering enterprise-grade solutions across AI, Web3, Blockchain, Big Data, Cloud, Cybersecurity, and Modern Application Development. With deep technical leadership and product innovation experience, Aman has positioned Nadcab Labs as one of the most advanced engineering companies driving the next era of intelligent, secure, and scalable software systems. Under his leadership, Nadcab Labs has built 2,000+ global projects across sectors including fintech, banking, healthcare, real estate, logistics, gaming, manufacturing, and next-generation DePIN networks. Aman’s strength lies in architecting high-performance systems, end-to-end platform engineering, and designing enterprise solutions that operate at global scale.






